Protect Privileged Systems with Zero-Trust Remote Database Access
Request a DemoWhat is Remote Database Access?
Remote Database Access (RDA) is a protocol standard that typically refers to accessing databases between a device and a server remotely. The database refers to data stored in the cloud or in physical computer systems.

The Importance of Securing Remote Database Access
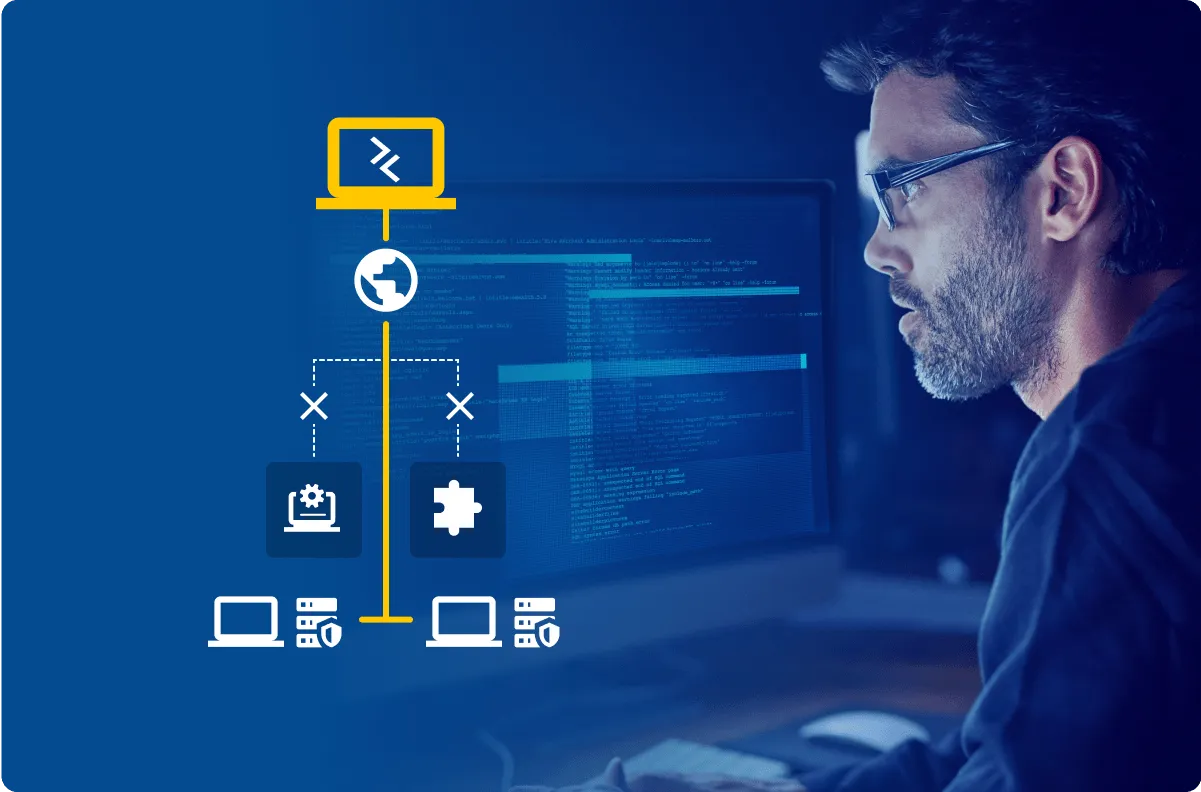
Providing access to your most sensitive systems is necessary, but it introduces risk. VPNs typically provide too much access, especially for contractors, vendors and occasional-use employees.
Exposing database credentials introduces even more risk. Understanding who has access to systems is difficult when shared root or system administrator accounts are used.
It's important to secure databases and who has access to them because they contain sensitive data such as proprietary company data and customers' Personally Identifiable Information (PII). Knowing who has access to these systems is essential in the event of a security breach or insider attack.
