メールスプーフィング
サイバー犯罪者は、送信元のメールアドレスを偽装し、銀行や医療機関などの信頼できる組織から送られてきたかのように見せかけます。送信元ドメインを改ざんしたうえで、悪意のあるリンクを通じてマルウェアをダウンロードさせたり、認証情報を入力させたりして、被害者をだまします。
サイバー脅威: スプーフィング攻撃
スプーフィング攻撃は、サイバー犯罪者が実在する企業やウェブサイト、知人などを装って行う攻撃です。主な目的は、パスワード、クレジットカード情報、その他の個人識別情報 (PII) を共有させて、だまし取ることです。
サイバー犯罪者は、送信元のメールアドレスを偽装し、銀行や医療機関などの信頼できる組織から送られてきたかのように見せかけます。送信元ドメインを改ざんしたうえで、悪意のあるリンクを通じてマルウェアをダウンロードさせたり、認証情報を入力させたりして、被害者をだまします。
サイバー犯罪者は、本物のサイトを模倣した偽のウェブサイトを作成し、ログイン認証情報を盗み取ろうとします。これらのページは、ロゴや配色、レイアウトが本物とほぼ同じに作られているため、一見しただけでは正規のサイトと見分けるのが困難です。

インターネットプロトコル (IP) のなりすましでは、サイバー犯罪者はIPアドレスを偽装し、別のデバイスやネットワークになりすまします。この攻撃は、システムに大量のトラフィックを送りつける分散型サービス拒否 (DDoS) 攻撃の際によく使用され、攻撃者の身元を隠す目的でも利用されます。

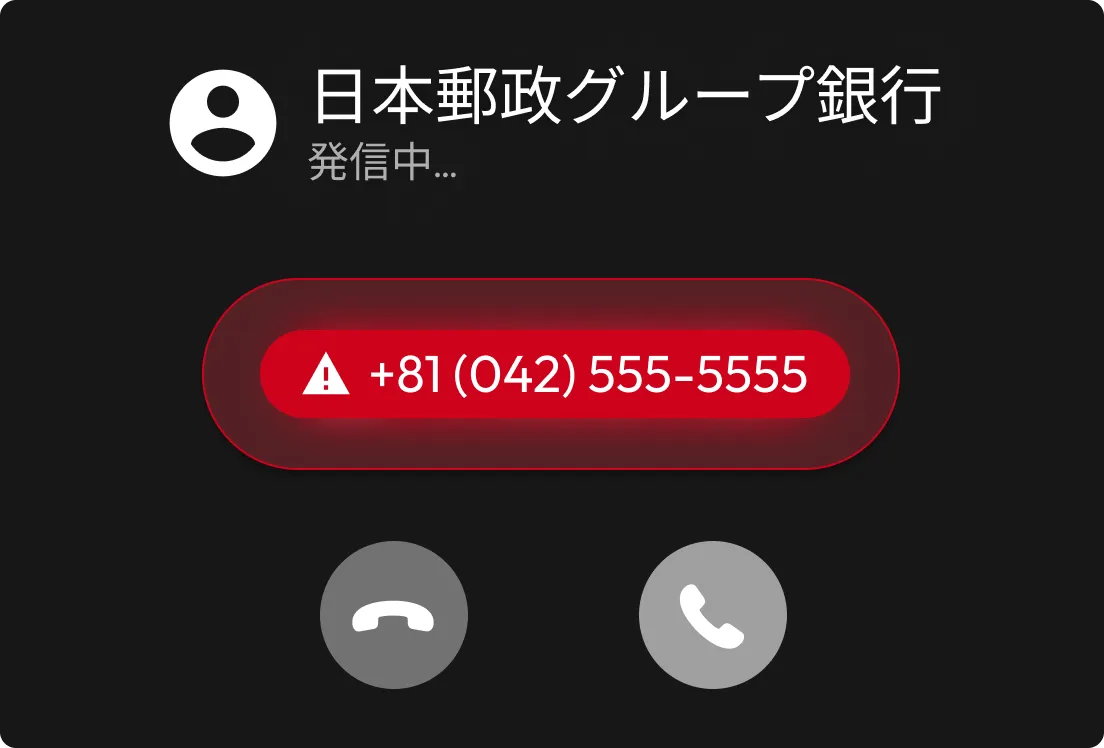
なりすまし電話とも呼ばれ、電話の着信時に表示される番号を操作して、金融機関や政府機関などの信頼できる組織になりすます手口です。サイバー犯罪者は、クレジットカード情報やワンタイムパスワード (OTP) などの機密情報を電話口で聞き出そうとします。
スミッシングとも呼ばれ、サイバー犯罪者が正規の企業の電話番号を装ってSMS (ショートメール) を送信する手口です。これらのメッセージでは、緊急性をあおる表現を用いてリンクのクリックやアカウント情報の確認、セキュリティコードの入力を促します。

