What can you share with Keeper?
- Passwords
- Passkeys
- Files and documents
- Payment information
- Two-factor codes
- Confidential notes
- IT documentation
- SSH keys and digital certificates
- Access to privileged accounts
Whether you're collaborating with a team or managing a household, Keeper lets you share securely, instantly and without risk.
Share records or folders with specific users on an ongoing basis. These shares remain active until manually revoked and are ideal for teams or individuals who need continual access to shared items.
Grant temporary access to a record or folder for a defined duration, after which access is automatically revoked. Unlike self-destructing shares, the record can be viewed multiple times during the allowed window.
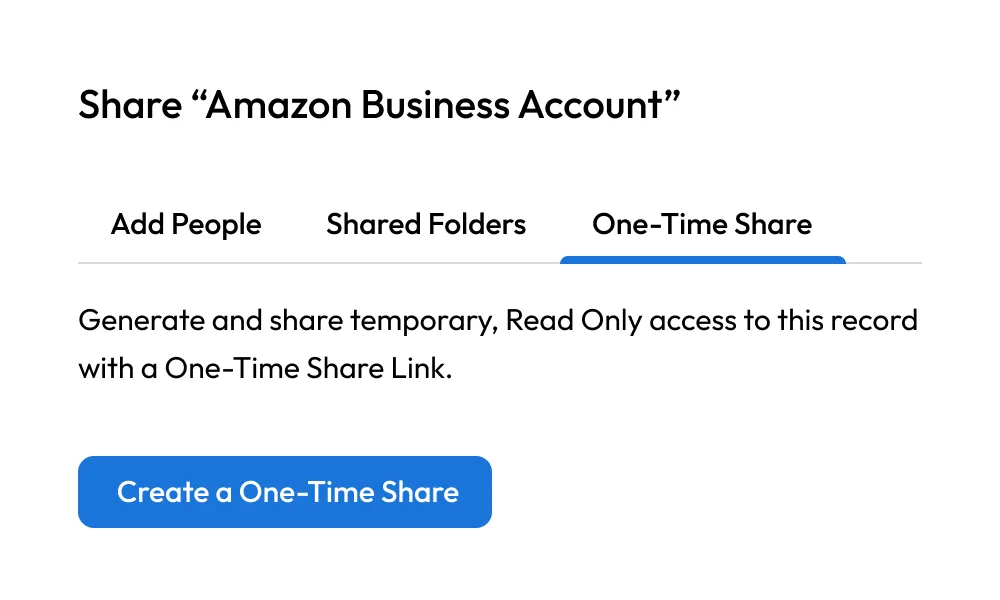
Single-use, view-once links that immediately expire after being accessed. This method ensures that sensitive information is only visible for a moment in time and cannot be accessed again.
