Keeper Security has once again been recognized by the German technology publication connect professional. In its latest independent test, Keeper Endpoint Privilege Manager (EPM) received a
Many business customers have migrated from LastPass to Keeper over the past several years. As a result of recent news surrounding LastPass’ data breach, customers are asking what they should do to ensure passwords migrated from LastPass to Keeper are updated, in case backup files from LastPass that may remain on LastPass’ infrastructure, have been accessed by the attackers.
Business customers who subscribe to the Advanced Reporting & Alerts Module (“ARAM”) and the Compliance Reports module are able to perform a “password aging” report, which can identify passwords that may require updates. The report is executed through the Keeper Commander CLI tool, which is available for Windows, macOS and Linux environments. If you’re a Keeper Business or Enterprise customer who does not currently have ARAM or Compliance Reports, you can activate these features in your Keeper Admin Console.
To run a password aging report, follow the steps below:
1. Ensure ARAM and Compliance Reports are Active
Log in to the Keeper Admin Console as an administrator and visit the “Subscriptions” tab. Ensure your enterprise license includes Advanced Reporting & Alerts, and Compliance Reporting. The password aging report makes use of the audit and compliance data feeds available to customers who subscribe to these services.
If you have any questions regarding the Advanced Reporting & Alerts or the Compliance Reporting modules, please contact your Keeper customer success team or visit the links below.
- https://docs.keeper.io/enterprise-guide/event-reporting
- https://docs.keeper.io/enterprise-guide/compliance-reports
2. Install Keeper Commander
Keeper Commander is a command-line and SDK interface to Keeper Enterprise. Commander can be used to access and control your Keeper vault, run reports and perform advanced administration. Keeper Commander is an open source project with contributions from Keeper’s engineering team and partners.
Installation instructions are here: https://docs.keeper.io/secrets-manager/commander-cli/commander-installation-setup
Note: If you already have Keeper Commander, ensure you are using the latest version.
3. Login to Commander
To log in to Keeper Commander, either run the binary application or run “keeper shell” from the terminal.
$ keeper shellYou can then log into Commander using a Master Password or SSO.
More information about logging into Commander can be found here: https://docs.keeper.io/secrets-manager/commander-cli/using-commander/logging-in
4. Run Aging Report
The first step in running a password aging report is to download and process the audit and compliance data. This is performed by running the following command:
aging-report --rebuildThis command might take several minutes (or more) to complete depending on the number of records stored.
As an example, to look at any passwords that have NOT been updated in over 1 year, input:
aging-report --period 1yTo drill down into owned records for a specific user within the organization:
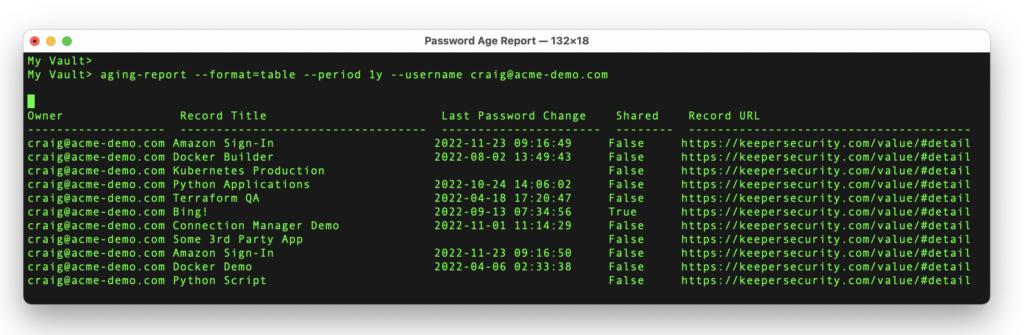
aging-report --period 1y --username user@company.comExample output:
To export the data in a CSV formatted output (for import into a spreadsheet or database), use the “format” option. For example:
aging-report --period=1y --format=csv --output=report.csv --username user@company.comMore information about the aging report can be found by typing:
aging-report --helpYou can also visit the link below:
The output of the aging report will tell you which record passwords have NOT been updated in the requested time period. The “Last Password Change” column represents the date of the last password change event. The “Record Title” is decrypted locally either using the current user’s private keys or the enterprise key, depending on the level of administrative access. The “Shared” column indicates if the record is shared with other users. The Record URL contains the direct hyperlink to the Web Vault and Record UID that can be used for further investigation.
5. Delete Local Files
After you have run the necessary reports, we recommend deleting any files on disk which contain plaintext reports. The use of the aging report will store a local file in the Keeper Commander working directory called sox_<ID>.db which is an SQLite file that contains encrypted data used during the generation of the report. We recommend deleting this file from the filesystem once you are finished analyzing data.
If you have any questions or need help, please email us at commander@keepersecurity.com.


