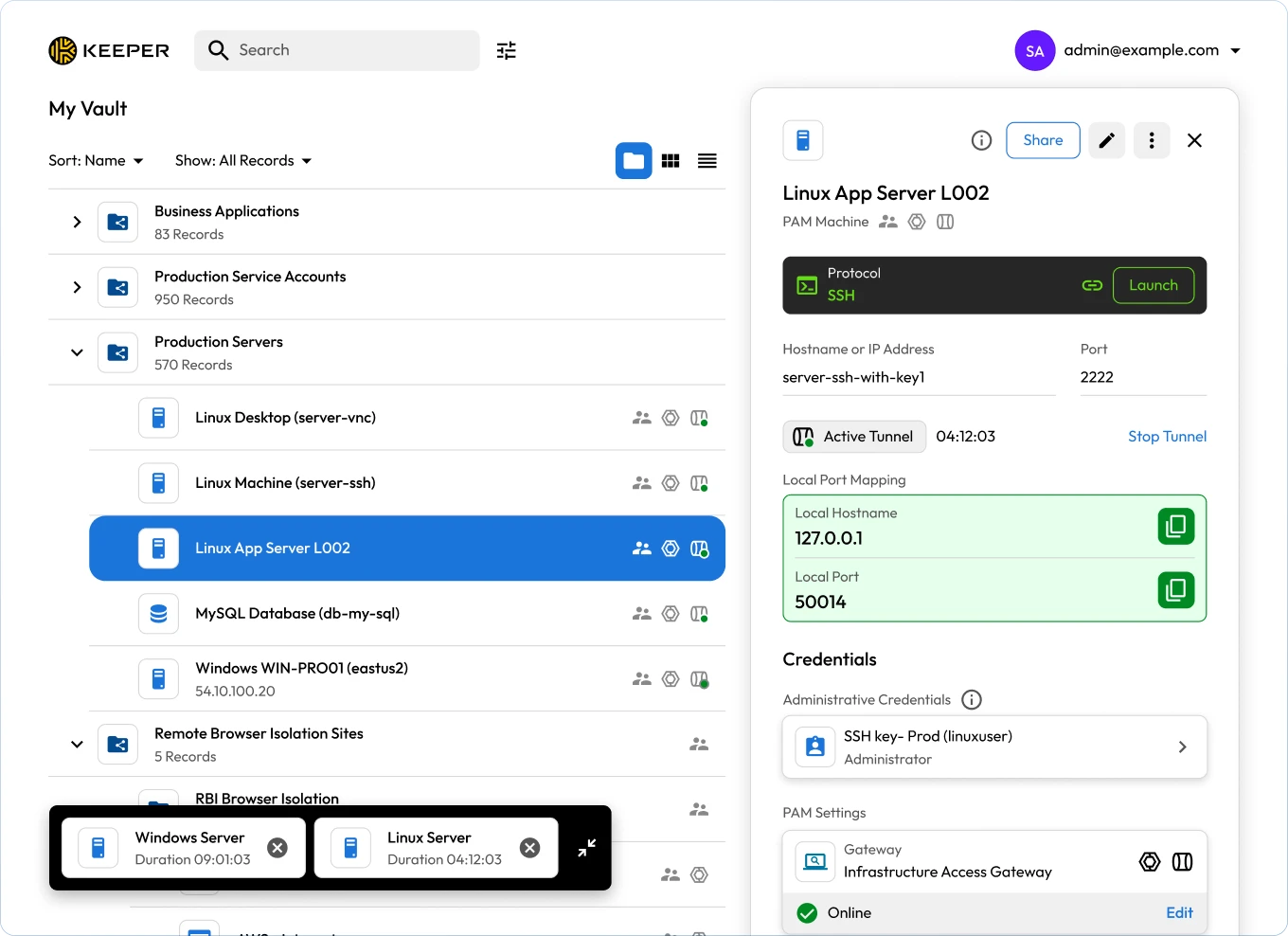
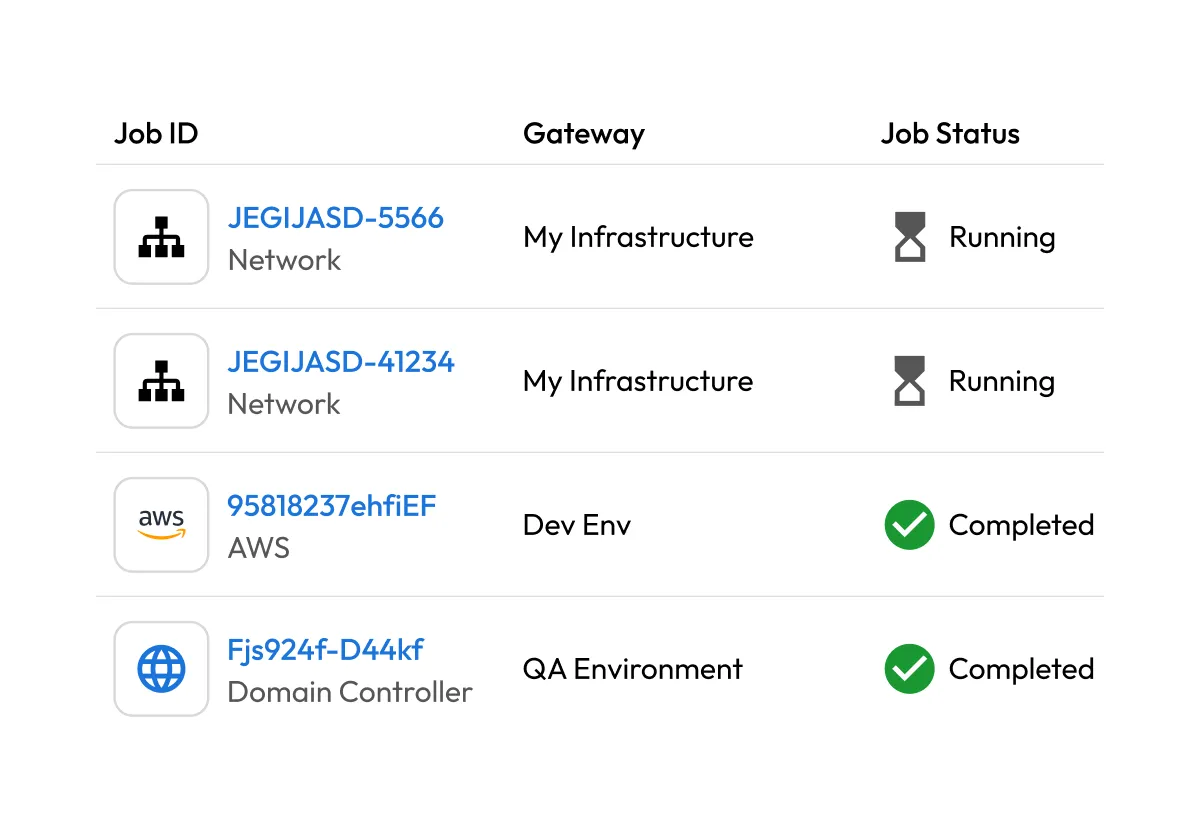
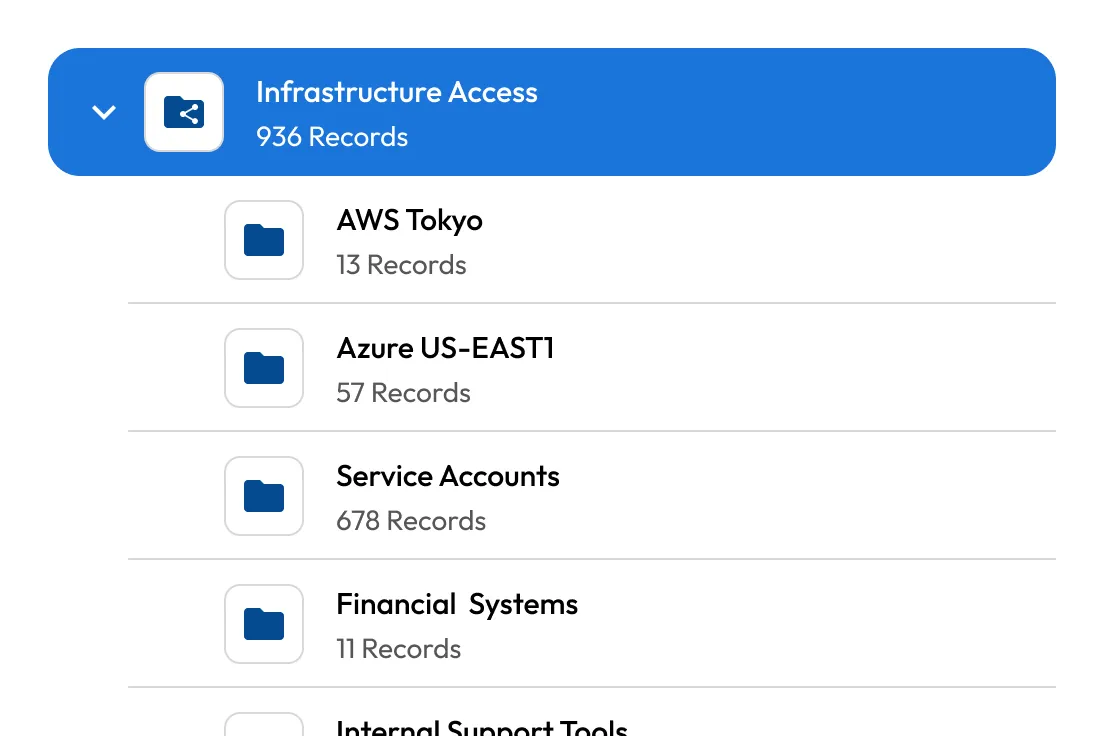