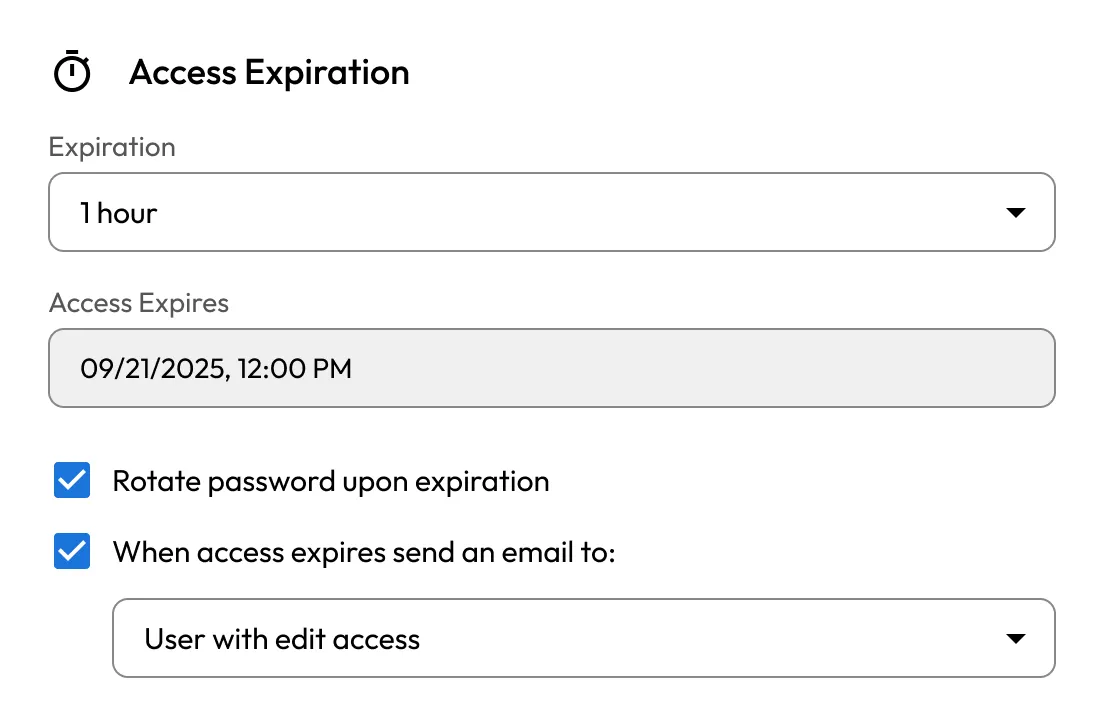
Grant temporary access to shared records or folders, ideal for vendors, contractors and rotating teams. Privileged accounts can be automatically rotated after the share has expired.
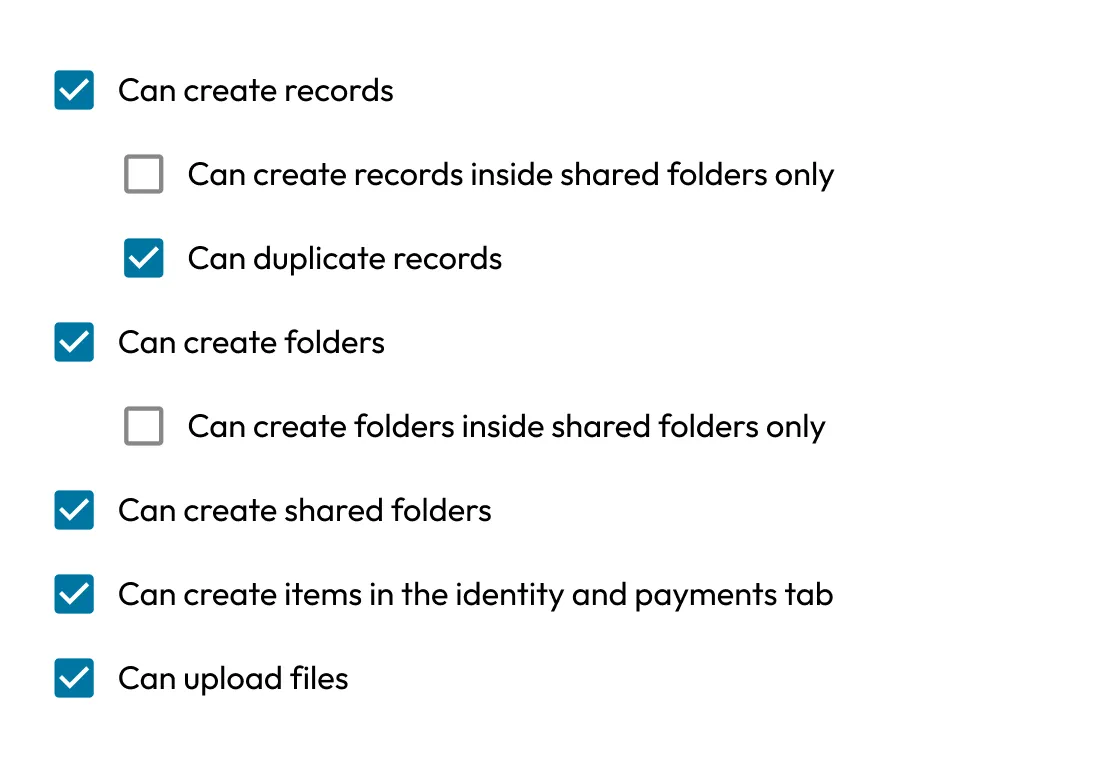
Granular permission system offers over 80 vault and role-level permissions across 14 categories, with extensive policy controls and clear audit trails — purpose-built for enterprise governance and compliance.