How to Secure Database Access Without Credential Exposure
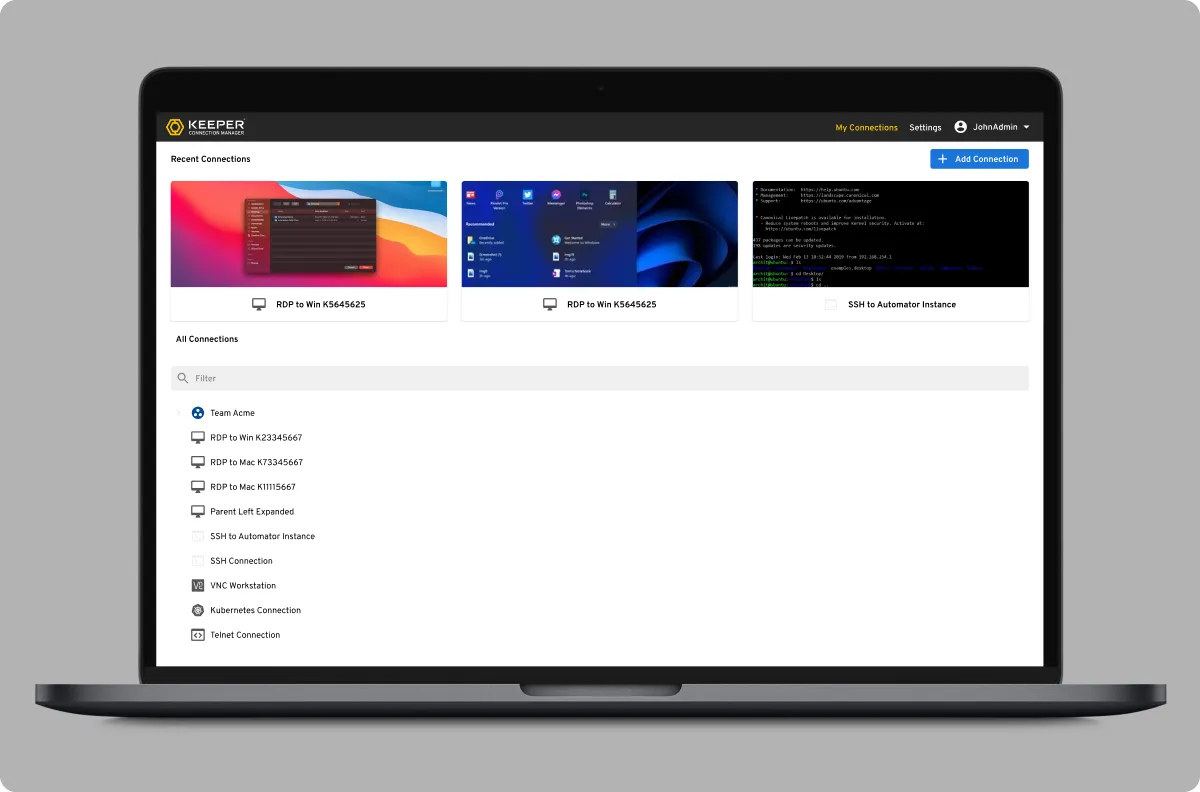
Keeper Connection Manager (KCM) eliminates the risk associated with using VPNs. KCM allows administrators to provide direct database access to MySQL, SQL Server and PostgreSQL. Other database types can be accessed via RDP, SSH, K8s, VCN and RemoteApp – all without having to share credentials. Access can be revoked at any time, and a robust audit trail identifies when and how the system was used.

Control Database Access With Multiple Access Paths
Keeper Connection Manager is built on a foundation of zero-knowledge and zero-trust security, with granular access rules. Administrators can provide Database Administrators (DBAs) with access to the whole target system or just one component.
For MySQL, a specific SSH-like connection type can be configured. If your DBAs prefer to work in a UI such as SQL Server Management Studio (SSMS), RemoteApp can be set up to just allow access to SSMS.