サイバー犯罪者は、正規のものに見せかけるために、メールアドレスや電話番号、IPアドレス、ウェブサイトのURLなどを偽装します。信頼を得た後、悪意のあるリンクのクリック、感染した添付ファイルのダウンロード、あるいは偽のログインページへの認証情報の入力を促します。スプーフィング攻撃は、機密情報の窃取、金銭的詐欺の実行、重要なアカウントへの不正アクセスを目的としています。

すぐに行動するよう促すメッセージは、スプーフィング攻撃の典型的な兆候です。サイバー犯罪者は、冷静に判断する時間を与えないよう不安をあおり、「アカウントが停止されます!」や「今すぐパスワードを確認してください!」といったメッセージを送ります。

偽のウェブサイトは、正規のドメイン名にわずかな変更を加えることで、疑いを持たないユーザーをだまし、ログイン情報を入力させようとします。

かつては、誤字脱字や不自然な文法がスプーフィングの明確な兆候とされていましたが、現在ではサイバー犯罪者がAIを利用して本物らしいメッセージを作成しています。そのため、文法上の誤りだけで判断するのではなく、組織の公式なブランド表現と異なる不自然な言い回しや文体がないかにも注意しましょう。
パスワードマネージャーは、ボルトに保存されたURLと一致するウェブサイトでのみログイン情報を自動入力するため、スプーフィングのリスクを軽減します。これにより、偽サイトに誤って認証情報を入力してしまう可能性を大幅に低減できます。
多要素認証 (MFA) を有効にすると追加の認証ステップが求められるため、アカウントの保護が強化されます。たとえパスワードを知られていたとしても、サイバー犯罪者がアカウントにアクセスすることはほぼ不可能です。
送信元が不明な相手から届いたリンクのクリックや、添付ファイルのダウンロードは避けましょう。メッセージに対応する前に、必ず送信元を確認してください。
正規の組織が、メールやSMS、電話で機密情報を要求することはありません。依頼が本物かどうか判断に迷う場合は、公式ウェブサイトに掲載されている連絡先を利用して、企業に直接確認しましょう。
![大文字、小文字、数字、記号を組み合わせた、強力な自動生成パスワードのイラスト。パスワード生成ツールで緑色の強度メーターと [強力] というラベルの付いた盾のアイコンが、パスワードセキュリティが高いことを示しています。](/assets/images/pages/threats/spoofing-attack/ja_JP/spoofing-mini-animation-2-desktop@2x.webp)
スプーフィング攻撃に陥った場合でも、Keeperボルトに強力で一意なパスワードを保存しておくことで、パスワードの使い回しを防止。複数のプラットフォームにわたるアカウントの不正アクセスを防ぎます。
BreachWatch®は、認証情報が公開されたデータ侵害に含まれていることが確認された場合、ダークウェブアラートをリアルタイムで通知。サイバー犯罪者に悪用される前に迅速な対応が可能になります。
チャットサポートを利用する場合、Cookie を有効にしてください。