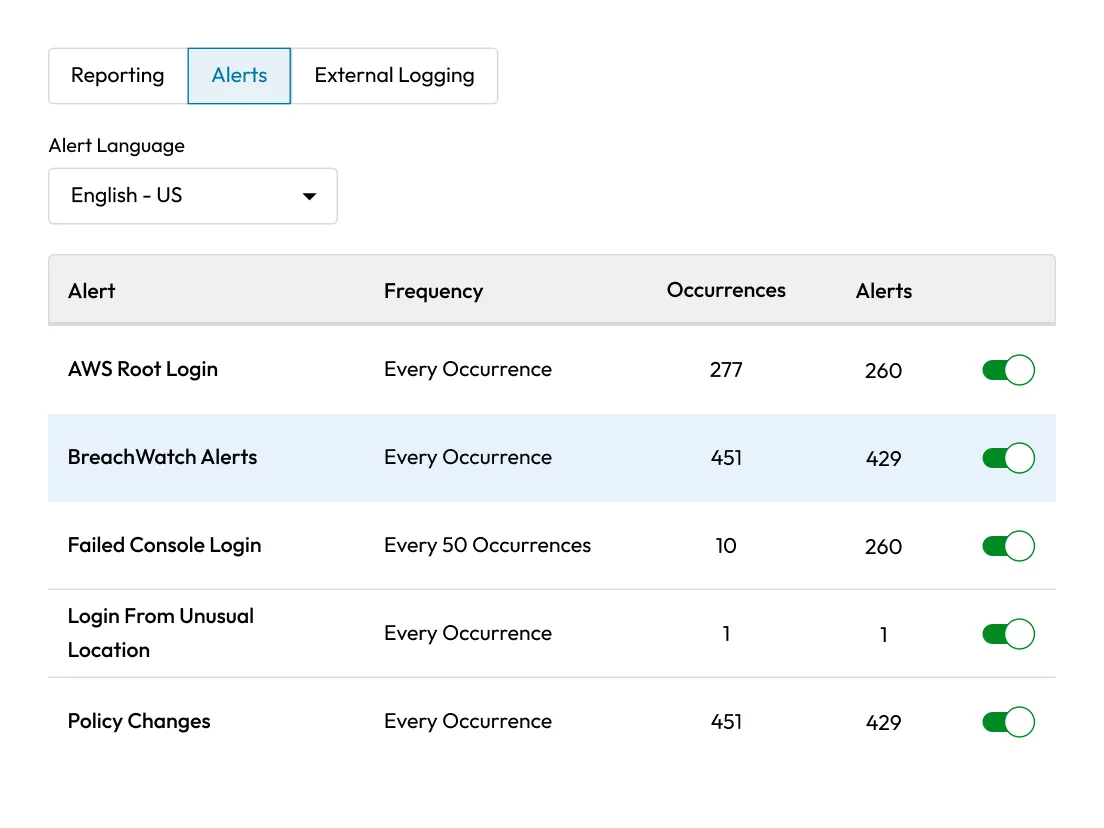
Trigger event-based alerts
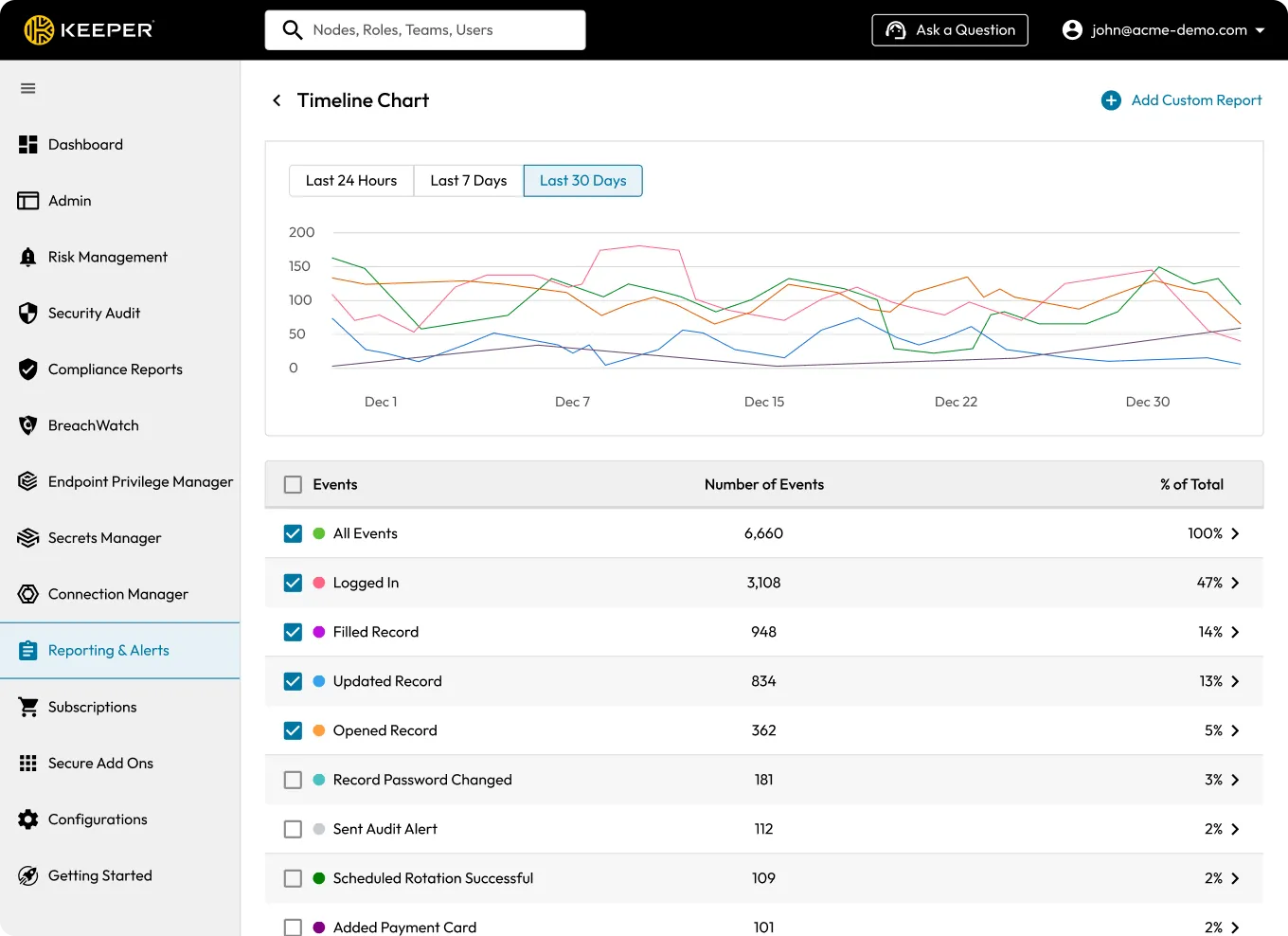
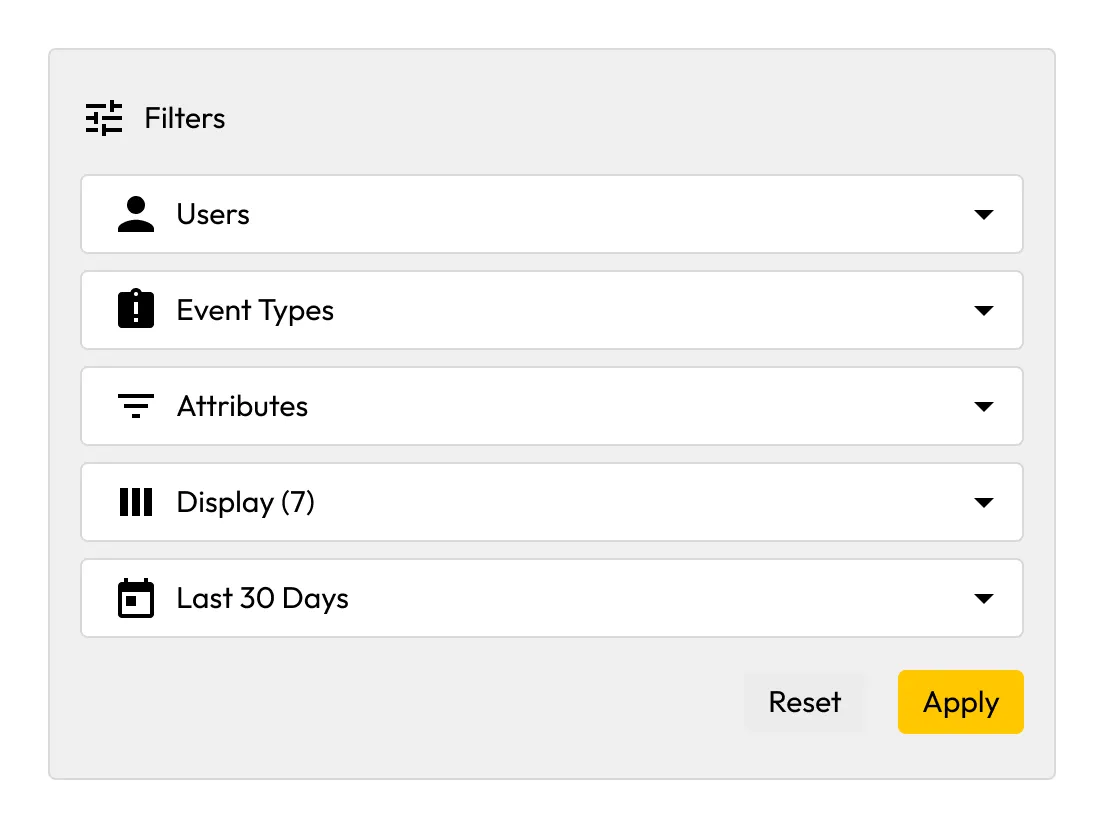
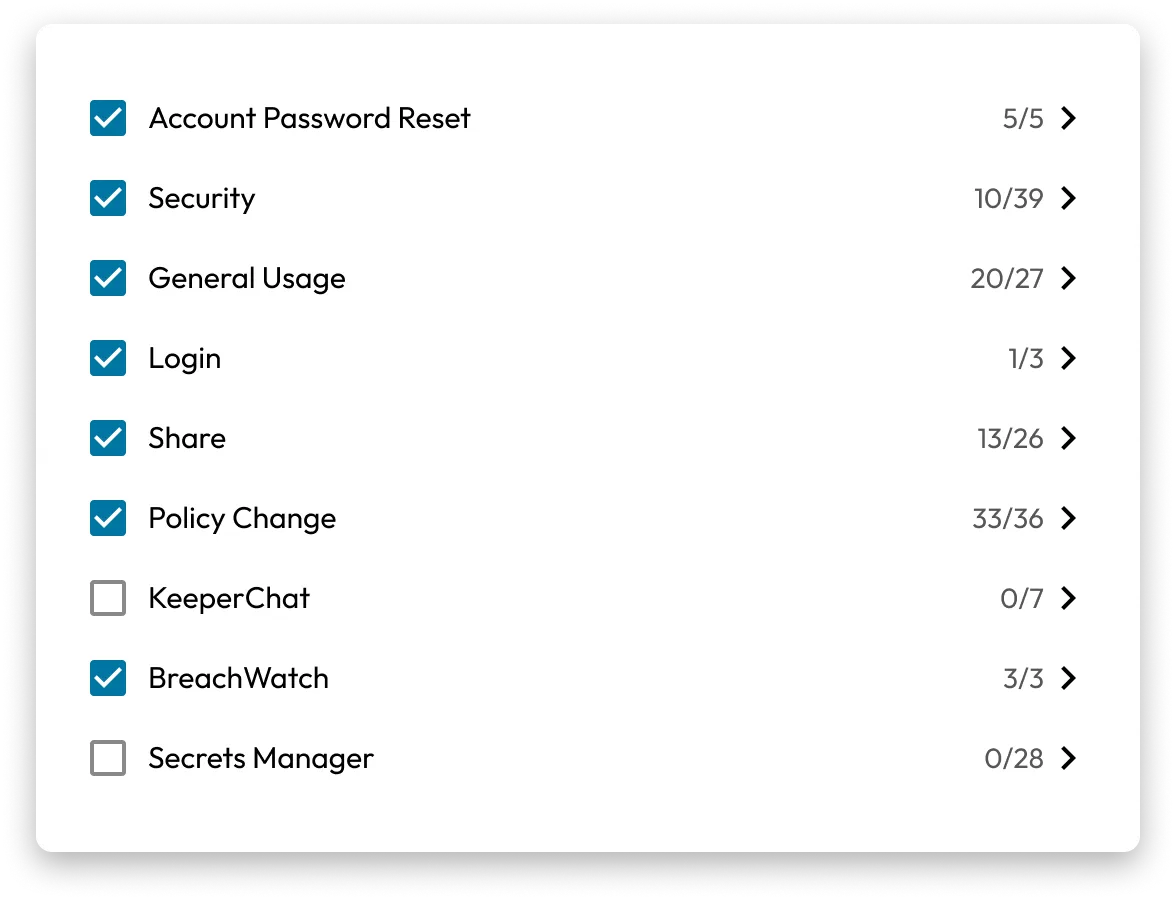
Get real-time alerts on over 300 event types, including human and NHI usage, administrative policy changes, record sharing, BreachWatch dark web detections, privilege elevation requests, PAM sessions, credential access and more. The interactive event timeline shows the most recent activities to help your team respond faster.