Seamlessly integrate with any data environment
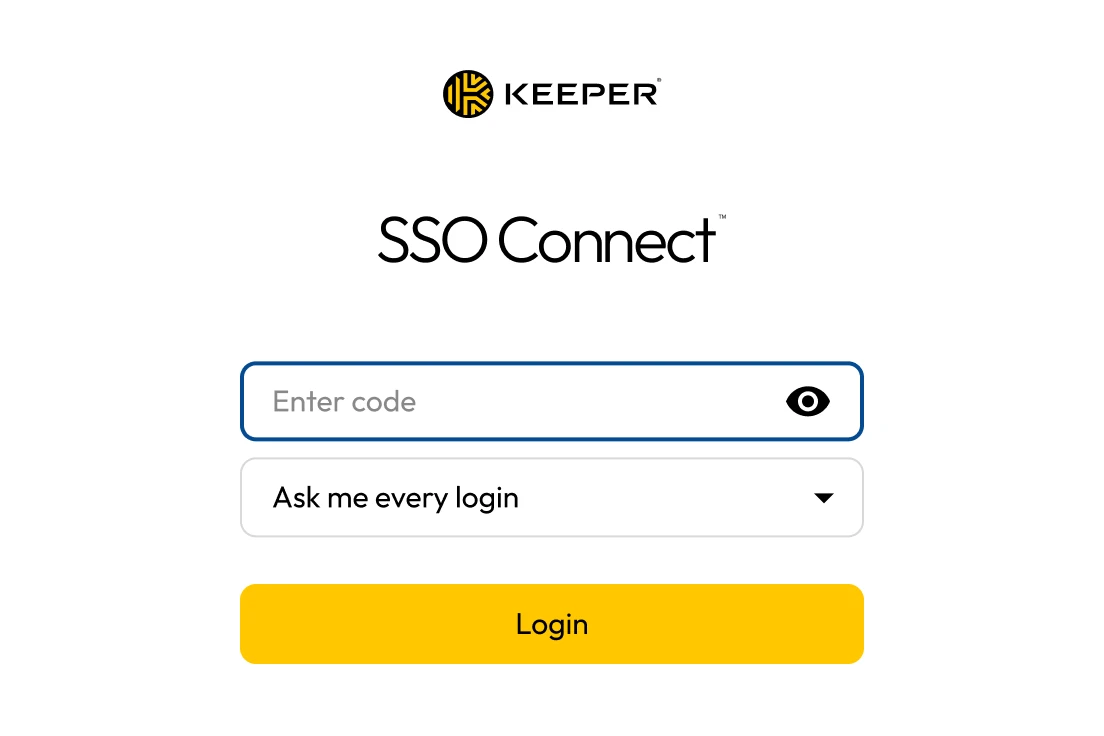
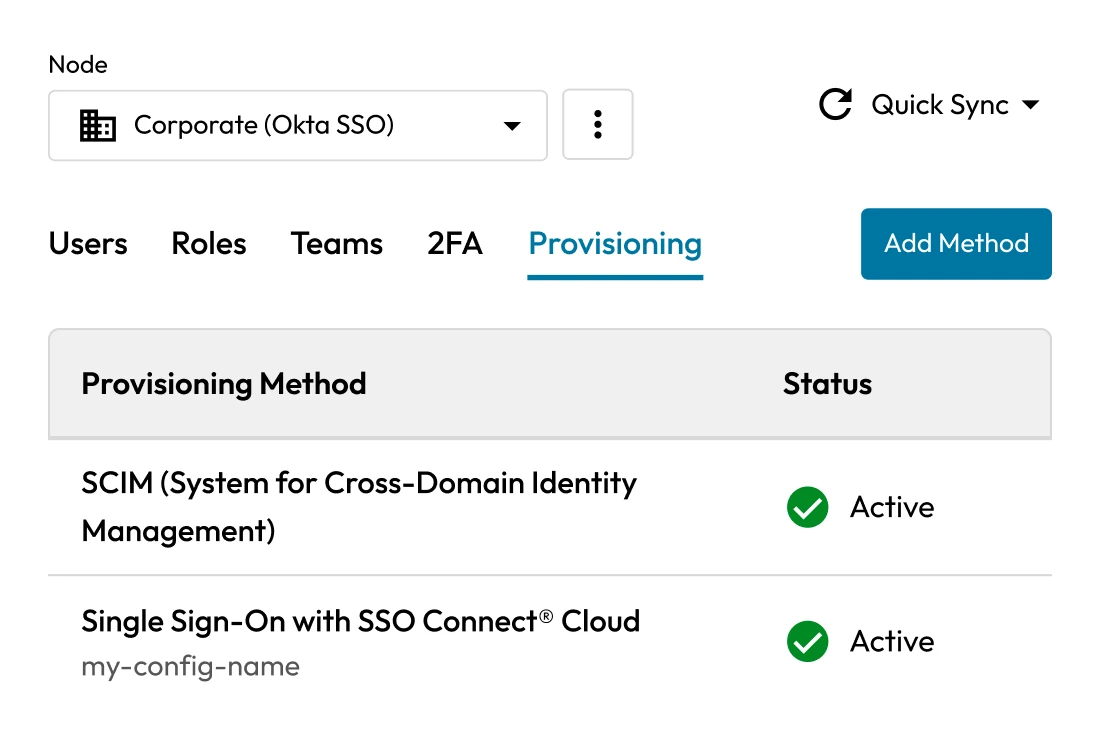
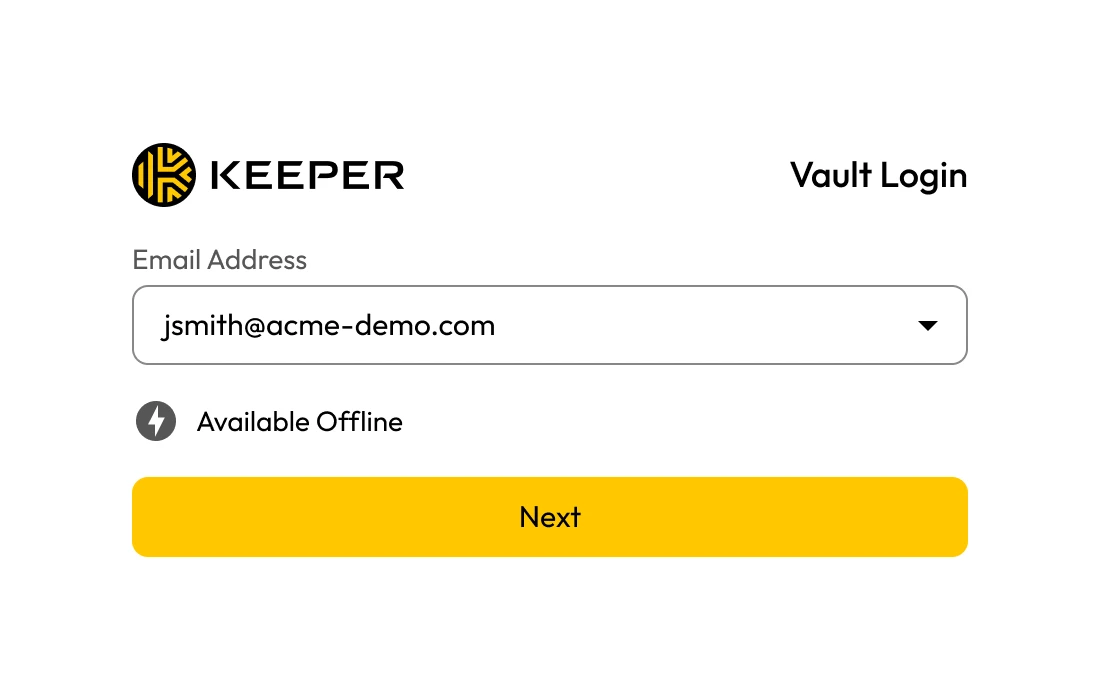
Secure any environment - cloud or on-premises - across Windows, macOS and Linux with Keeper SSO Connect. It integrates seamlessly with leading identity providers, including Microsoft 365, Entra ID (Azure), ADFS, Okta, Ping Identity, JumpCloud, Centrify, OneLogin and F5 BIG-IP APM.