Secure remote access to your critical infrastructure with KeeperPAM®
KeeperPAM provides secure, zero-trust remote access to your critical infrastructure, reducing reliance on traditional VPNs and simplifying network complexity.
KeeperPAM provides secure, zero-trust remote access to your critical infrastructure, reducing reliance on traditional VPNs and simplifying network complexity.
Distributed teams, contractors and third-party vendors all require access to critical systems from diverse locations and environments.
Credentials, keys and tokens live on endpoints and in cloud services, often without centralized visibility and control.
VPNs and misconfigured access points create exploitable entry paths that cybercriminals can laterally move to.
Without visibility and control, one mistake can compromise your entire environment and enable privilege escalation.
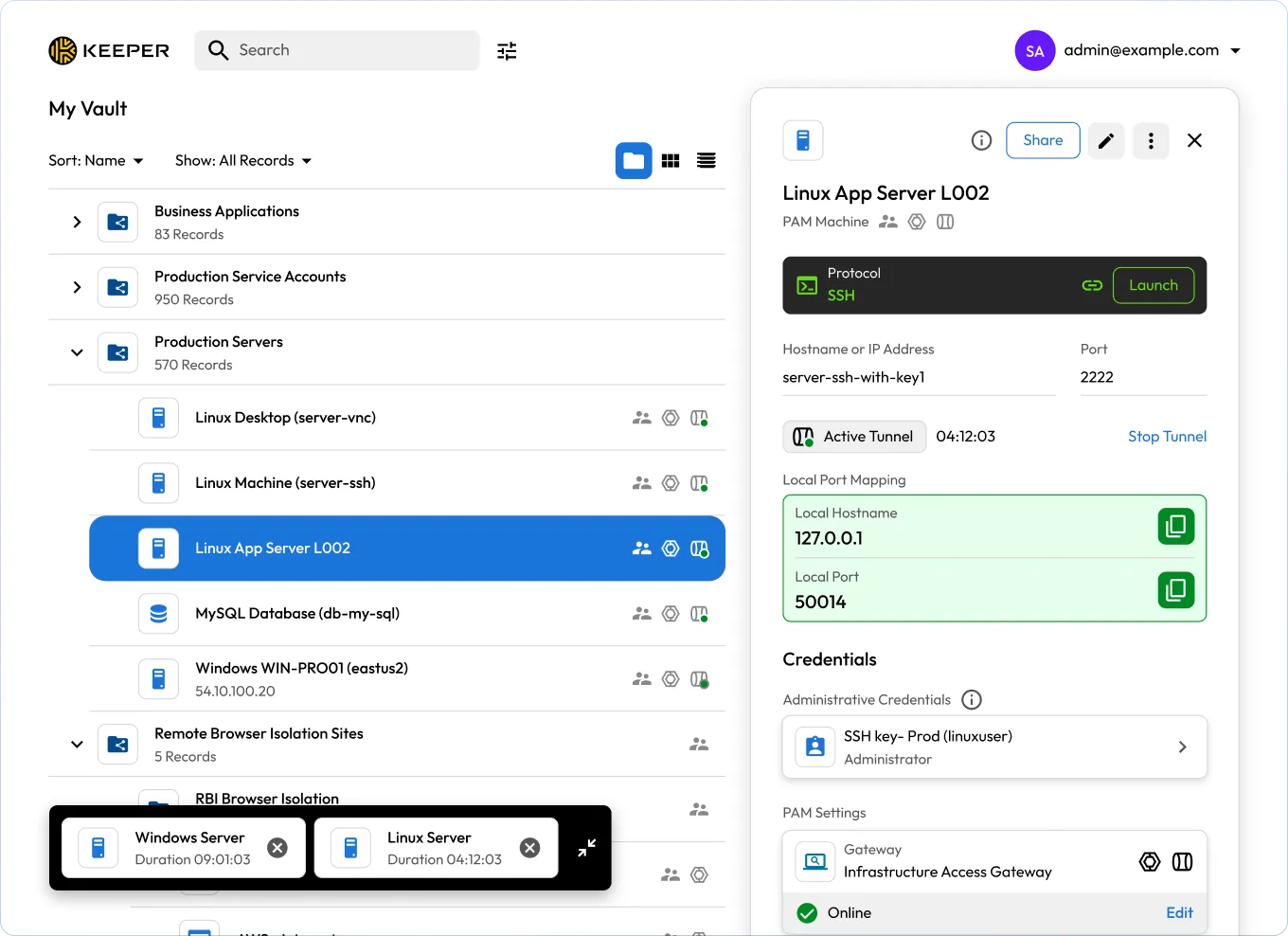
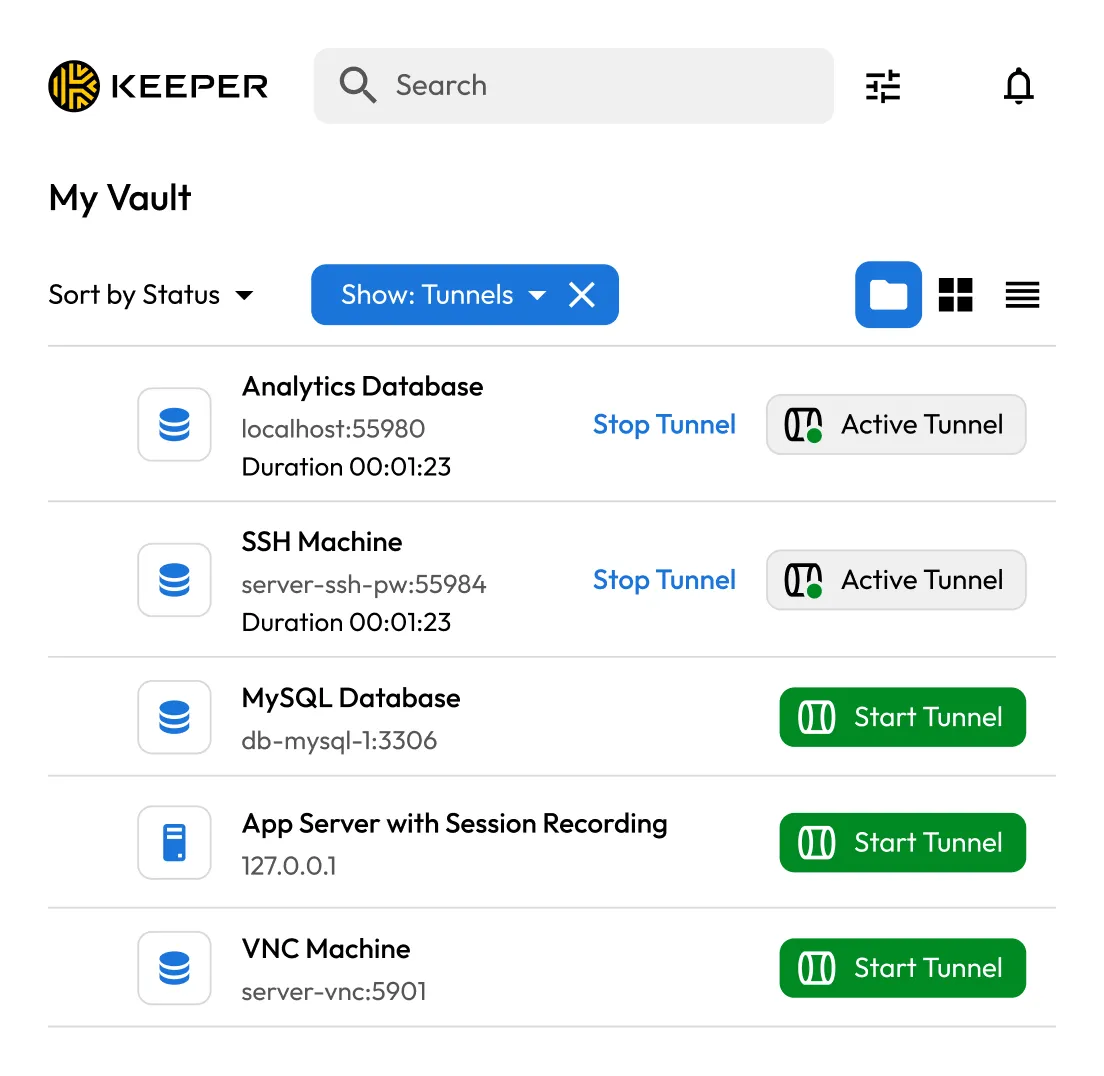
Connect to infrastructure from anywhere based on defined access policies. KeeperPAM establishes outbound-only, end-to-end encrypted tunnels through the Keeper Gateway, enabling secure access to infrastructure without VPNs or inbound firewall changes.
