The main difference between Keeper and Delinea is their focus on Privileged Access Management (PAM). While both platforms offer PAM solutions, Keeper stands out as the superior choice. It provides a more comprehensive cybersecurity solution that includes password management, remote access and privileged access management, whereas Delinea only offers a PAM solution. What Is a
Updated on May 23, 2023. The main difference between Keeper and LastPass lies in their approaches to security. Keeper uses a zero-knowledge security model and encrypts data at the device and record level, while LastPass only encrypts data at the vault level making it more vulnerable to cyber attacks. Furthermore, Keeper offers a range of
Regulations and frameworks such as PCI-DSS, SOX, NIST SP 800-53, NERC CIP and HIPAA require privileged user activity to be monitored and audited sufficiently for investigation. Privileged user monitoring and auditing for databases are critical as databases often contain the most sensitive information to an organization. Many organizations leverage built-in database auditing capabilities included with
Updated on February 10, 2023. Password security is crucial to preventing cyber attacks. It is important to find a password manager that enables the zero-trust security model to mitigate the risks of data breaches from compromised user accounts. Here is a breakdown of this security framework and how Keeper helps with zero-trust compliance requirements. What
Updated on September 27, 2023. Identity and Access Management (IAM) is a framework of policies and business processes that ensure authorized users have necessary access to the technological resources they need to perform their jobs. IT and security administrators use IAM solutions to administer user identities and control access to enterprise resources, particularly sensitive organizational
One of the selling points of cloud computing is the ability to quickly spin up new machines as needed. Unfortunately, this means that cloud environments grow very complex, very quickly – and manually updating configuration files to add new instances gets really old, really fast. It’s easy to make a mistake, which inhibits productivity and
The term “ITAR compliance” is a misnomer. Unlike FedRAMP and other compliance frameworks, there is no formal “ITAR Compliance” or “ITAR Certification” process. Organizations that fall under ITAR need to understand how the regulations apply to them and set up internal policies and controls to protect ITAR technical data. Let’s examine what ITAR is all
Updated on September 27, 2023. A password manager is a tool that provides users and businesses with the ability to track, store, protect, share and manage login credentials for applications and online services in an encrypted vault. Password management solutions are crucial to keeping users safe and secure online. As cybercriminals increasingly infiltrate networks, it
RSAC 2022 is happening now! RSA Conference is the world’s leading cybersecurity event offering a multitude of opportunities to learn valuable insights, network with peers, and get hands-on with cutting-edge demos. Keeper Security is proud to be exhibiting this year and will be hosting personalized demonstrations, in-depth product overview and Q&A sessions, and 1:1 meetings
Terraform is a very popular infrastructure-as-code (IAC) tool that enables DevOps teams to deploy and manage infrastructure such as servers, containers and databases. Since Keeper Secrets Manager supports record creation through Terraform, you can secure infrastructure secrets using your Keeper Vault. This feature, combined with existing credential read functionality, makes it possible to maintain your
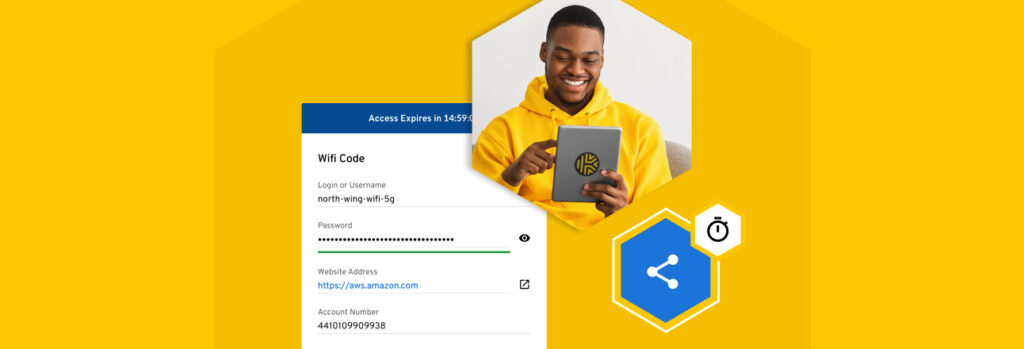
Ever need to share a password with someone, maybe a friend, a contractor or a business associate but they don’t have a Keeper account? Keeper is pleased to announce the launch of One-Time Share, a new feature that lets Keeper users securely share records with anyone on a time-limited basis, without the recipient having to
The mass migration to distributed work presented IT and DevOps teams with new challenges as they were forced to perform infrastructure monitoring and management remotely. IT and DevOps personnel needed a secure, reliable, and scalable way to remotely connect to their machines that is easy to manage. Keeper Connection Manager provides DevOps and IT teams
Cloud computing, widespread distributed work, hyper-digital supply chains, and the rapidly rising number of connected devices provide threat actors with more potential entry points into organizational networks than ever before – and they’re leveraging stolen user credentials to breach them, according to a recent Gartner blog discussing the top cybersecurity trends for 2022. It’s Not
The zero trust security model is rapidly gaining in popularity because it works so well in today’s distributed data environments – and work models. In addition to applications and data being spread across multiple private and public clouds, users are accessing organizational resources from multiple locations, on multiple devices, on both home and public internet
In recent years, many business and IT decision-makers have established a track record of questionable decision-making when it comes to organizational cybersecurity, from not properly segmenting networks, to not deactivating unused accounts (or protecting them with multi-factor authentication) to not implementing proper password security controls and more. As a result, organizations were victimized by costly
Ransomware was the number-one type of cyber attack victimizing organizations in 2021, accounting for 21% of cyber attacks worldwide, and manufacturing was the most heavily targeted industry, according to new research by IBM Security. The most common ransomware strain by far was REvil, also known as Sodinikibi, which made up 37% of the attacks, with
Multi-Factor Authentication (MFA) is crucial to protecting against password-related cyber attacks. On a fact sheet the White House released earlier this week, advising organizations on how to protect themselves against potential cyber attacks in light of the crisis in Europe, the first action item is, “Mandate the use of multi-factor authentication on your systems to
Managing IT infrastructure secrets is a hassle. Ironically, deploying and maintaining most secrets management solutions is at least half the battle. Typically, installing a secrets manager requires purchasing and installing additional on-prem hardware, then enduring a complex and time-consuming software installation process, and maintaining servers moving forward. Keeper Secrets Manager (KSM) was designed to be
The NVIDIA security breach resulted in tens of thousands of employee login credentials being leaked online. Threat actors also made off with mass quantities of highly confidential business information, including code signing certificates and what appears to be source code for the company’s Deep Learning Super Sampling (DLSS) technology. Common Methods for Stealing Employee Credentials
MYKI MSP customers were dismayed last week when they received an email from the company, a copy of which was posted on Reddit, announcing that MYKI had been acquired by JumpCloud – and that the MYKI password manager, including MYKI for MSPs, was being discontinued. According to the email, MYKI customers have until April 10,