Imagine a customer service representative at your organization uploads sensitive customer data into an AI tool to draft emails more quickly. When an employee uses an
Updated on July 31, 2024.
A phishing attack is a type of social engineering attack that attempts to persuade someone to disclose sensitive information. When people are not aware of phishing attacks, they tend to fall for them, which can result in the loss of sensitive information such as credentials and credit card numbers.
Continue reading to learn ten types of phishing attacks and how to stay protected against them.
1. Smishing
Smishing, also known as SMS phishing, is when you receive a text message asking you to click on a link. The message can be worded as though it contains an offer for a free product or an urgent alert. The attacker may use personal information from their victim in an attempt to convince them that the message is real so they will disclose sensitive data.
2. Vishing
Vishing is similar to smishing, but it takes place through a phone call rather than a text message. Victims of vishing attacks are often more convinced because they’re talking to another person on the other end of the phone. This can make the victim more likely to disclose sensitive information without second-guessing themselves.
3. Clone phishing
Clone phishing is when an attacker clones an email from a legitimate company and resends it to their victim. However, the cloned email contains malicious links and malware that will infect the victim’s device if they click on them. This can place the victim’s personal information at risk of becoming compromised or stolen.
4. Whaling
Whaling is a type of phishing attack that targets high-profile individuals rather than everyday people. An example of a high-profile person would be the CEO of a company. The goal of this type of attack is to gain access to high-level data or classified information.
5. Pharming
Pharming is a type of phishing attack where the victim is redirected from a legitimate site to a spoofed one. A spoofed website is a site that is designed to look legitimate but is used to steal personal information. The purpose of the redirect is to get the victim to enter their personal information on the spoofed site so the cybercriminals can steal it.
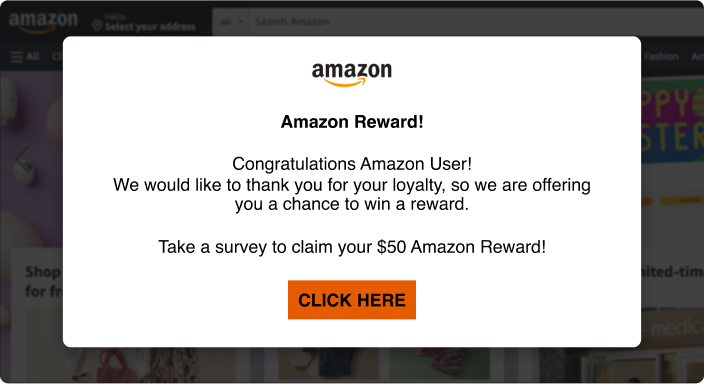
6. Pop-up phishing
Pop-up phishing is when a message pops up as an individual is surfing the web that tells the potential victim something is wrong with the security of their device. For example, it could say something like “WARNING! Your computer may have a virus.” It’ll then prompt you to scan your device, but doing this will infect your device with malware. Once the malware is installed, attackers can steal your data or prevent you from accessing your files, depending on the type of malware installed.
7. Spear phishing
With spear phishing, an attacker must have prior information about their victim, such as their full name, phone number and address. Spear phishing can take place through email, text messages or phone calls. During this type of attack, the victim is easily convinced because the attacker has information about them that makes them sound legitimate and trustworthy.
8. Evil twin phishing
Evil twin phishing is when an attacker sets up a fake WiFi access point. Instead of clicking on a legitimate WiFi network, victims will click on the fake one and once they do, everything they share over the network is passed through a server that is controlled by the attacker. The attacker will be able to see everything they do, including when they log into their accounts and enter sensitive information such as credit card numbers. This type of attack is more likely to occur when the victim is trying to access a public WiFi network.
9. Angler phishing
Angler phishing is when an attacker poses as a Customer Service Representative (CSR) in an attempt to convince the victim to disclose their personal information. Since the victim believes it’s a legitimate CSR, they give out their information with no hesitation.
10. HTTPS phishing
HTTPS phishing is when an attacker creates a spoofed site that uses the Hypertext Transfer Protocol Secure (HTTPS). Most sites have HTTPS in the URL bar, where it appears as a lock icon. HTTPS is a standard protocol that is meant to ensure that a site’s connection is secure because it encrypts traffic between a browser and a site. However, many attackers have been abusing HTTPS to get victims to trust spoofed sites. Spoofed sites are not secure, but a fake HTTPS makes it look like they are. Because of this, victims are more likely to enter their information into the spoofed site.

How to protect yourself from phishing attacks
Now that you know some of the most common types of phishing attacks, here are some of the ways you can protect yourself from falling victim to them.
Stay informed about the latest phishing threats
One of the best ways you can protect yourself from phishing attacks is by knowing what they are and keeping up to date on the latest phishing scams that are making headlines. Phishing scams are more likely to occur during big events like tax season, which is often when attackers pose as the IRS. Being vigilant about the latest phishing scams can make all the difference in keeping yourself and your information safe.
Use a password manager
A password manager is a solution that aids with creating, securely storing and managing multiple passwords. A little-known benefit to using a password manager is that it can also help you detect phishing websites. If your saved login information isn’t showing up on the website you visit, you’re probably on the wrong site and should exit it immediately. For example, when you store login information using Keeper Password Manager, the website address is also saved so your credentials can be auto-filled when you go to the site. If Keeper isn’t prompting you to enter your credentials, then you’re most likely on a phishing site.
Don’t click on unsolicited links or attachments
Always remember that you should not click on any links or attachments that you receive unsolicited, especially from people you do not know. As an extra precaution, before clicking on links, check to see if they’re safe. One way you can do this is by hovering your mouse over the link to check if the URL looks “phishy.” You can also use a URL checker like the Google Transparency Report to ensure that the URL is safe to click. If it’s not, make sure you report it to the company the attacker is impersonating so they can warn other customers.
Ensure you have MFA enabled on your accounts
If you were to fall victim to a phishing attack and the attacker gets away with your credentials, having Multi-Factor Authentication (MFA) helps prevent your accounts from being compromised. MFA adds one or more authentication methods in addition to your username and password. So even if the attacker knows your login credentials, they still wouldn’t be able to log in to your accounts without that additional verification.
Don’t respond to anyone who asks you to reveal personal information
Anyone you don’t know or haven’t reached out to who asks you for your sensitive and personal information is a red flag. While most phishing attacks use scare tactics as a way to get victims to reveal their information, it’s important that you stand your ground by not falling for them. Unless you personally reach out to a company, a legitimate company will never ask you to disclose sensitive information.
Regularly back up your data
Many phishing attacks can result in your device being infected with malware. Certain types of malware, such as ransomware, may prevent you from being able to access your files, so it’s important that you always have your personal data backed up in a secure location. The best way you can do this is by storing your information in a password manager that offers file storage. Keeper Password Manager offers an add-on called Secure File Storage, which allows you to store different types of files and securely access them from anywhere. There’s no need to worry about losing access to your files because they’ll be backed up in an encrypted location.
Stay safe against phishing attacks
Phishing attacks can lead to your personal information being stolen and used for malicious purposes, which is why you must learn how to stay protected against phishing attacks. Investing in a password manager like Keeper® can keep you safe from unknowingly giving away your login credentials.
Start protecting your login credentials today by starting a free 30-day trial of Keeper.