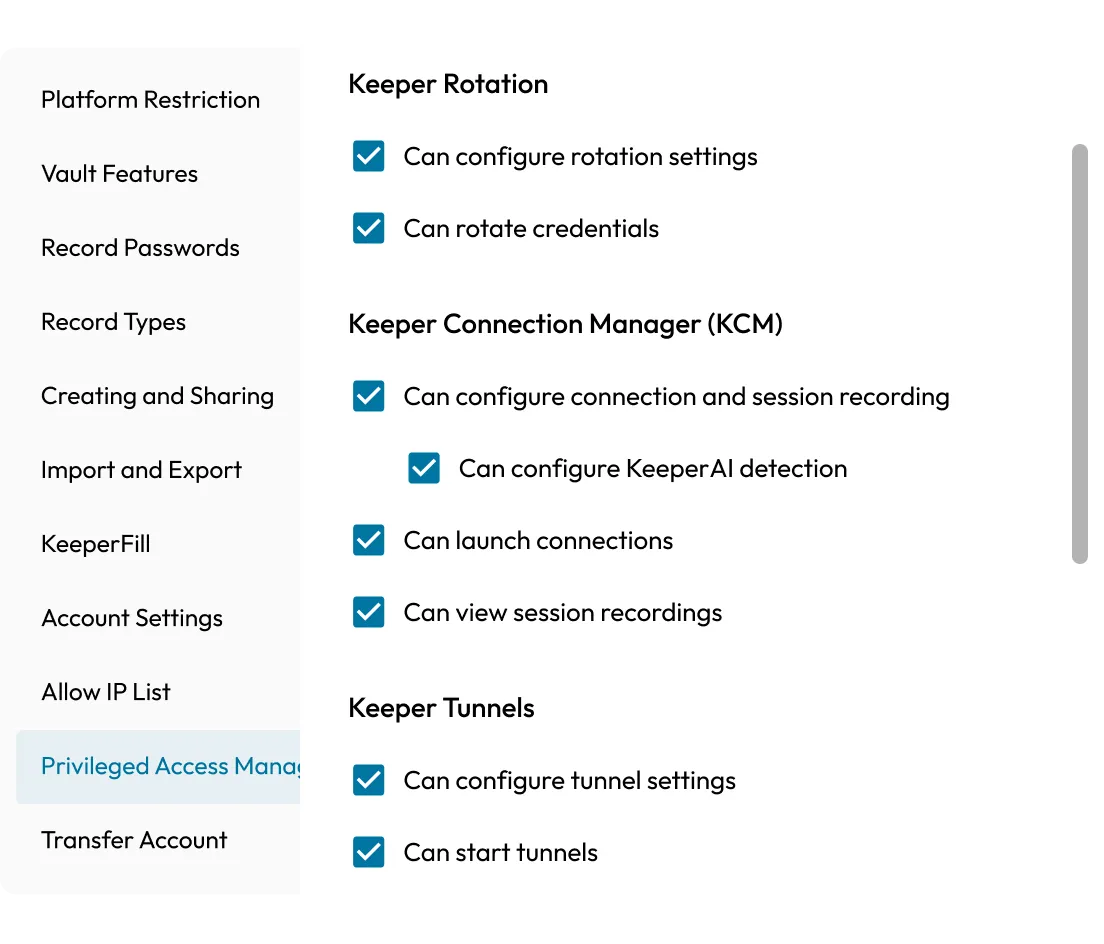
Grant users secure access without ever revealing credentials. KeeperPAM provisions time-limited, policy-enforced sessions through the Keeper Vault, so credentials stay hidden, protected and rotated according to organizational policy.