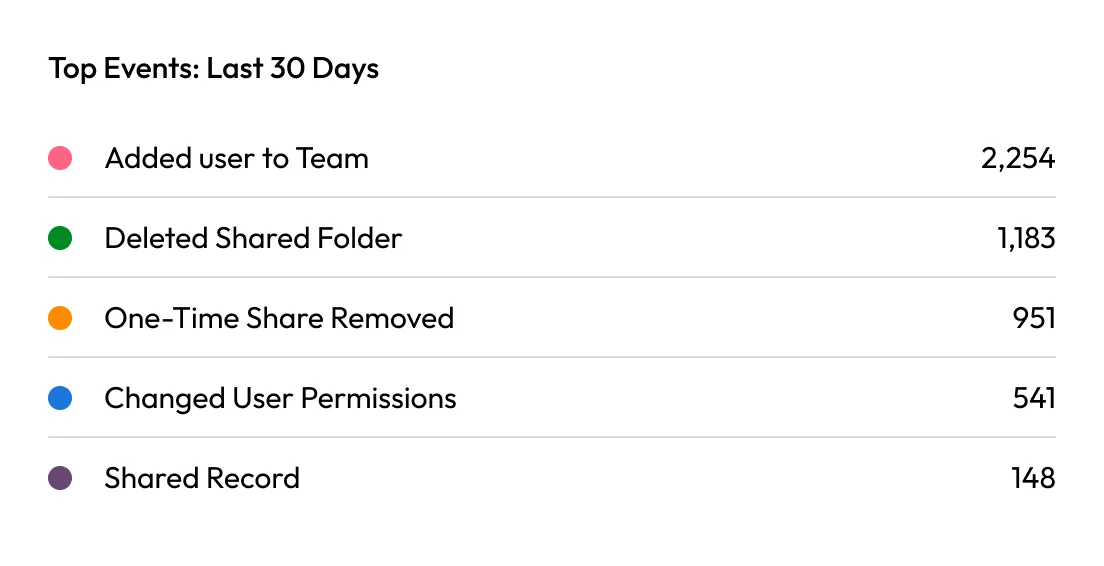
Get alerts when records are accessed or modified. Log events to SIEMs or receive notifications through email, Slack or Teams.