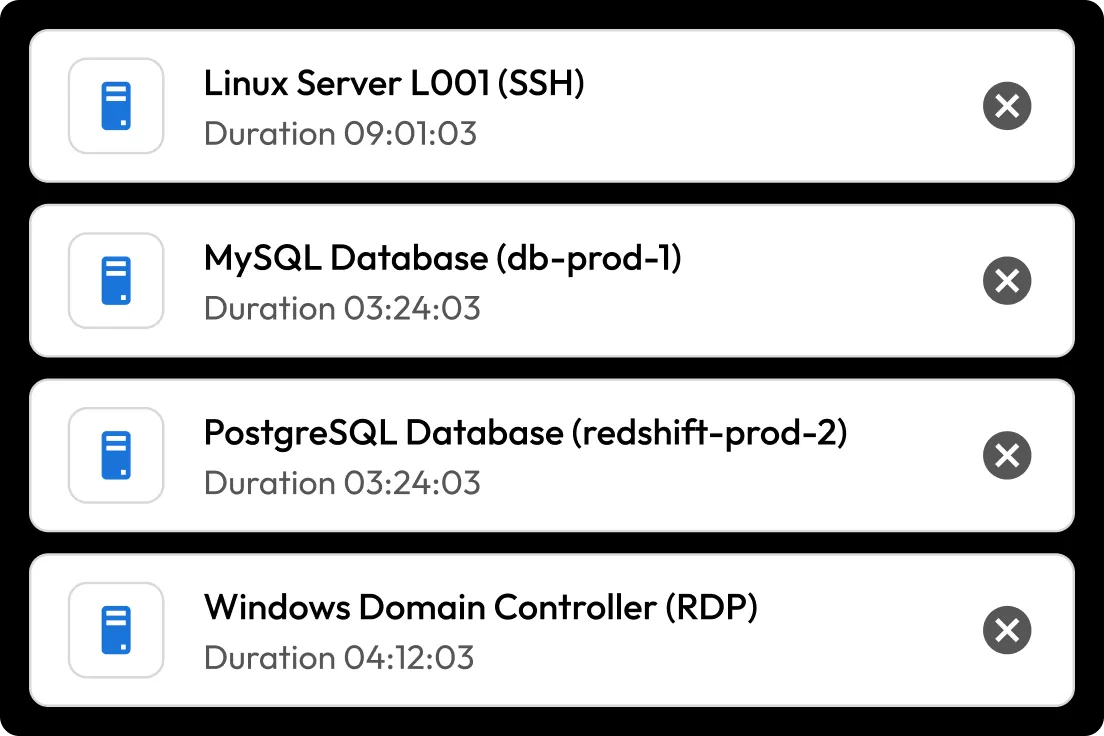
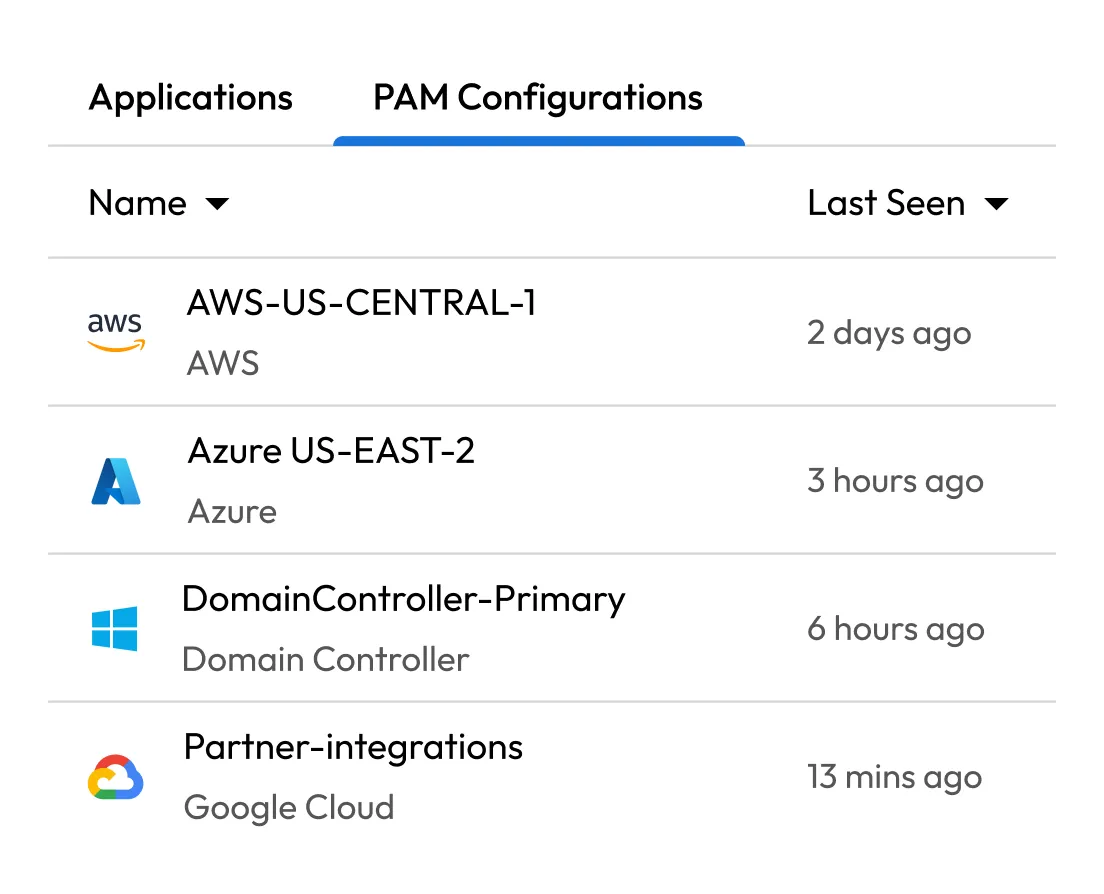
