Are Your Organization's Passwords on the Dark Web?
Try our free dark web scan to see your cyber risk.
Small-to-Medium Sized Businesses (SMBs) are the primary target for cybercriminals.
Every few seconds, an SMB pays a ransom
of all data breaches are due to weak or stolen passwords
Cyber attacks are now the leading cause of bankruptcy in SMBs
of all businesses hit with a cyber attack go bankrupt within 6 months
Average cost of data breach
What is the Dark Web?
The dark web is a part of the internet that provides anonymous and secure communication channels that are not able to be found by search engines. It is home to a number of criminal activities including the trafficking of stolen personal identifiable information, trafficking of drugs, illegal sales of weapons and more.


Why is a Dark Web Monitoring Tool Important for Business?
A dark web monitoring tool is important for businesses for several reasons including but not limited to:
- Identifying breaches early-on
- Preparing your business for future cyber threats and cyber attacks
- Protecting your employees and customers’ personal information
- Identifying security vulnerabilities in your organization
Without a dark web monitoring tool it can be hours, days or months before you realize accounts at your organization are compromised. This can place your organization and all of its sensitive data at risk of being breached – possibly costing you millions of dollars to fix and permanently damaging your reputation.
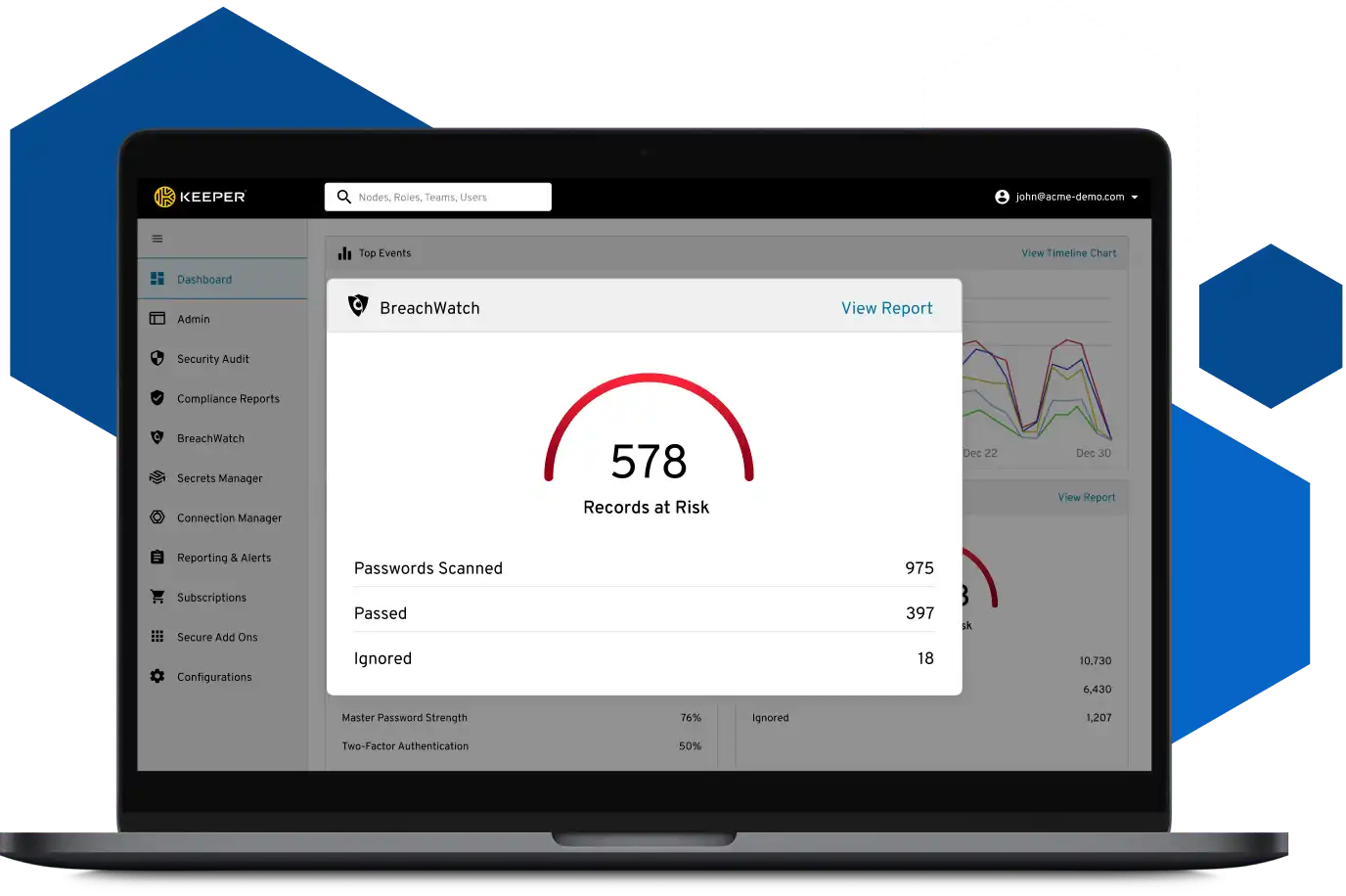
How Does Keeper BreachWatch Work?
Keeper BreachWatch is a dark web monitoring add-on feature that works with Keeper Password Manager. BreachWatch constantly monitors the dark web for breached passwords that match the ones stored in your vault.
When BreachWatch detects a breached credential, an automatic notification is sent to you – allowing you to take action immediately to update it. When you update your credentials using Keeper, your new credentials are automatically saved in your vault under the same record. If you decide to ignore the alert, the record will not be scanned again and your vault will continue to show that the record is at risk.