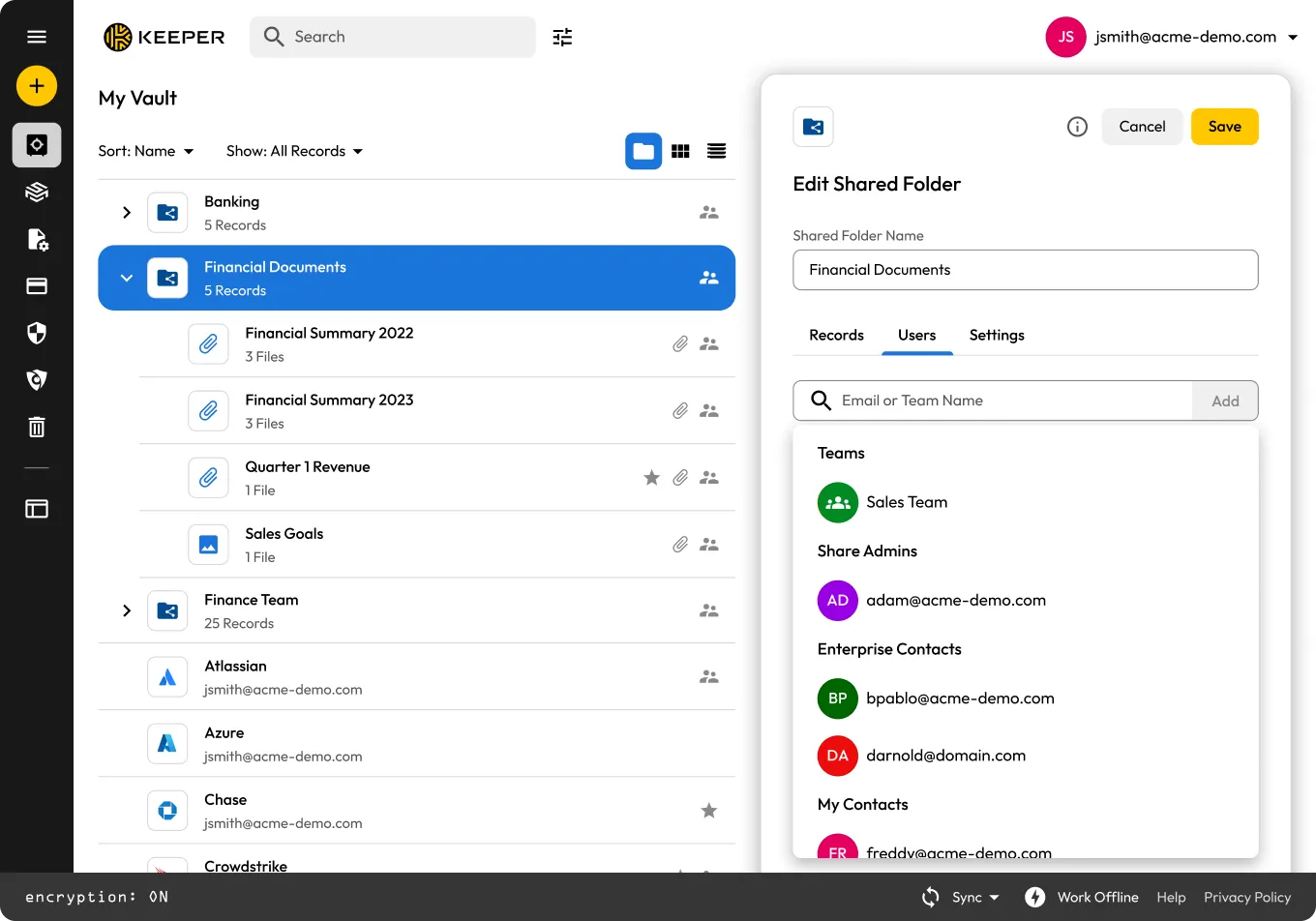
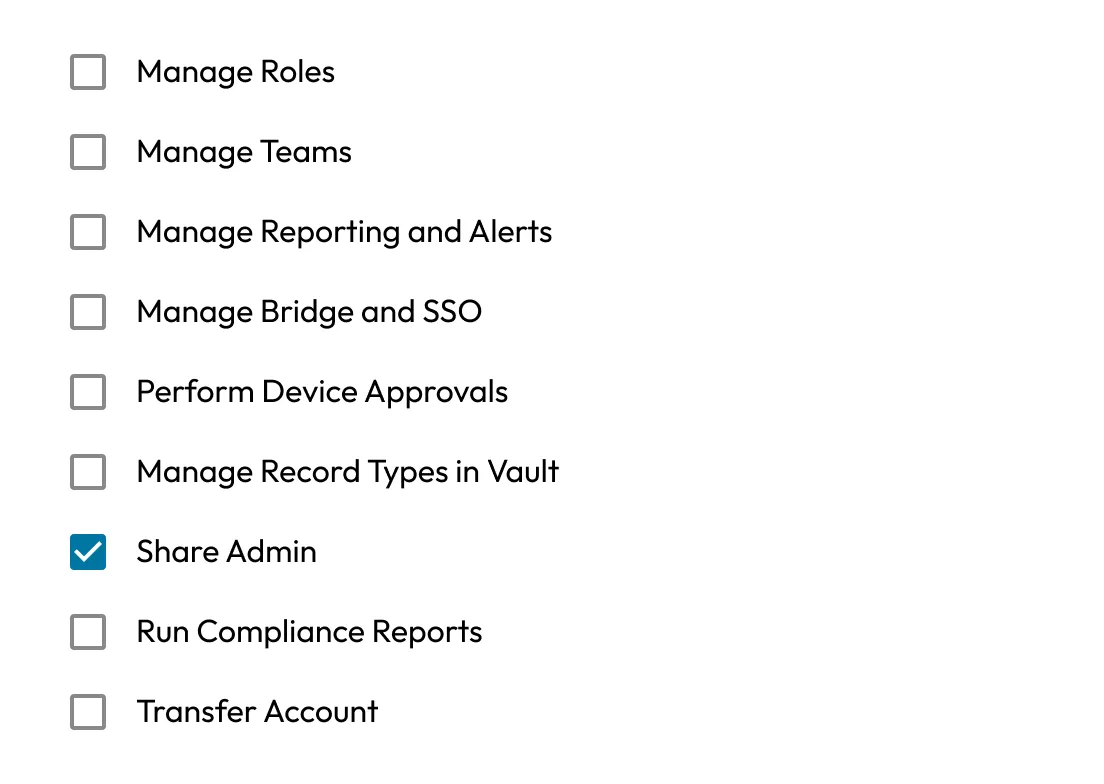
Designate “Share Administrators” to oversee permissions, transfer ownership and manage