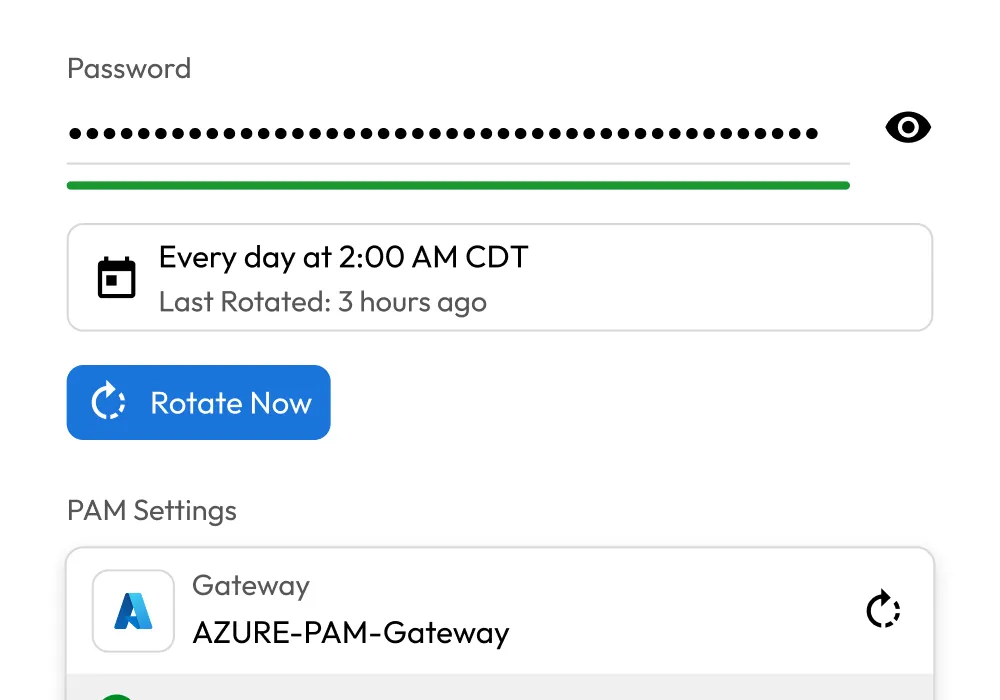
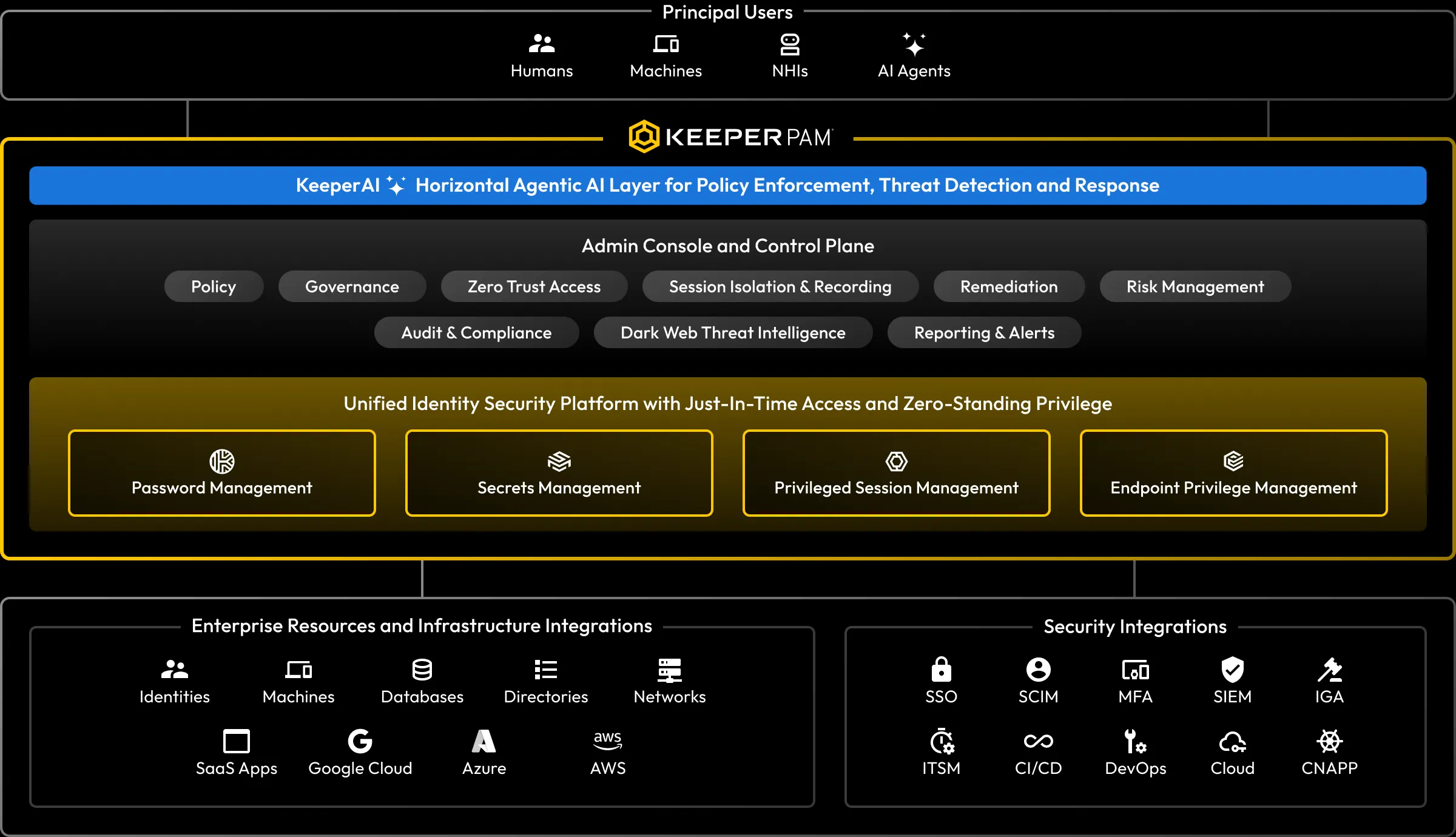
Privileged Access Management
