Privileged Session Management FAQs
What is PSM?
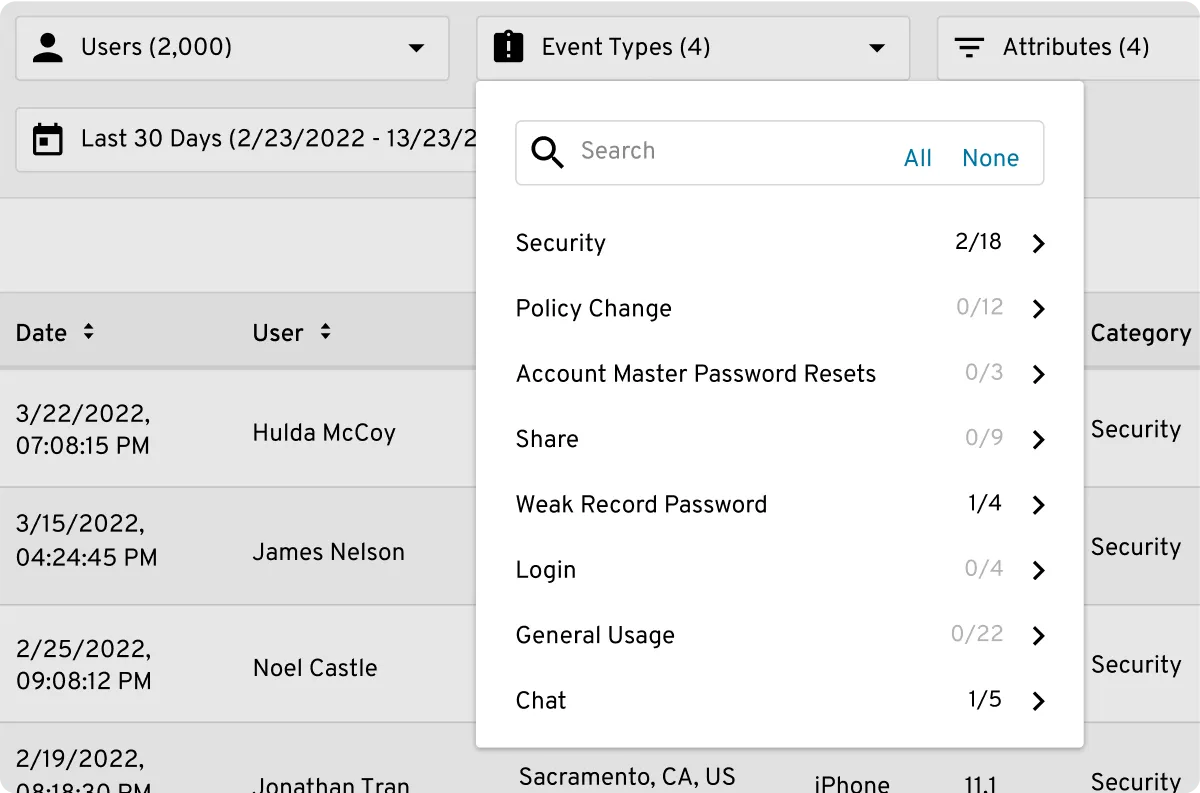
Privileged Session Management (PSM) is a cybersecurity control wherein companies record, monitor and control user sessions initiated by privileged accounts. PSM ensures that organizations have complete visibility and control over privileged access, which is integral to both data security and compliance.
What is meant by a "Privileged Account"?
A privileged account, also known as an "admin account", is a set of login credentials used to access highly sensitive network and digital assets, including firewalls, servers and administrative accounts.
What is privileged activity monitoring?
Privileged activity monitoring is a broad term encompassing the process of monitoring, auditing and controlling network activity by privileged users. PSM is a form of privileged activity monitoring.
PAM vs PSM: What's the difference?
Privileged Access Management (PAM) is an umbrella term that refers to the process of safeguarding accounts used by privileged users, meaning those with access to admin accounts. PAM involves a combination of people, processes and technology. Privileged Session Management (PSM) is a subset of PAM that refers specifically to recording, monitoring and auditing login sessions by privileged users.