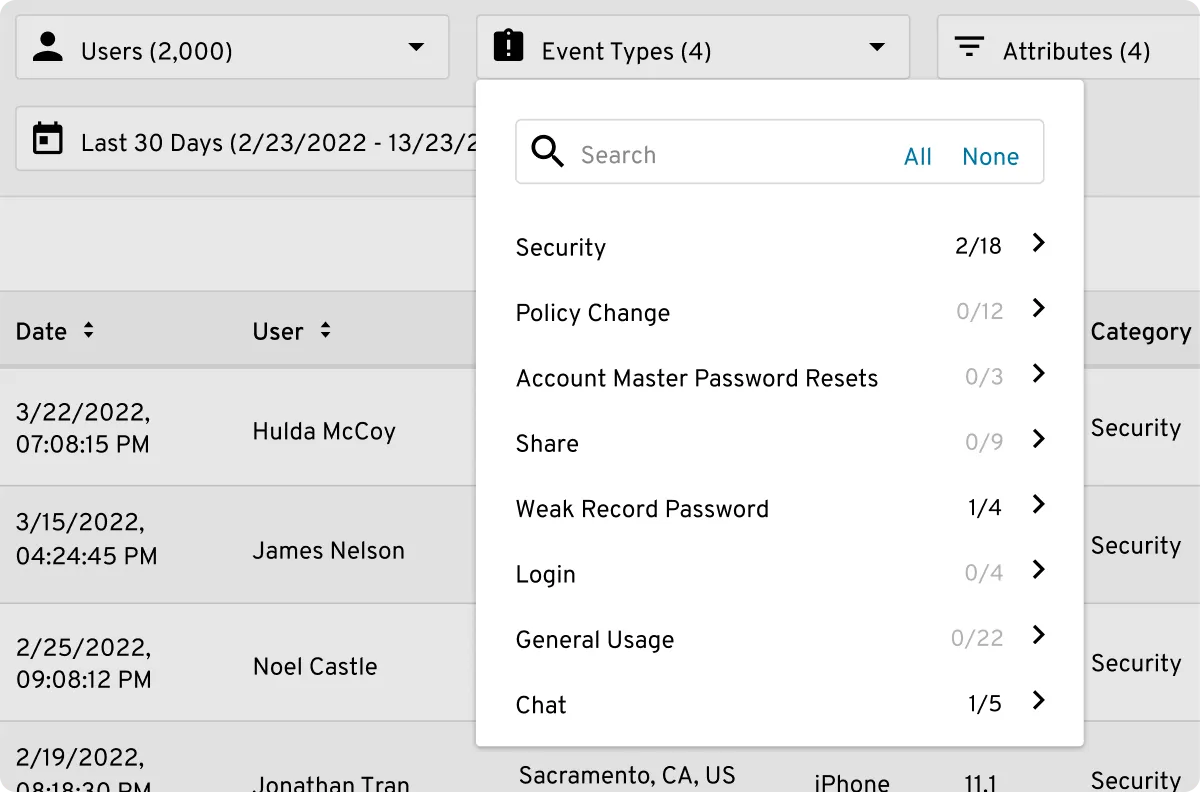
Meet Compliance Needs With Audited and Recorded Sessions
Nearly all compliance frameworks address the risks associated with privileged systems access by mandating that access requests be logged and recorded, including any database systems considered "in scope." KCM satisfies these core needs.
Securing Remote Database Access is Easy With Keeper
Implementing a Privileged Access Management (PAM) solution should be as painless as possible. This is often not the case. Some solutions require custom clients to be installed for all privileged users and agents to be installed on all privileged endpoints, in addition to one or more bastions to broker the connections. Some require changes to your Active Directory (AD), or direct access to your domain controllers.
Because it's agentless and clientless, Keeper Connection Manager is easy to deploy. Simply install a gateway and you have support for:
- MySQL, PostgreSQL and SQL Server database connections
- RemoteApp
And other non-database connections:
- SSH
- VNC
- Kubernetes
- RDP out-of-the-box
There are no agents, your web browser is the client and there is no impact to your database servers or other services.