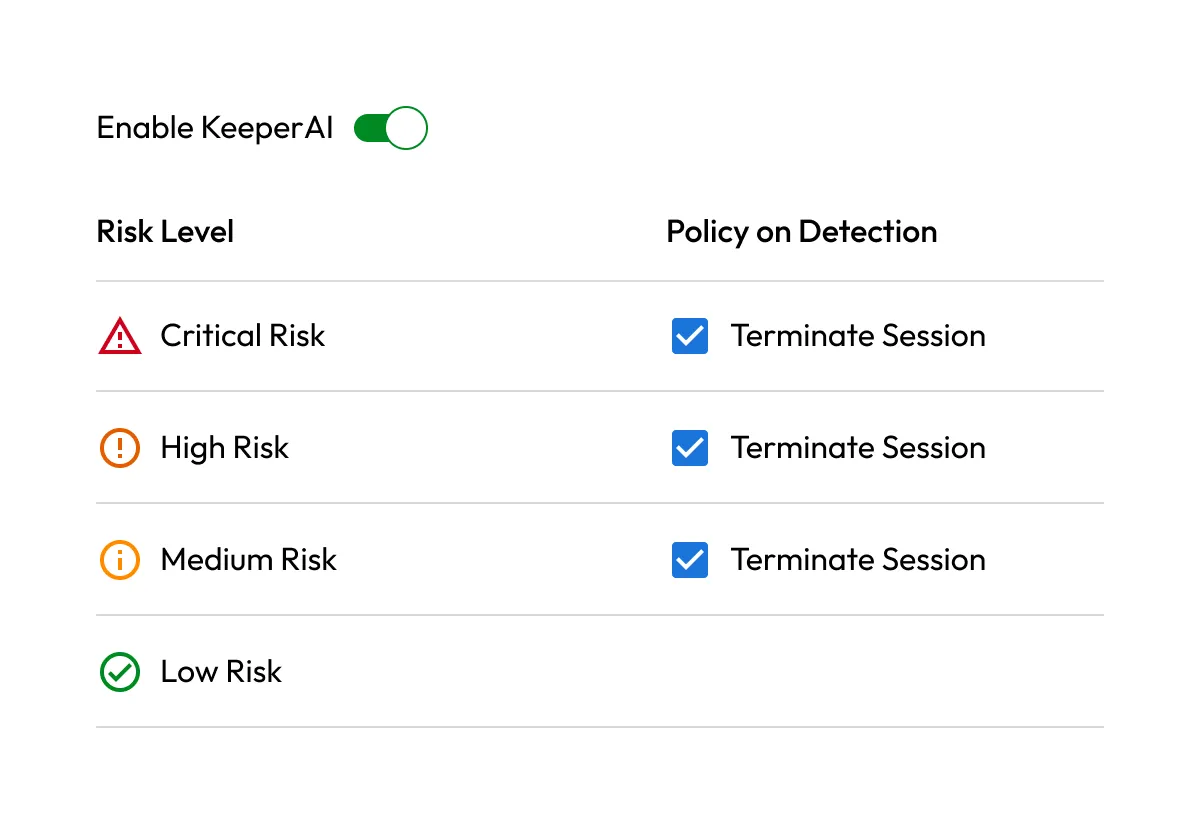
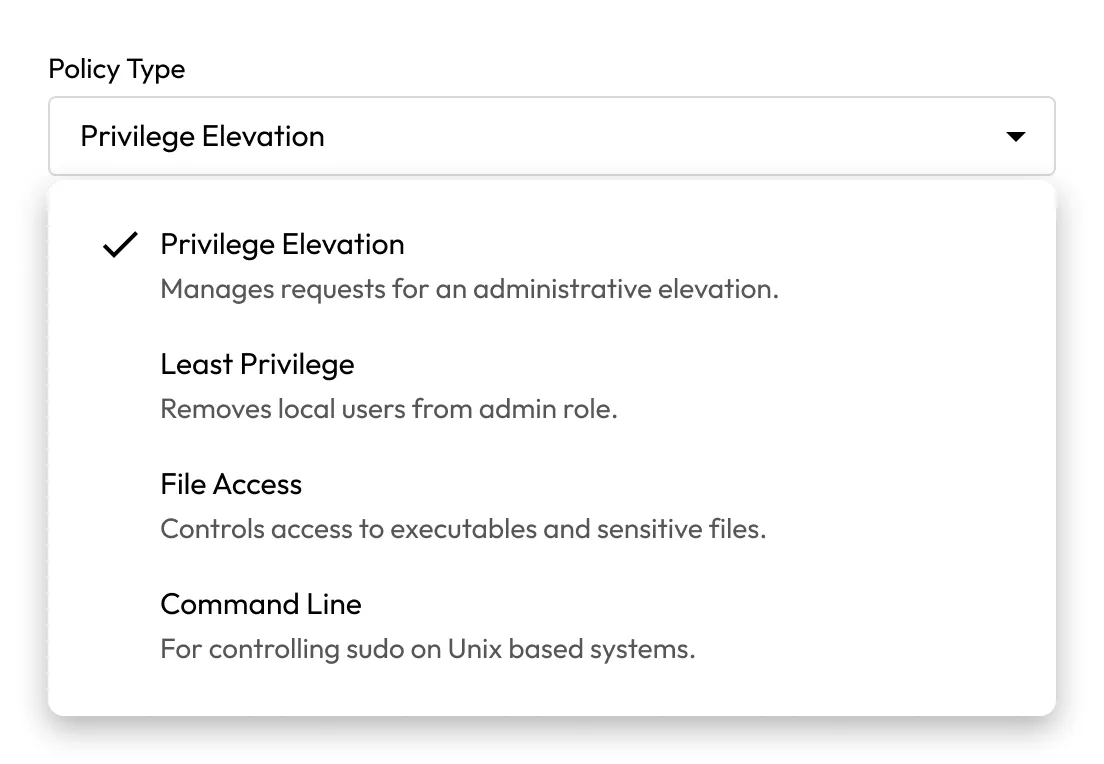
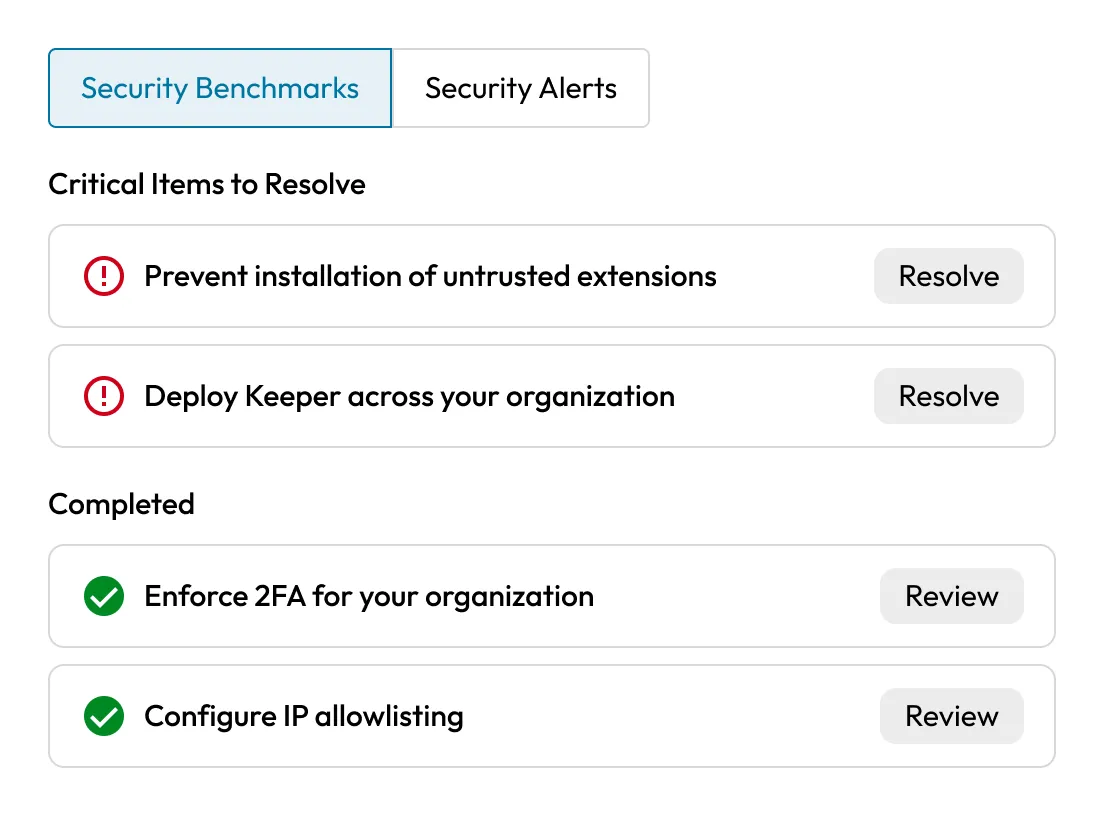
