Understanding Zero-Trust
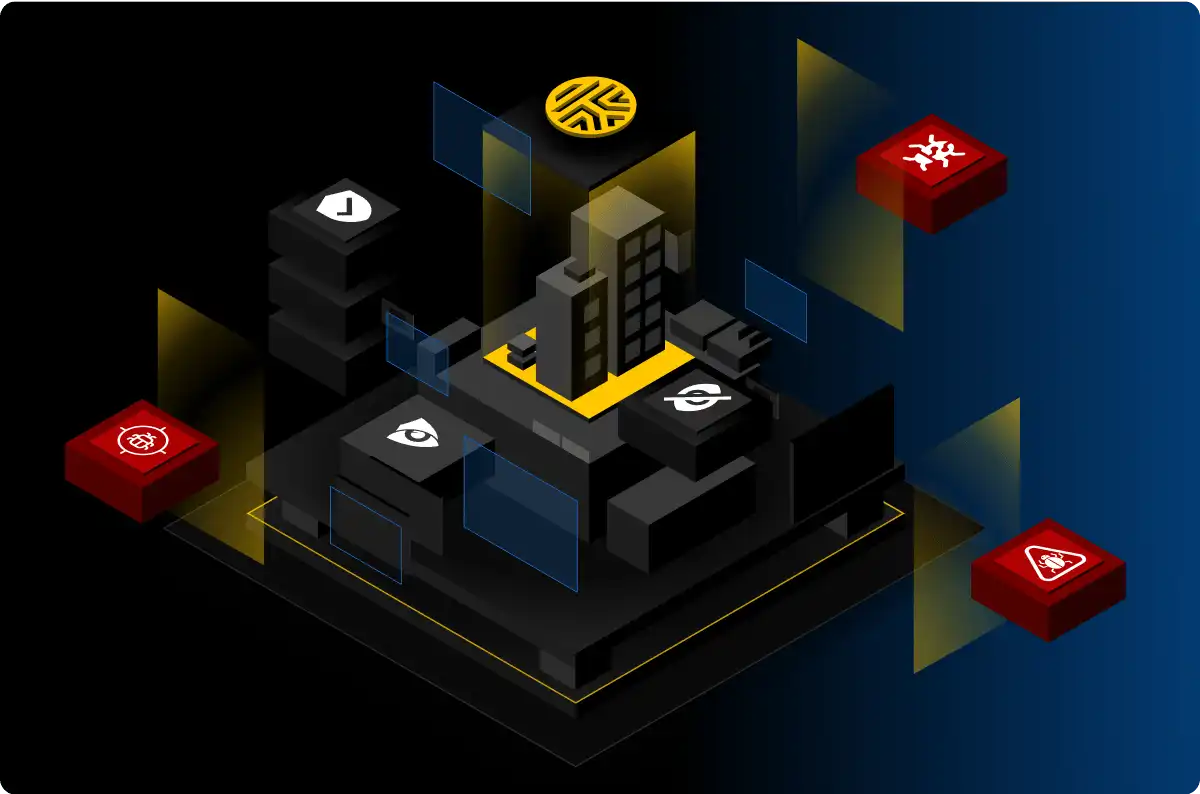
The zero-trust security framework is centered around three core principles: assume breach, verify explicitly, and ensure least-privilege access.
Instead of implicitly trusting all users and devices within the network perimeter, zero trust doesn’t trust any of them. Zero trust assumes that all users and devices could potentially be compromised, and everyone, human or machine, must be verified before they can access the network. Once logged onto the network, users should have the minimum amount of network access they need to perform their jobs, and no more.
When deployed properly, the zero-trust model gives IT administrators full visibility into all users, systems, and devices, helps ensure compliance with industry and regulatory mandates, and helps prevent cyber attacks caused by compromised user credentials.