Imagine a customer service representative at your organization uploads sensitive customer data into an AI tool to draft emails more quickly. When an employee uses an
Updated on December 11, 2025.
A hardware security key is a small, physical device that provides you with access to systems, applications and accounts. Hardware security keys protect your accounts beyond traditional passwords or mobile-based authentication. They help both individuals and businesses ensure that only authorized users can access sensitive information, making them one of the most reliable and secure ways to strengthen security posture.
Continue reading to learn more about how hardware security keys work, as well as the benefits and risks of using them.
How do security keys work?
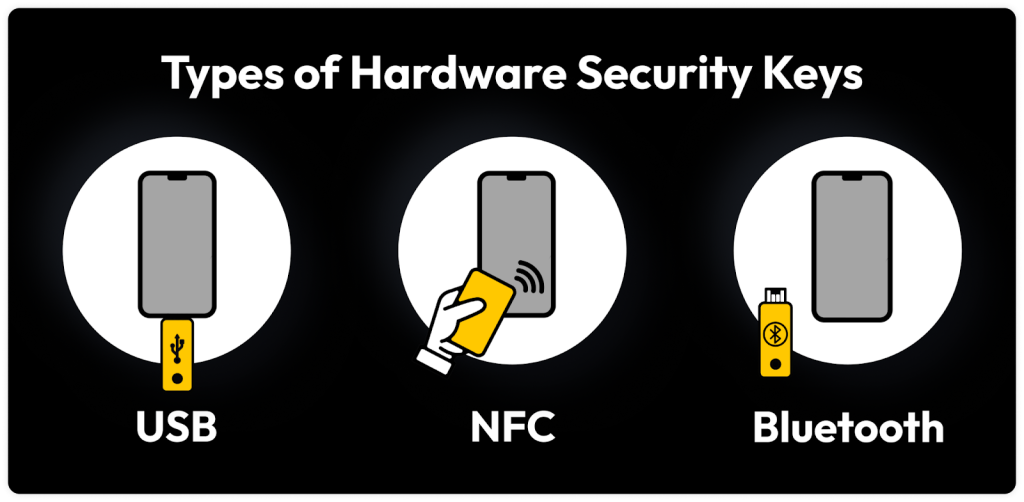
Hardware security keys use advanced encryption to verify your identity during the login process, adding an extra layer of protection against phishing attacks and data breaches. These devices connect via USB, NFC or Bluetooth and are supported by many popular platforms, including Google and Microsoft.
Once you enter your username and password, insert or tap your hardware security key to complete the login. The security key uses secure protocols like FIDO2 to create a unique digital signature that confirms your identity without ever exposing your credentials. Since the key only authenticates legitimate websites, it stops cybercriminals from gaining access, even through believable phishing attempts. As a result, a hardware security key is a highly reliable Two-Factor Authentication (2FA) method for both personal and organizational use.
Benefits and risks of using a hardware security key
Hardware security keys are one of the most secure Multi-Factor Authentication (MFA) methods available. Since they’re physical devices, they fall under the “something you have” category of authentication factors — in contrast to “something you know” (a password), “something you are” (biometrics) or “somewhere you are” (device location). Because you physically possess your hardware security key, the likelihood of unauthorized access to your account is much lower. However, hardware security keys also pose a few security risks, including cost, compatibility and risk of loss or theft.
| Benefits of hardware security keys | Risks of hardware security keys |
|---|---|
| Strong security and phishing protection | Limited compatibility |
| Convenient to use | More expensive than other authentication methods |
| Reduced risk of account takeover attacks | Risk of theft or loss |
| Works across multiple devices and platforms | Requires backup planning |
Benefits of using a hardware security key
Hardware security keys offer a simple way for users to protect their accounts against phishing and account takeovers by requiring a physical device to gain access. Because cybercriminals cannot replicate a physical device remotely, hardware security keys provide strong security and phishing protection. Unlike other MFA methods like One-Time Passwords (OTPs), security keys don’t require any code for entry, streamlining the login process with a quick tap or insertion. Many models are also designed for versatility, supporting USB, NFC or Bluetooth, so users can authenticate across multiple devices.
Risks of using a hardware security key
Despite their strong security benefits, hardware security keys have limitations, mainly in terms of compatibility. Although major platforms like Google and Microsoft support them, many smaller websites and applications do not. Their initial cost can also be an obstacle, especially for businesses that may not have the means to provide each user with a $20-$75 device. Since these security keys are very small, they can be easily misplaced or forgotten, and losing your only key to sensitive data can hinder your workflow. With hardware security keys, users must also plan ahead to avoid getting locked out of their accounts by registering a backup key or an alternative MFA method.
Use a hardware security key with Keeper®
By requiring physical authentication, hardware security keys add a strong layer of protection against phishing, credential theft and account takeover. While they require an upfront investment and some advanced planning, the security they provide exceeds the capabilities of traditional MFA methods. Keeper® supports YubiKey, FIDO2 and WebAuthn security keys, including those with Lightning connectors and NFC for efficient use across devices. Keeper integrates seamlessly with your preferred hardware security key to secure both personal accounts and entire organizations.
Keeper Password Manager helps enhance your login experience by supporting hardware security keys. Start a free trial today to see how Keeper makes it easy to store your MFA methods.
Frequently asked questions
What happens if I lose or misplace my security key?
If you lose your security key, your accounts remain protected, but you may be locked out of them until you use a backup MFA method. To avoid losing access to your accounts, always set up an alternative MFA method, such as an OTP code or biometric authentication. Platforms like Google, Microsoft and Keeper support multiple registered security keys.
Is a security key just a USB?
No, security keys do much more than USBs. A hardware security key contains a secure chip that uses encryption to verify your identity, whereas a USB simply stores files. Modern security keys come in various formats, such as Lightning and NFC, allowing them to work across different devices.
How do I set up a hardware security key?
To set up a hardware security key, you must first purchase a compatible key and make sure it works with your device’s connection type (USB, NFC, Lightning, etc.). Next, visit your account’s security settings and find an option similar to Add a security key. Once you follow the on-screen instructions, your security key will be registered, and you’ll insert or tap the key when prompted to complete the setup.