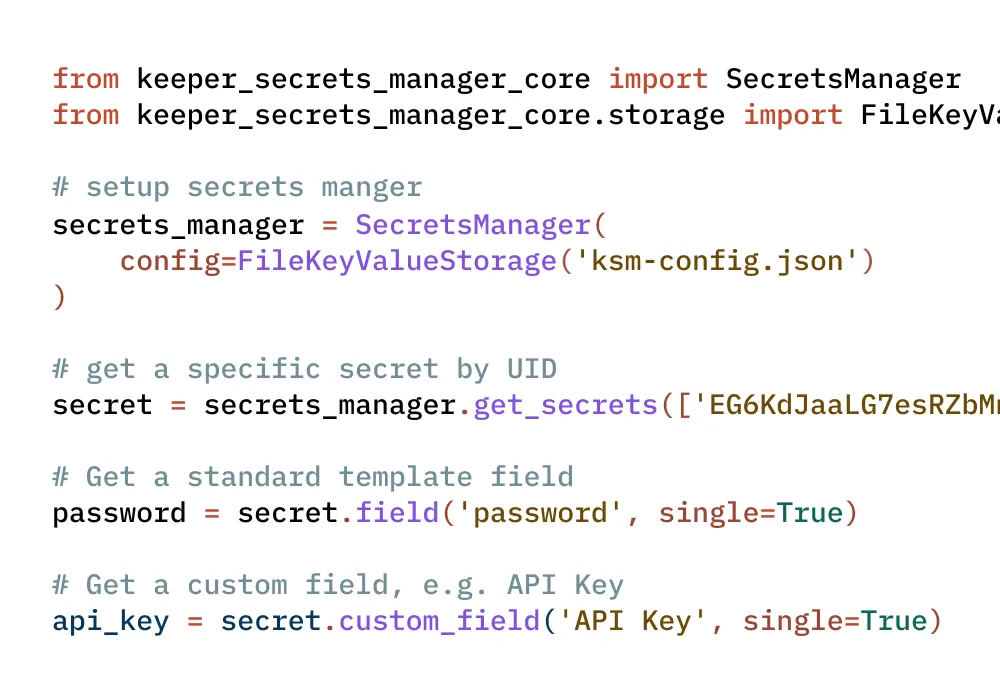
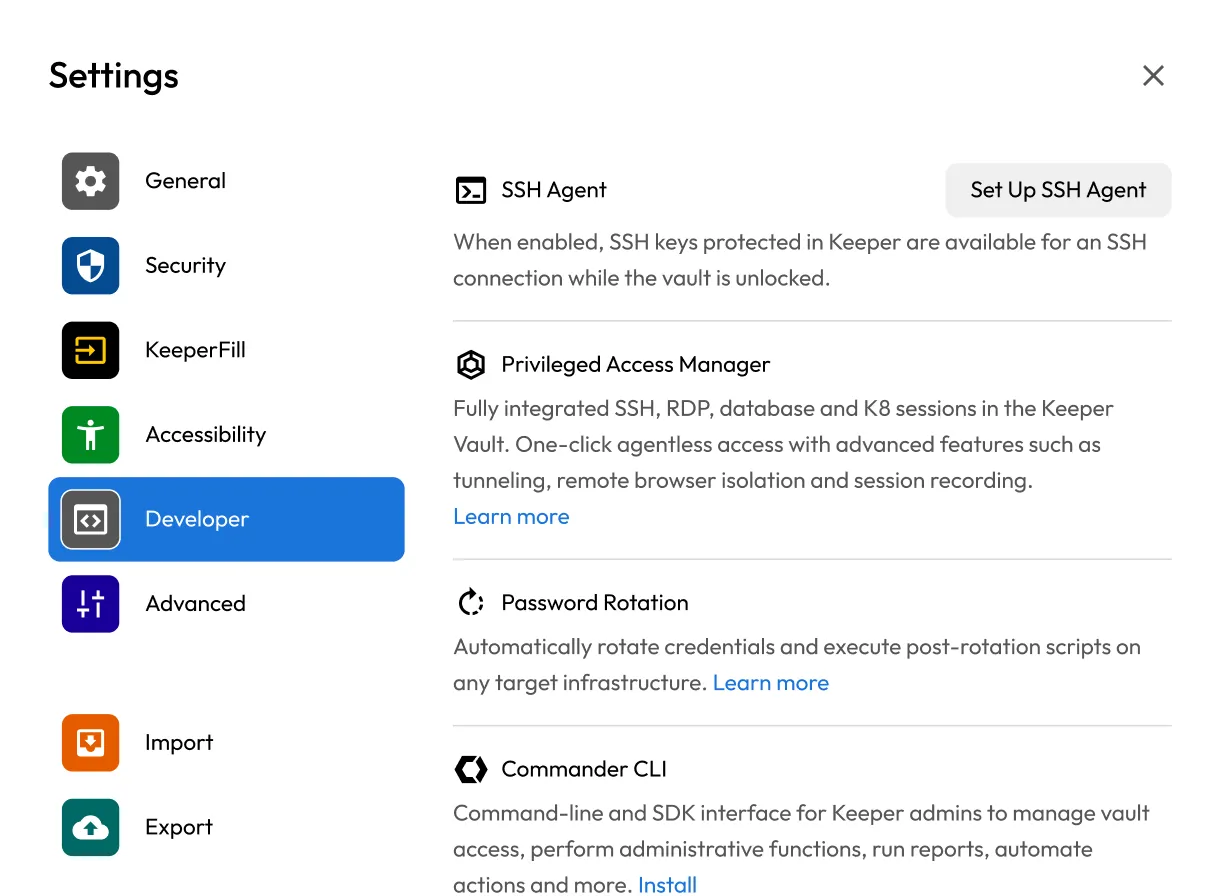
The modern AI-enabled