Access SSH, RDP, VNC, SQL and HTTPS without changing workflows. KeeperPAM supports a wide range of infrastructure, web protocols and databases, so teams can connect using the tools they already know.

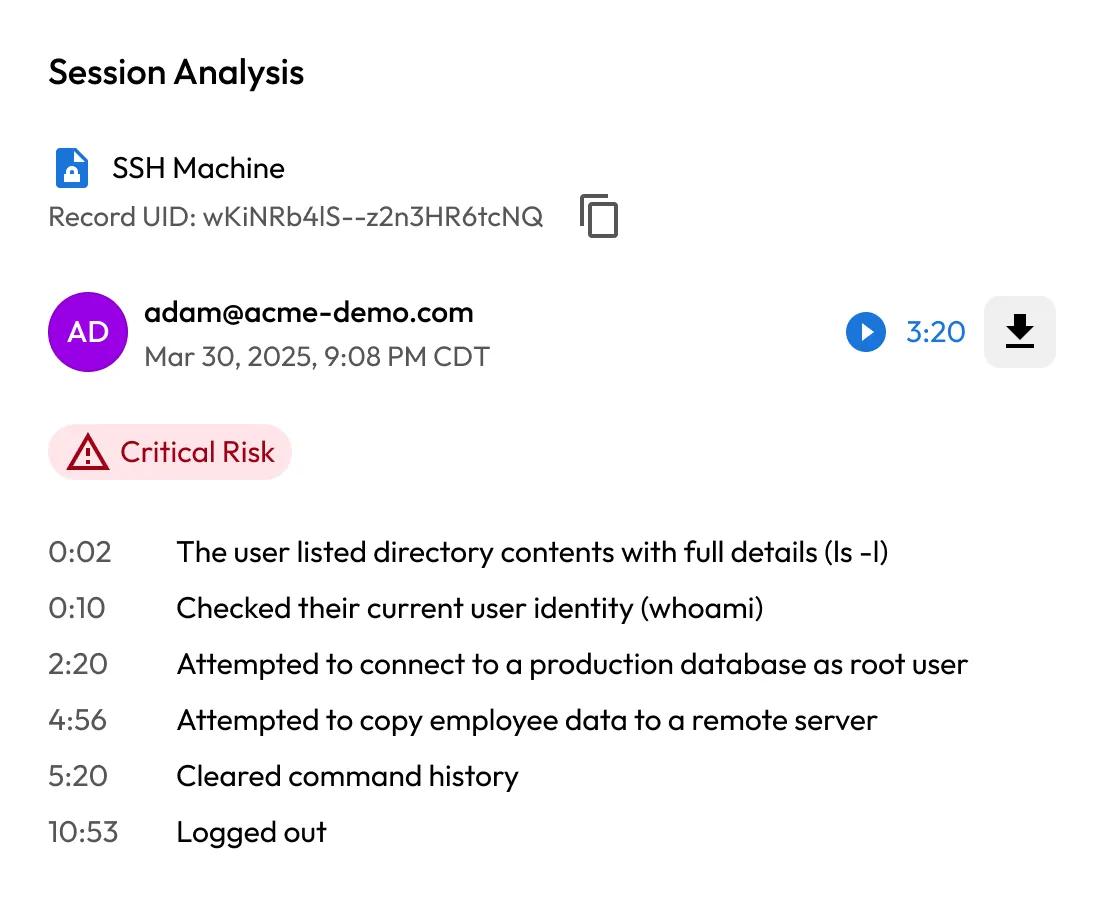
Capture supported screen and keystroke activity across every privileged session. KeeperPAM ensures every action is logged for audit trails, compliance and security investigations.
