Imagine a customer service representative at your organization uploads sensitive customer data into an AI tool to draft emails more quickly. When an employee uses an
Updated on September 26, 2025.
Authentication is an essential part of securing your sensitive information from various cyber threats. In the past, a username and password may have been enough, but you now need an extra verification method to protect yourself from modern cyber attacks. The main difference between Two-Factor Authentication (2FA) and Multi-Factor Authentication (MFA) is that 2FA requires you to use one authentication method in addition to your username and password, whereas MFA requires two or more authentication methods.
Continue reading to learn more about authentication, the difference between 2FA and MFA and the best authentication methods you should use.
What is authentication?
Authentication is the process of verifying that someone is who they claim to be. For example, when you enter your username and password to log in to your email account, that’s a basic form of authentication. However, with more advanced cyber threats, you must use additional layers of authentication to stay safe online.
To understand the difference between 2FA and MFA, you must first know the four types of authentication:
- Something you know: Passwords, PINs or security questions.
- Something you have: Physical or virtual tokens, like a One-Time Password (OTP) or Time-Based One-Time Password (TOTP).
- Something you are: Biometric data, such as your fingerprint or face ID.
- Somewhere you are: Apps and services that are only accessible if you’re in a specific geographic location.
What is 2FA?
Two-Factor Authentication (2FA) requires users to provide two different forms of authentication before gaining access to an account or system. That way, even if one factor, like your password, is compromised, a second form of authentication helps prevent unauthorized access. 2FA typically combines something you know (like a password) with something you have (like an OTP code).
What is MFA?
Multi-Factor Authentication (MFA) is a form of authentication that requires two or more additional factors beyond your username and password before accessing an account or system. Although 2FA is a subset of MFA since it uses two factors, MFA can involve two, three or four types of authentication factors for stronger protection. MFA is typically used for securing sensitive systems where having only one or two layers of security may not be enough.
What is the difference between 2FA and MFA?
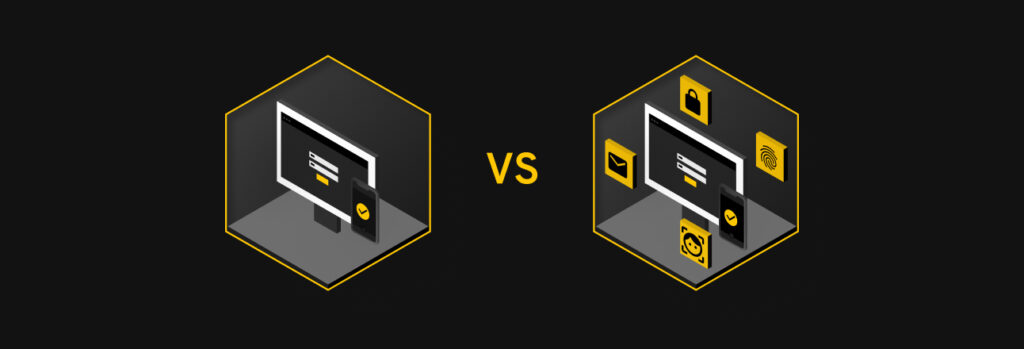
While 2FA and MFA are closely related, the key difference between them is the number of authentication methods used. 2FA uses exactly two factors, typically something you know and something you have. MFA, on the other hand, refers to the use of two or more authentication methods. This can include the same factors used in 2FA, but it can also go a step further, such as adding something you are (biometrics) or somewhere you are (location-based authentication).
In simple terms, all 2FA falls under MFA, but not all MFA is limited to only two factors of authentication.
| Feature | Two-Factor Authentication (2FA) | Multi-Factor Authentication (MFA) |
|---|---|---|
| Number of factors used | Exactly two | Two or more |
| Security level | Stronger than passwords alone | Stronger than 2FA, depending on how many additional factors are used |
| Use cases | Social media, banking, online shopping | Corporate systems, healthcare, government |
| Examples | Password with a TOTP code | Password with an authenticator app and Face ID |
Is MFA more secure than 2FA?
MFA is generally more secure than 2FA because it allows for more than one additional authentication factor beyond your username and password. To qualify as MFA, each factor must be a different type (something you know, something you have, etc.). For example, entering both a password and a PIN isn’t MFA since both are something you know. However, if you log in with a password, an OTP code and a fingerprint scan, those are three different types of authentication factors, making it a true example of MFA.
That being said, 2FA is much more secure than using only a password. 2FA is also widely supported across most apps and online platforms. Even though MFA offers stronger protection than 2FA, it’s still best practice to enable 2FA wherever MFA isn’t available.
The best 2FA and MFA authentication methods
Here are some of the most secure authentication methods we recommend using:
- Hardware security keys: Security keys are physical devices used to verify your identity. A popular example is YubiKey, which looks like a small USB drive. When plugged in or tapped against your device, the token authenticates your access to an app, account or system. Since they require you to physically have them, security keys offer strong protection against many online attacks.
- Biometric authentication: Biometrics rely on your physical characteristics to verify your identity. Common forms include fingerprint scanning, facial recognition and iris scans. These methods are nearly impossible to fake or steal since they are part of you, making them among the most secure authentication methods available.
- Authenticator apps: Authenticator apps generate TOTPs on your smartphone. When linked to an account, you’ll need to enter the code from the app (Google Authenticator, Authy, Microsoft Authenticator, etc.) to log in. TOTPs typically expire every 30 seconds, adding a dynamic layer of security to your login process.
Why SMS codes aren’t the best authentication method
While many people associate 2FA with receiving codes via text message (SMS), this is the least secure authentication method since cybercriminals can intercept them through SIM swapping or phishing. Many people choose SMS authentication out of convenience, but if you’re looking for a more secure alternative, consider using a password manager like Keeper®. Modern password managers like Keeper offer built-in support for TOTPs, meaning you can store and access your 2FA codes without relying on text messages or the inconvenience of a separate authenticator app. Additionally, if you share access to an account stored in your vault, the 2FA can be shared as well, making it easier to collaborate and access sensitive information.
Protect your online accounts with additional authentication
Both 2FA and MFA provide crucial layers of security that can significantly reduce the risk of unauthorized access to your accounts. While 2FA offers more security than passwords alone, MFA offers even stronger protection by requiring multiple forms of authentication from different categories. Whether you’re protecting your personal online accounts or critical systems at work, enabling 2FA or MFA is an easy and effective way to protect your data.
Frequently asked questions
Which is better, MFA or 2FA?
Multi-Factor Authentication (MFA) is generally better than Two-Factor Authentication (2FA) because it uses two or more types of authentication methods, making it harder for cybercriminals to access your accounts. Although 2FA uses exactly two factors, MFA can include more than two layers, like biometrics or location-based authentication, for additional security. However, both 2FA and MFA are much safer than using only a password, so you should enable either whenever possible.
What is the strongest form of MFA?
The strongest form of Multi-Factor Authentication (MFA) combines all four types of authentication factors: something you know, something you have, something you are and somewhere you are. For example, using a security key, biometric authentication and location-based authentication in addition to a strong, unique password provides one of the highest levels of protection because it requires possession of a physical device, a unique biological characteristic and presence in the correct location — making it incredibly challenging for cybercriminals to bypass.
Is 2FA unhackable?
No, Two-Factor Authentication (2FA) can be hacked. While 2FA improves account security beyond a username and password, some methods, like SMS codes, are vulnerable to phishing attacks or SIM swapping. Using stronger 2FA methods, such as authenticator apps or security keys, can reduce security risks but is not entirely foolproof.