PAM platform for securing and managing access to critical infrastructure and endpoints
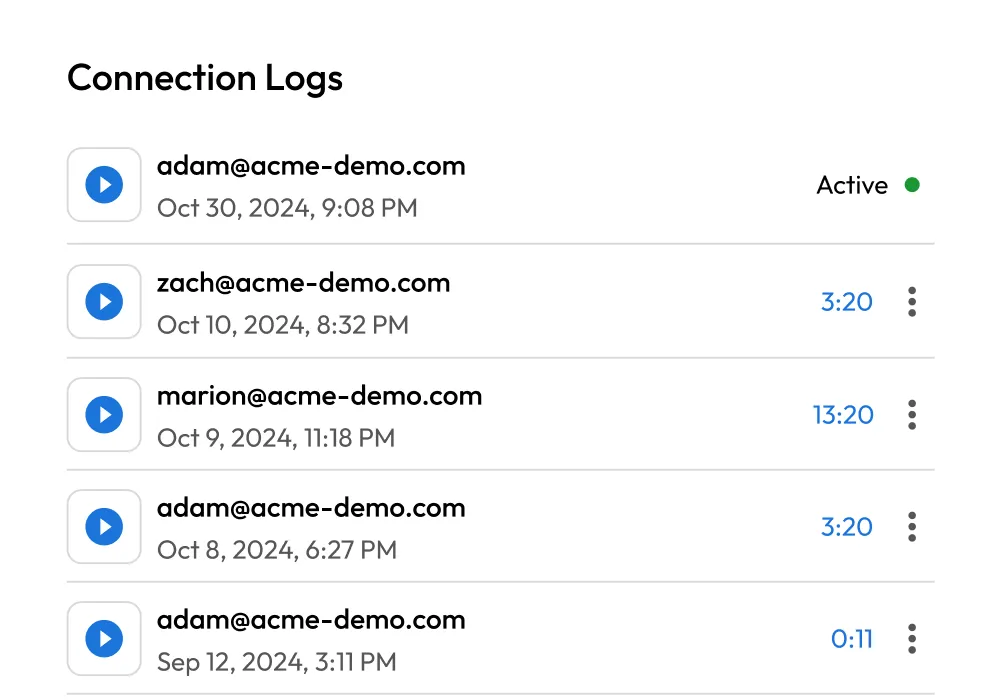