Secure access across AWS, Azure, on-prem and hybrid workloads. KeeperPAM unifies access control through a single interface, enabling IT and DevOps to manage everything in one place.
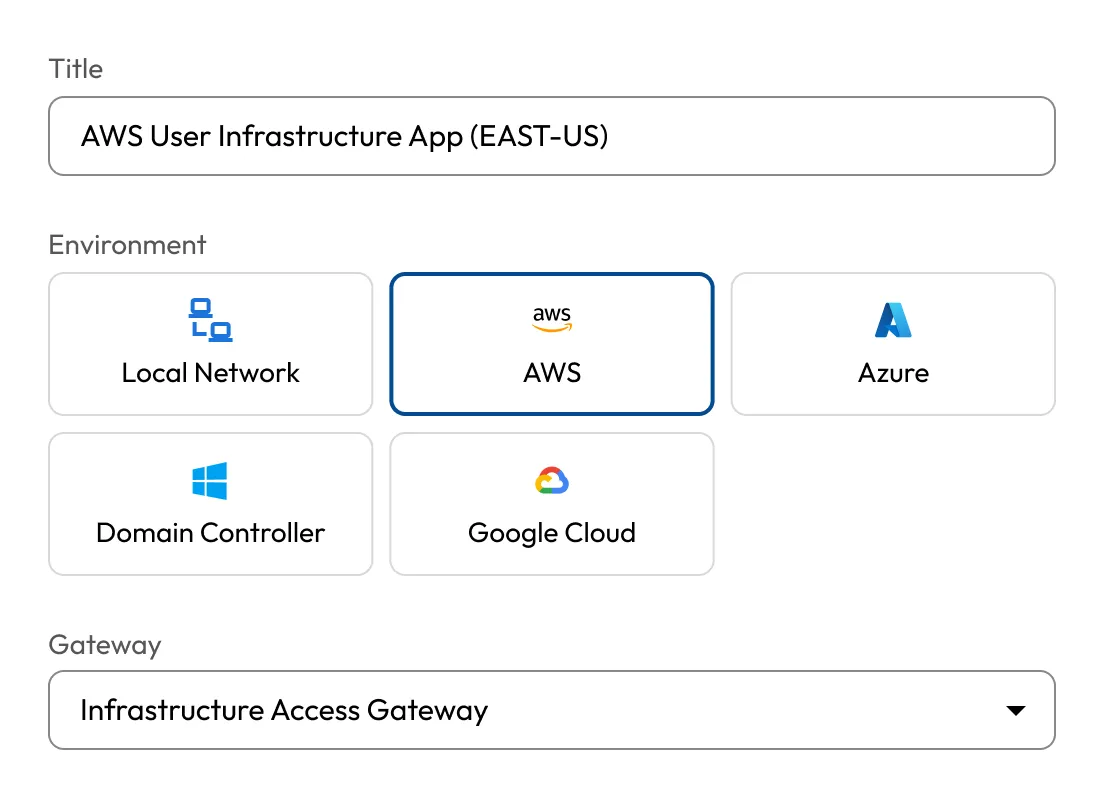

Skip the complexity of legacy PAM deployments. KeeperPAM delivers immediate access to infrastructure through lightweight gateways and a cloud-native model that's easy to scale and manage.
