What is a break glass account?
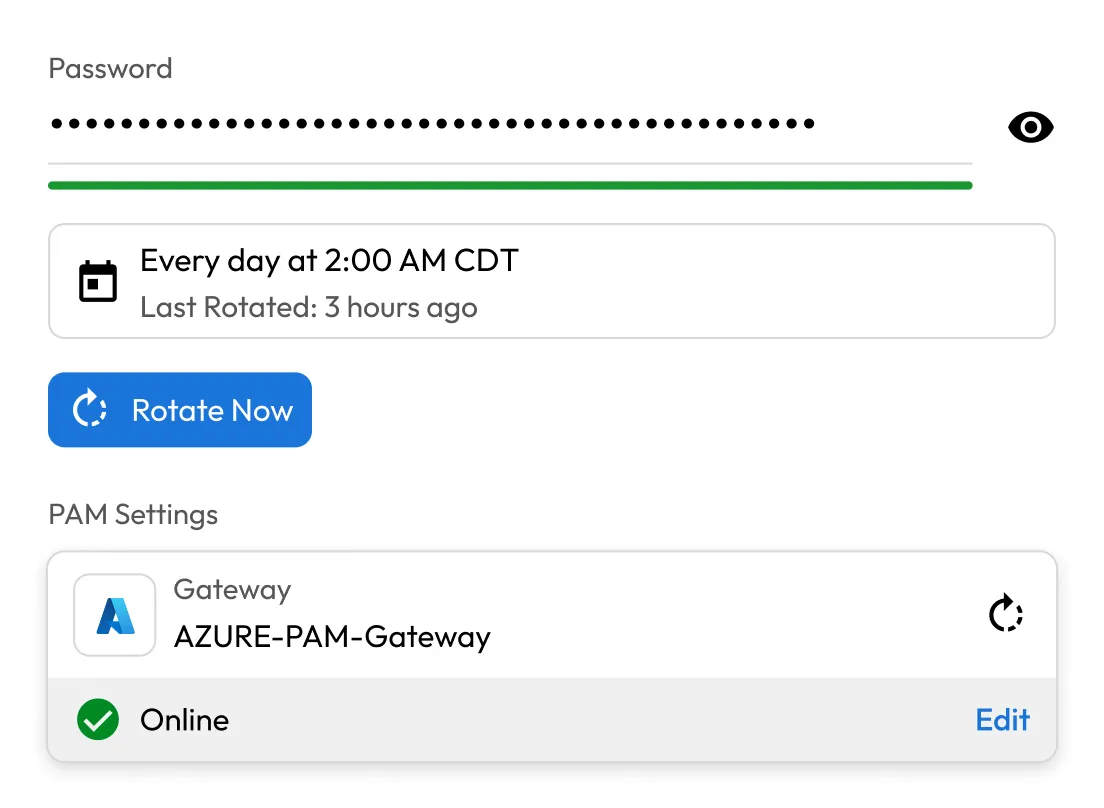
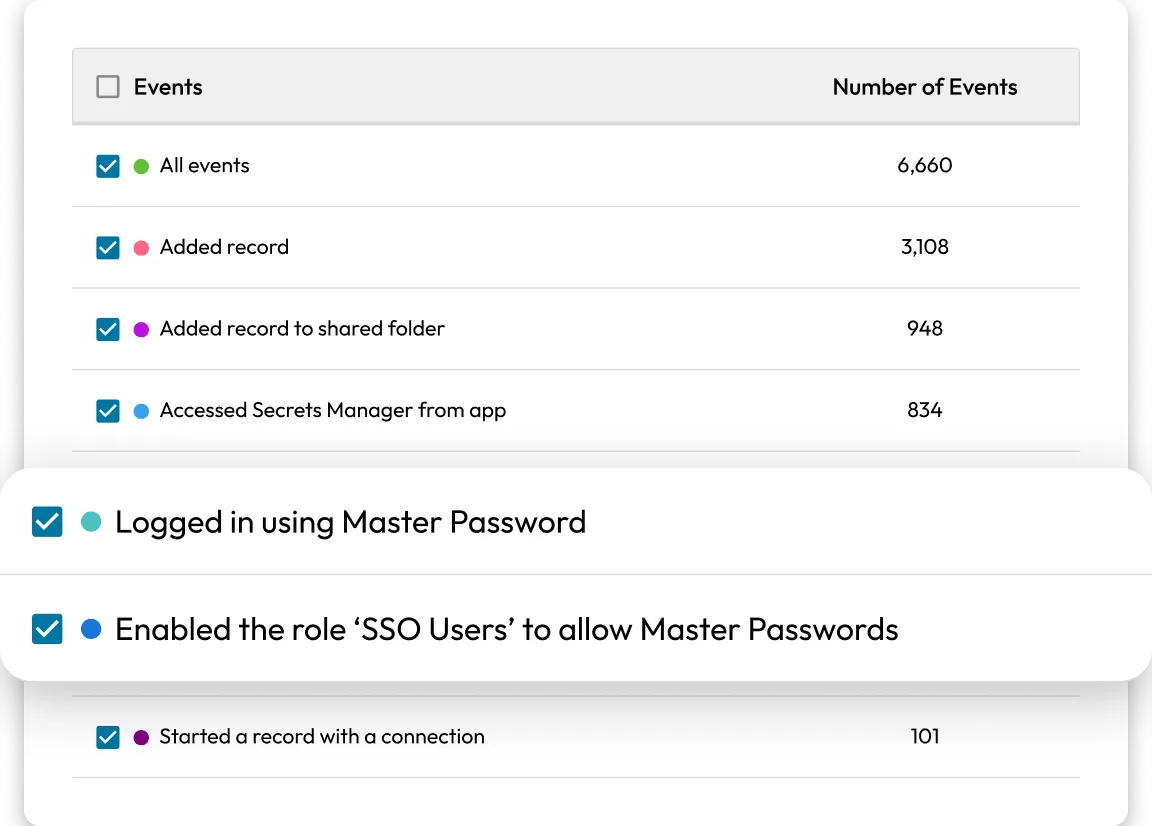
A break glass account is a dedicated Keeper administrator account that is intentionally not tied to SSO, IdP integrations, directory sync or other external dependencies. This account is protected with a strong master password and MFA, allowing designated administrators to sign in directly to Keeper during emergency situations such as:
- Identity provider outages
- SSO misconfigurations
- Network or VPN failures
- Infrastructure or directory synchronization disruptions