New research shows Microsoft Edge loads all saved passwords into memory in plain text, and Keeper Forcefield is built to protect against exactly this kind of
Updated on March 27, 2025.
Since the introduction of passkeys in 2021, many major companies, such as Apple, Google, Microsoft and Amazon, have started to support them across their platforms. You may have noticed that when creating a new account or updating your account information, you sometimes have the option to enable passkeys as a login method. You might be wondering whether or not you should use them. The answer is yes, you should use passkeys whenever given the option. Not only do they make logging into your accounts easier, but they are also much more secure than traditional passwords.
Continue reading to learn more about passkeys, why passkeys are safer to use and how they differ from passwords.
What is a passkey?
To understand what a passkey is, you need to first understand how passkeys work. A passkey consists of two cryptographic keys: a private key and a public key. The public key is stored with the company where you created your account, while the private key is stored locally on the device you used to set up the passkey (also known as the authenticator). When you log in to an account that has passkeys enabled, the account server will send a challenge to the authenticator, which can be a phone, computer, tablet, browser or password manager.
The authenticator then uses the stored private key to solve the “challenge” and sends a response back to the server. This process is also known as “signing” the data, which proves that you own the private key and verifies your identity. On your end, you simply authenticate using the method you typically use to sign into your device, such as facial recognition, a fingerprint or a PIN.
Are passkeys safer than passwords?
Yes, passkeys are safer to use than passwords. This is not only because passkeys are phishing-resistant, but they are also error-proof. When users generate a passkey, they can’t make mistakes like they do with traditional passwords.
In addition to being phishing-resistant and error-proof, passkeys also support Two-Factor Authentication (2FA) by design. 2FA is a second form of authentication that should be enabled on all online accounts when possible. Unless it’s required, many users don’t enable 2FA on their accounts because it creates an additional step to log in. Since passkeys are tied to the devices they’re generated on, the device acts as the authenticator, making passkeys even more secure than passwords since that device will always be required to log in.
However, because passkeys are tied to the devices they’re generated on, it makes managing them across different operating systems and device types complex. For example, if you use a Windows PC to generate a passkey and you want to log in to that account from your iPhone, you’ll want to use a service that enables you to sync your passkey across devices like a password manager. Without such a service, you’d still need to have the original device with you to authenticate.
The key differences between passkeys and passwords
Here are some of the key differences between passkeys and passwords.
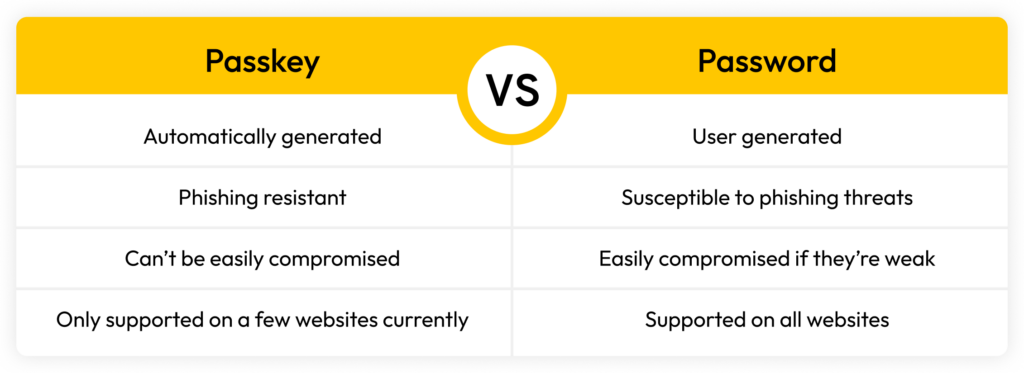
Passkeys are created differently from passwords
When creating passwords, users must follow password best practices so cybercriminals don’t easily crack them. Users must also ensure each password is unique, meaning it isn’t being reused across multiple accounts. Creating strong, unique passwords on your own can be difficult, especially having to remember all the passwords you create. When it comes to passkeys, users don’t have to create anything. All they have to do is generate the passkey for their account and then they can log in using the device from which they generated the passkey.
Passkeys are phishing-resistant, unlike passwords
Phishing is a cyber attack in which cybercriminals pretend to be someone they’re not – like a company, family member or friend – so their targeted victim is persuaded to provide sensitive information. In a phishing attack, cybercriminals often try to get victims to click on a link that takes them to a spoofed website. This phony website is designed to look legitimate so the victim will log in with their account credentials.
With passwords, it’s easy to fall victim to phishing because you might unknowingly enter your username and password into a malicious site designed to steal your credentials. With passkeys, however, cybercriminals can’t trick you into entering your login information on a phishing site, since there’s nothing to enter. This makes passkeys inherently phishing-resistant.
Passwords are easier to compromise than passkeys
For online accounts to be secure, you need to use strong passwords. A strong password is at least 16 characters long and contains uppercase and lowercase letters, numbers and symbols. Strong passwords are also never reused and don’t contain personal information or common dictionary words and phrases. While these are the rules for creating strong passwords, many people don’t follow them and continue to use weak passwords for their online accounts, making them more vulnerable to being compromised.
With passkeys, users don’t have to worry about creating strong passwords or having their accounts compromised if the company they created an account with experiences a data breach. This is because account servers only store the public key part of a passkey; if the server is breached, cybercriminals will only have access to the public key, which is useless without the accompanying private key.
Passkeys are only supported on a few websites
Some websites still don’t support passkeys as a sign-in method, setting them apart from passwords, which are supported on all websites. However, several major websites, such as Apple, Google, PayPal, Best Buy, Adobe, Amazon and Microsoft, do support passkeys. To see which other websites support passkeys, check out our passkeys directory.
Switch to passkeys for better security
While passkeys are considered more secure than passwords, not all websites support them, so you will still have to continue using strong passwords for those online accounts. In addition to a strong password, you should also have 2FA or Multi-Factor Authentication (MFA) enabled. Like 2FA, MFA adds an extra layer of security to your account by requiring that you provide one or more additional authentication factors to your username and password before you can successfully log in.
Keeping your accounts secure with strong passwords or passkeys doesn’t have to be difficult. Password managers like Keeper Password Manager are designed to help you secure your online accounts by storing both passwords and passkeys, making it a seamless experience to log in no matter which method is used.
Start a free 30-day trial of Keeper Password Manager today to see how Keeper can help you manage both your passwords and passkeys.