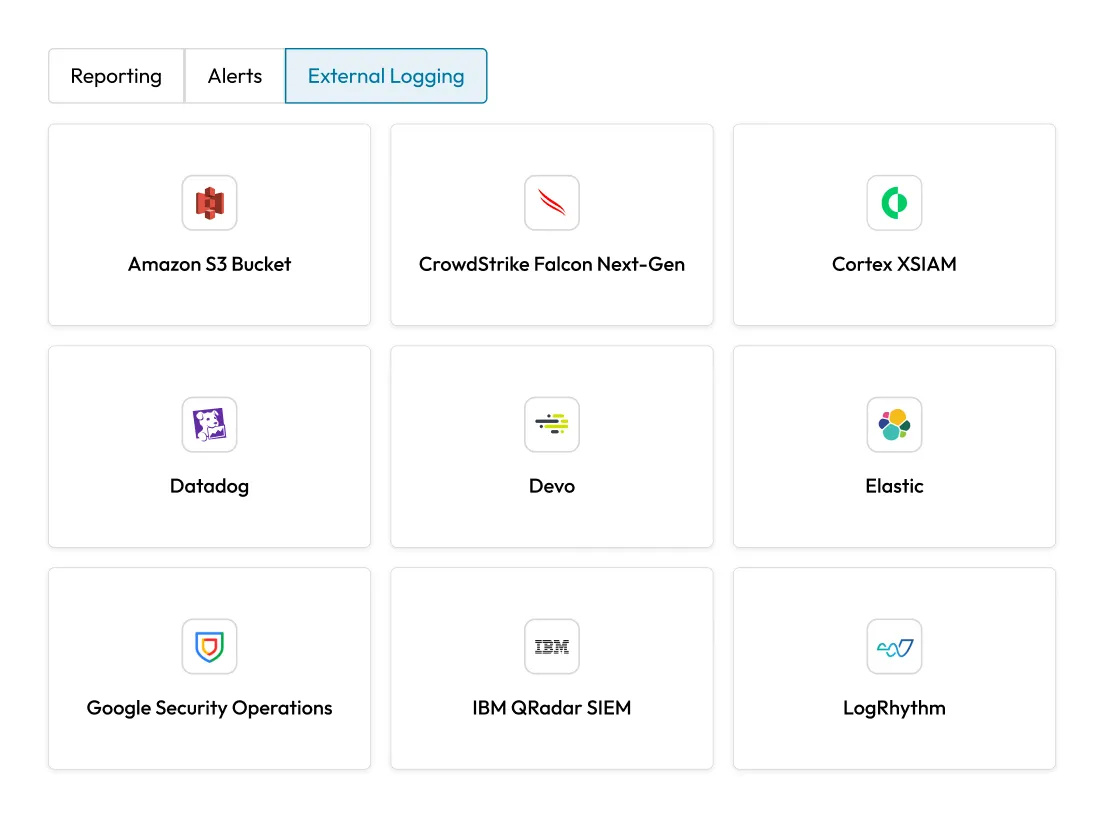
KeeperPAM works with the tools you already use. From Identity Providers (IdPs) like Okta and Entra ID to Security Information and Event Management (SIEM) platforms and Multi-Factor Authentication (MFA) solutions, KeeperPAM fits seamlessly into your security ecosystem.