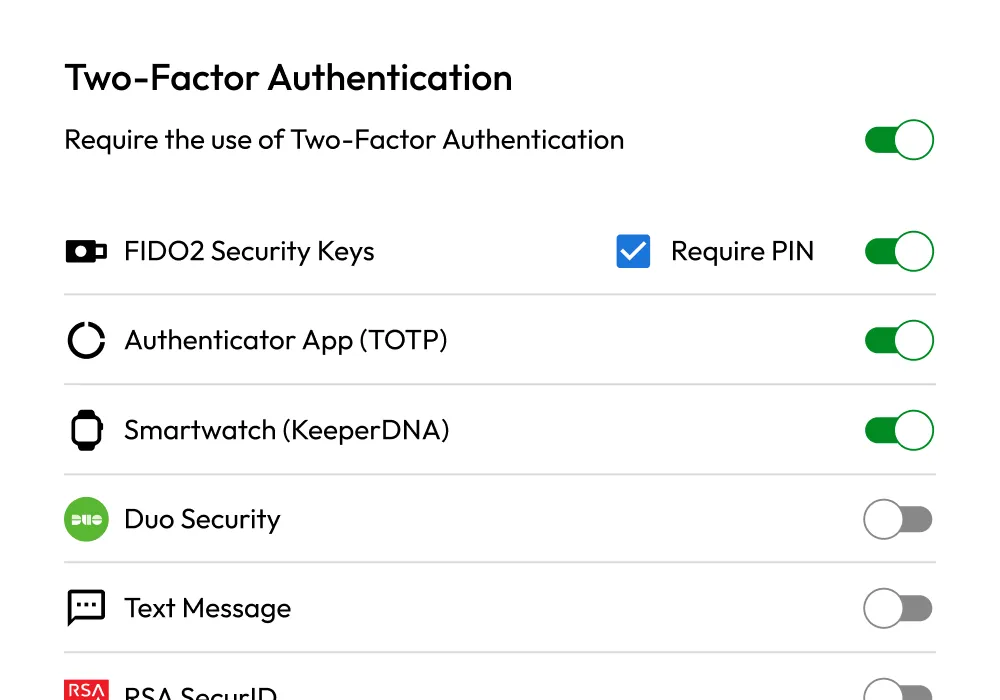
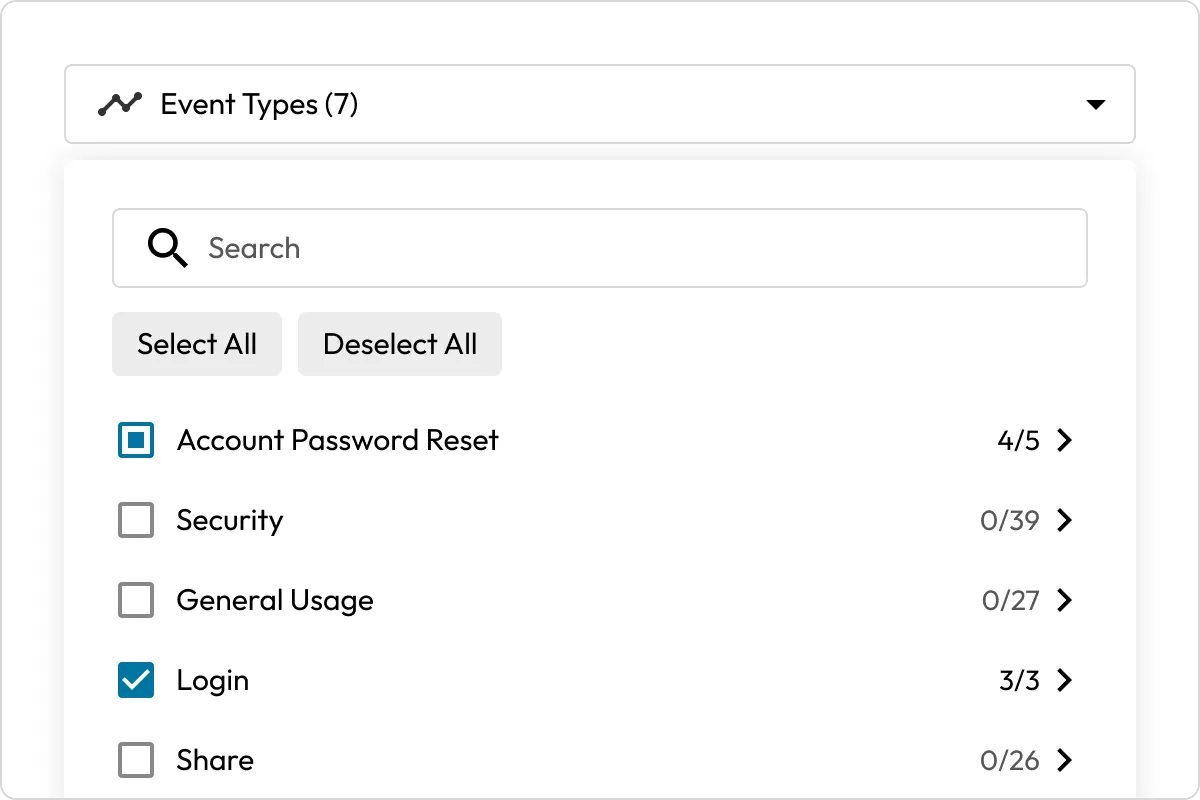
Authenticate and authorize every user and device in your enterprise with monitoring, threat tracking and reporting.