shared data organization-wide.
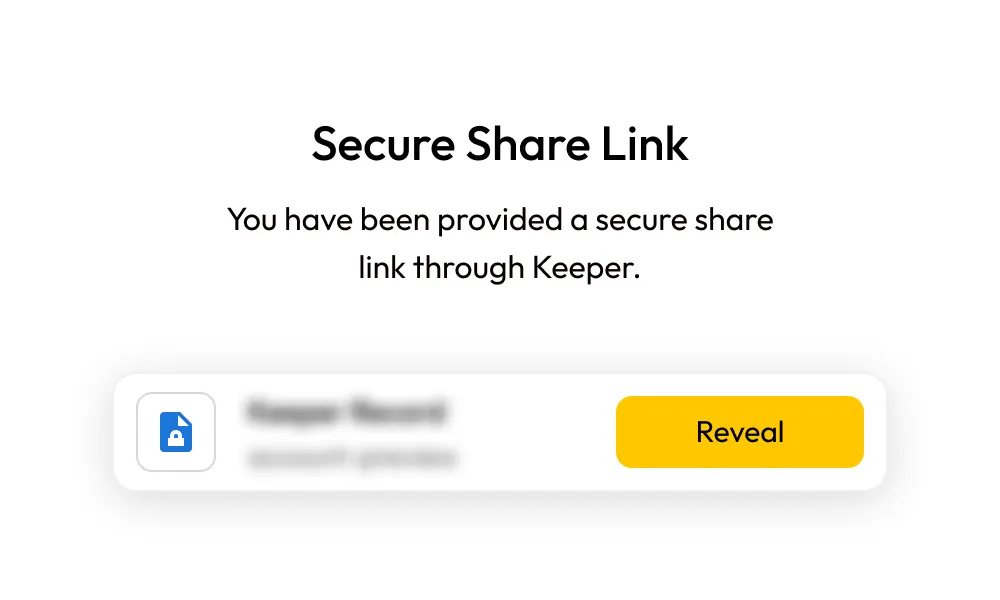
Send login details, WiFi passwords or payment information to anyone, even if they don’t use Keeper.