A Secure Bastion = Superior Security
The Keeper Connection Manager gateway can be completely locked down to the customer's infrastructure to limit access between the client device and target server. Secrets that are used to connect to the target servers can be managed within the Keeper Secrets Manager encrypted vault. Pass-through credentials also provide users with dynamic access to target instances without secrets storage anywhere in the gateway.

Keeper Offers Extensive Monitoring, Auditing and Reporting
In addition to aggregate security audits, Keeper also provides event logging for over 200 event types, event-based alerts and integration with popular 3rd party SIEM solutions.
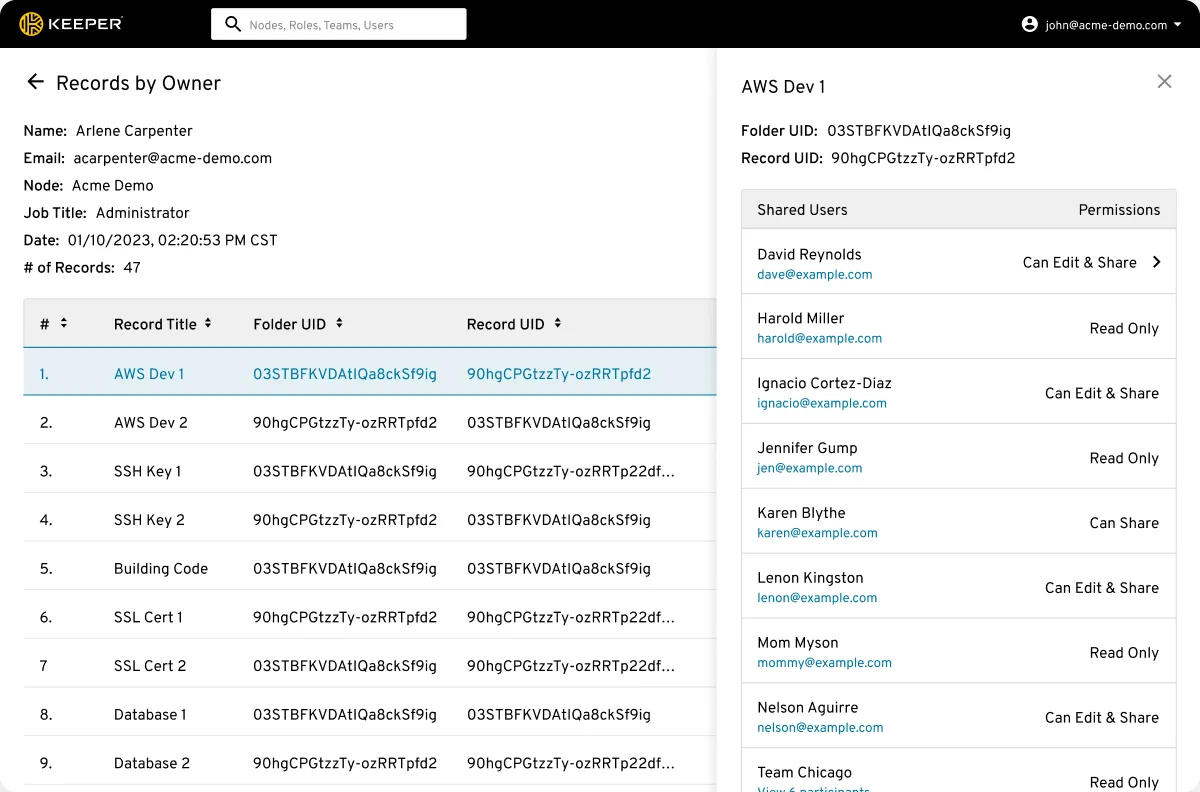
Keeper's compliance reporting functionality allows admins to monitor and report on access permissions for privileged accounts across the entire organization, in a zero-trust and zero-knowledge security environment.
Market-Leading Security Infrastructure and Policies
Keeper holds the longest-standing SOC 2 attestation and ISO 27001 certification in the industry. Keeper utilizes best-in-class security, with a zero-trust framework and zero-knowledge security architecture that protects customer data with multiple layers of encryption keys at the vault, shared folder and record levels.
