New research shows Microsoft Edge loads all saved passwords into memory in plain text, and Keeper Forcefield is built to protect against exactly this kind of
Updated on December 9, 2025.
A One-Time Password (OTP) is an automatically generated code used to verify a user’s identity during a login attempt. Unlike traditional passwords that can be stolen or reused, OTPs are valid for a single use, expire within seconds and provide strong protection against unauthorized access. Both individuals and organizations rely on OTPs as a form of Multi-Factor Authentication (MFA) to verify user identity before granting access to sensitive information.
Continue reading to learn more about OTPs, the benefits of using them and how you can start receiving them.
Types of OTPs
While OTP is the umbrella term for any password designed to be used once, there are two main types of OTPs: Time-Based One-Time Passwords (TOTPs) and HMAC-Based One-Time Passwords (HOTPs).
Time-Based One-Time Password (TOTP)
A Time-Based One-Time Password (TOTP) generates a unique code that remains valid for a short period of time — generally 30 to 60 seconds. During setup, the user scans a QR code or manually enters a secret key provided by the service on which they’re enabling MFA. The shared secret is stored both on the server and in the authenticator app or password manager. The authenticator then uses the secret key and the current time to generate a new code. When logging in, the user enters the code before it expires, allowing them to complete the authentication process.
HMAC-Based One-Time Password (HOTP)
HMAC-Based One-Time Passwords (HOTPs) generate codes based on a counter rather than time. With HOTPs, each time a new OTP is requested, the counter increases. For example, when a user requests a new code from their authenticator app, the algorithm moves to the next number in its built-in counter to produce the next HOTP code. Since these codes aren’t time-bound, an HOTP remains valid until it’s used or replaced, making it more flexible but less commonly used than TOTPs due to security concerns.
OTP vs TOTP vs HOTP: What’s the difference?
Although TOTPs and HOTPs fall under the broad category of OTPs, each type behaves differently and presents varying security benefits. Here’s how they compare.
| Feature | OTP | TOTP | HOTP |
|---|---|---|---|
| How codes are generated | Depends on the service and the level of security needed | Uses shared secret and current time | Uses shared secret and incremental counter |
| Validity period | Varies; can expire in seconds or remain valid until used | Typically 30 to 60 seconds | Until used or regenerated |
| Security strength | Varies by method; SMS-based is less secure than authenticator app-based | High security; time-based codes reduce risks | Moderate security; longer validity window introduces risks |
| Common use cases | General MFA, password resets, login verification | Authenticator apps, password managers | Hardware tokens, offline environments |
Benefits of using OTPs
By ensuring that each code can only be used once, and often within a short timeframe, OTPs make it much more challenging for cybercriminals to compromise accounts. Here are several of the main benefits of using OTPs:
- Helps prevent account compromise: Even if your username and password are compromised, cybercriminals cannot log in without the OTP, stopping many unauthorized login attempts.
- Defends against replay attacks: Since OTPs are only valid once, cybercriminals cannot intercept or reuse them in a replay attack. Once expired or used, the code becomes invalid, rendering it useless to cybercriminals.
- Minimizes risks from password reuse: If you reuse the same password (which you shouldn’t do), having an OTP helps prevent cybercriminals from using that same password to access your other accounts.
- Limits the exploitation window: TOTPs specifically refresh every 30 to 60 seconds, limiting the amount of time a cybercriminal who successfully intercepts or guesses the code can actually use it.
- Reduces phishing success: OTPs make it more challenging for cybercriminals to gain access to an account through phishing attempts because, even if a user shares their password, the OTP is still required and cannot be reused.
How to receive an OTP
- SMS: The OTP is delivered to your phone as a text message. While this method is convenient and commonly used, SMS is the least secure way to receive OTPs since text messages are vulnerable to SIM swapping and interception.
- Phone call: Some services offer OTP delivery through an automated phone call. If you don’t have text messaging available, this may be a good alternative; however, it is less convenient for frequent logins.
- Email: The OTP is sent to your inbox. Although it’s easy to access your email on multiple devices, email-based OTPs can be intercepted if your email is compromised.
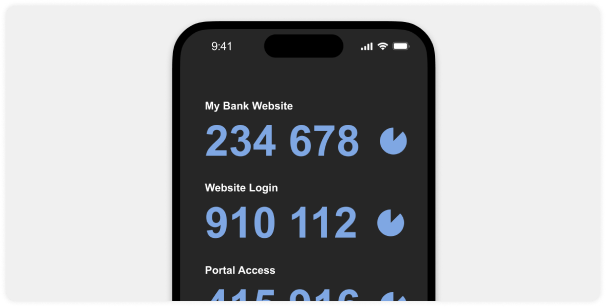
- Authenticator app: Apps like Google Authenticator, Microsoft Authenticator and Keeper® generate TOTPs directly on your device. These codes refresh automatically every 30-60 seconds and do not rely on an external network, making this method one of the most secure options available.
It’s important to note that not all websites support the use of OTPs, so you should still use a strong, unique password for each account and enable other types of MFA.
Secure your accounts with strong passwords and OTPs
OTPs are a simple yet powerful way to secure your accounts, prevent credential theft and stop phishing attempts from becoming successful. However, managing both passwords and OTPs across multiple accounts can become overwhelming. Luckily, Keeper Password Manager simplifies this by generating and storing strong, unique passwords and OTPs in a single, encrypted vault. By using Keeper’s built-in TOTP generator, you can protect both your personal and business accounts without needing to remember every code, and when you need to share sensitive information, Keeper’s One-Time Share feature provides a secure, time-limited way to send data without exposing your credentials.
Frequently asked questions
What is an example of a one-time password?
A One-Time Password (OTP) is a short code like 246019 sent via SMS, email or generated from an authenticator app. An example of how it can be used is when logging in to your banking app. Once you receive an OTP, you enter it along with your traditional password. The code typically expires within 30-60 seconds (for TOTPs) or becomes invalid after it’s used (for HOTPs), adding an additional layer of security to your account.
What are the disadvantages of a one-time password?
While One-Time Passwords (OTPs) increase your accounts’ security, they have several drawbacks:
– Delivery issues: SMS or email-based OTPs may be delayed or fail to arrive, causing problems and frustration if you need an OTP urgently.
– Extra login step: Having to enter an OTP adds more friction to the login process, which some users may find inconvenient compared to just entering a username and password.
– Dependency on a device: Sometimes, authenticator apps are required to receive OTPs, so losing your device may temporarily lock you out of your account.
Despite these disadvantages, OTPs remain a strong security measure, especially when combined with strong, unique passwords and the use of a password manager like Keeper.
Are one-time passwords safe?
Yes, One-Time Passwords (OTPs) are generally safe and provide an additional layer of security beyond traditional passwords. Since each code can only be used once, OTPs reduce the risk of account compromise from stolen or reused passwords. TOTPs generated by authenticator apps are especially secure because they don’t rely on methods like SMS or email, which are more vulnerable to interception.