You decide who has access and for how long, and you can change or revoke it at any time.
Yes, with One-Time Share, you can grant time-limited access to a Keeper record, even if the recipient doesn’t have a Keeper account.
Yes, you can share passkeys with other Keeper users, using the same vault-to-vault sharing mechanism used for passwords and other records. The recipient receives the shared passkey encrypted for them and can access it according to the permissions you set.
Yes, you can set granular permissions, such as View Only, Can Edit or Change Owner. You can also revoke access at any time.
You can revoke access instantly from your vault. The recipient will no longer be able to view or interact with the shared record. Here’s how:
Sharing features vary by plan:
Free: No sharing capabilities; access is limited to local storage on a single mobile device.
Unlimited and Family: Includes secure record sharing, vault-to-vault sharing and One-Time Share with non-Keeper users.
Business and Enterprise: Full sharing capabilities, including team-based sharing, shared folders, role-based access controls and One-Time Share with external users.
You can share both! Keeper supports Shared Folders, allowing you to organize and share multiple records with groups or individuals.
Yes, all data is protected using Keeper’s zero-knowledge architecture and AES 256-bit encryption, both at rest and in transit.
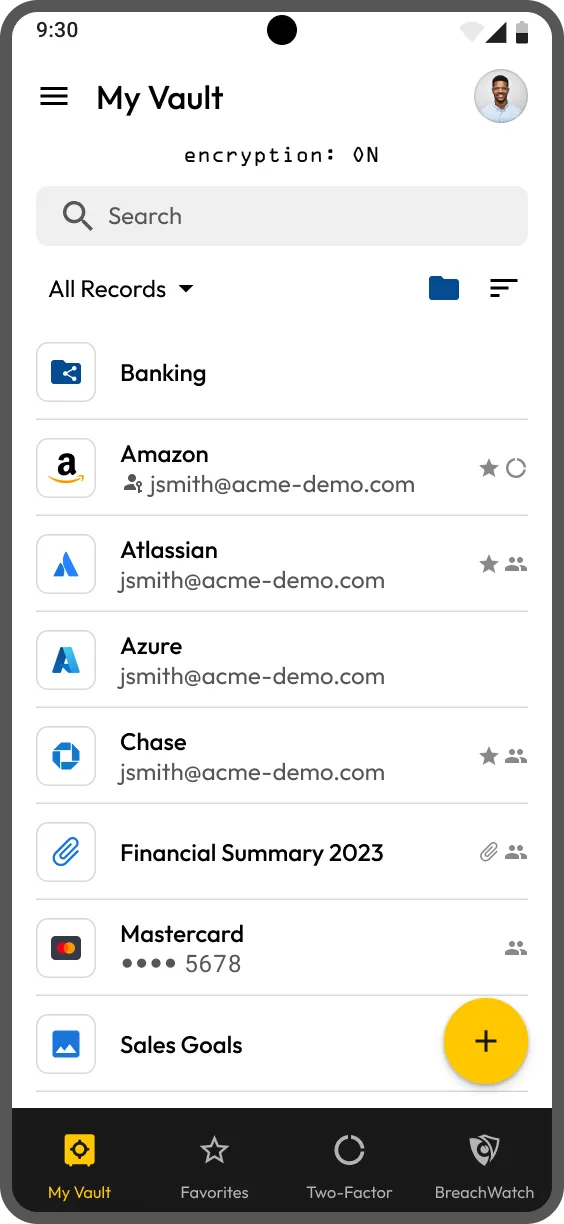
Yes, Keeper’s secure sharing is available across web, desktop and mobile apps, so you can share safely from anywhere.
You must accept cookies to use Live Chat.