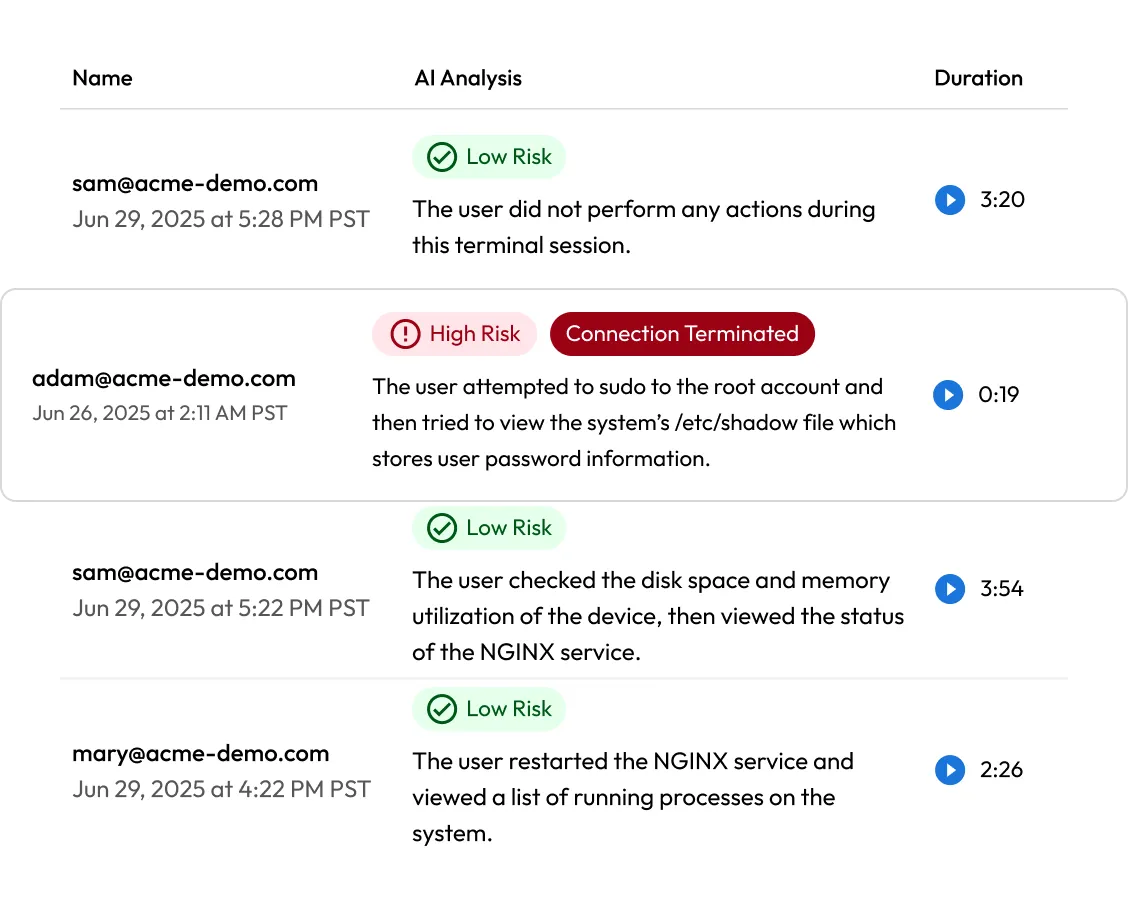
KeeperAI delivers real-time AI threat detection and automated response within privileged sessions. It analyzes live activity, flags high-risk behavior and can automatically end sessions when necessary.
"[Keeper Connection Manager] really has been the perfect remote access solution for us."
Bart Rousseau, Head of Training Lab Operations.
Nokia
"[Keeper Connection Manager] is so clean, fast and efficient. And it's an easy install with a clean interface."
Darin Land, Director of Information Technology,
Lang, Richert & Patch
Protect access to your critical infrastructure with KeeperPAM
KeeperPAM uses zero-trust, outbound-only tunnels established through the Keeper Gateway. Unlike traditional VPNs, which may increase the attack surface, KeeperPAM grants time-limited access only to the necessary systems without exposing credentials.
With KeeperPAM, users never see or handle credentials, ensuring they remain encrypted and hidden. Access is provisioned through the Keeper Vault, which injects credentials into sessions and supports automated rotation based on configuration.
KeeperPAM supports secure remote access to Linux and Windows servers, RDP, VNC, SSH, Kubernetes clusters, internal web apps and databases like MySQL and PostgreSQL.
You must accept cookies to use Live Chat.