What Is a Supply Chain Attack?
Supply chain attacks target vendors and suppliers instead of directly targeting a specific business. Protect your organisation against these attacks with privileged access management.

Understanding Supply Chain Attacks
A supply chain attack, which is also known as a third-party attack, value-chain attack or backdoor breach, is when a cybercriminal accesses a business’s network via third-party vendors or through the supply chain. Supply chains can be massive and complex, which is why some attacks are so difficult to trace.
Many businesses work with dozens of suppliers for everything from ingredients or production materials to outsourced work and technology. This is why it’s so important to protect the supply chain and ensure the companies you’re working with are as committed to security as you are.
Supply chain attacks are a type of cyber attack that is often overlooked. This type of attack can cause catastrophic damage over time and can be more difficult to detect and prevent if your vendors aren’t maintaining strict cybersecurity policies and using the best tools.
How Do Supply Chain Attacks Work?
Supply chain attacks work by delivering viruses or other malicious software via a supplier or vendor. For example, a keylogger placed on a USB drive can make its way into a large retail company, which then logs keystrokes to determine passwords to employee accounts. Cybercriminals can then gain access to sensitive company information, customer records, payment information and more.
Examples of Supply Chain Attacks

Software Supply Chain Attack
A software supply chain attack only requires one compromised application or piece of software to deliver malware across the entire supply chain. Attacks will often target an application’s source code, delivering malicious code into a trusted app or software system.
Cybercriminals often target software or application updates as entry points. Software supply chain attacks are incredibly difficult to trace, with cybercriminals often using stolen certificates to “sign” the code to make it look legitimate.
Hardware Supply Chain Attack
Hardware attacks depend on physical devices, much like the USB keylogger we mentioned earlier. Cybercriminals will target a device that makes its way through the entire supply chain to maximise its reach and damage.
Firmware Supply Chain Attack
Inserting malware into a computer’s booting code is an attack that only takes a second to unfold. Once a computer boots up, the malware is executed, jeopardising the entire system. Firmware attacks are quick, often undetectable if you’re not looking for them and incredibly damaging.
How to Mitigate the Risk of Supply Chain Attacks
Supply chain attacks can be mitigated with a combination of options:
- Use a Privileged Access Management (PAM) solution like KeeperPAM®. KeeperPAM helps prevent supply chain attacks by giving IT administrators complete visibility into vendor access and password practices, as well as the ability to enforce security rules company-wide. PAM can help prevent vendors from accessing anything that isn’t strictly necessary for their work.
- Invest in Security Operation Center (SOC) analysts. These IT professionals will look closely at your business’s cybersecurity infrastructure to identify any problems or missing protection. They’ll also react to threats, analyze the effects of any attacks and work to improve your system.
- Deploy a fake attack with red teams and blue teams. Your red team will create a fake attack in order to mimic a live threat and the blue team will react to it. This can help you identify how threats operate and whether or not your current cybersecurity model is strong enough to stop an active threat.
- Make cybersecurity a regular part of your company’s training regimen. Every employee should understand the importance of cybersecurity and their role in the company’s overall security.
- Have contingency plans/threat models which include every third-party provider. You should always have a contingency plan in place in the event that a third-party provider is compromised or compromises your system. A threat model can help you visualise potential threats that may arise from your vendors/suppliers.
How Companies Detect Supply Chain Attacks
Detecting a supply chain attack quickly is the key to ensuring the damage is limited and reversible. By using modern tools, you can detect all kinds of supply chain attacks from firmware to software and beyond. Here’s what you need:
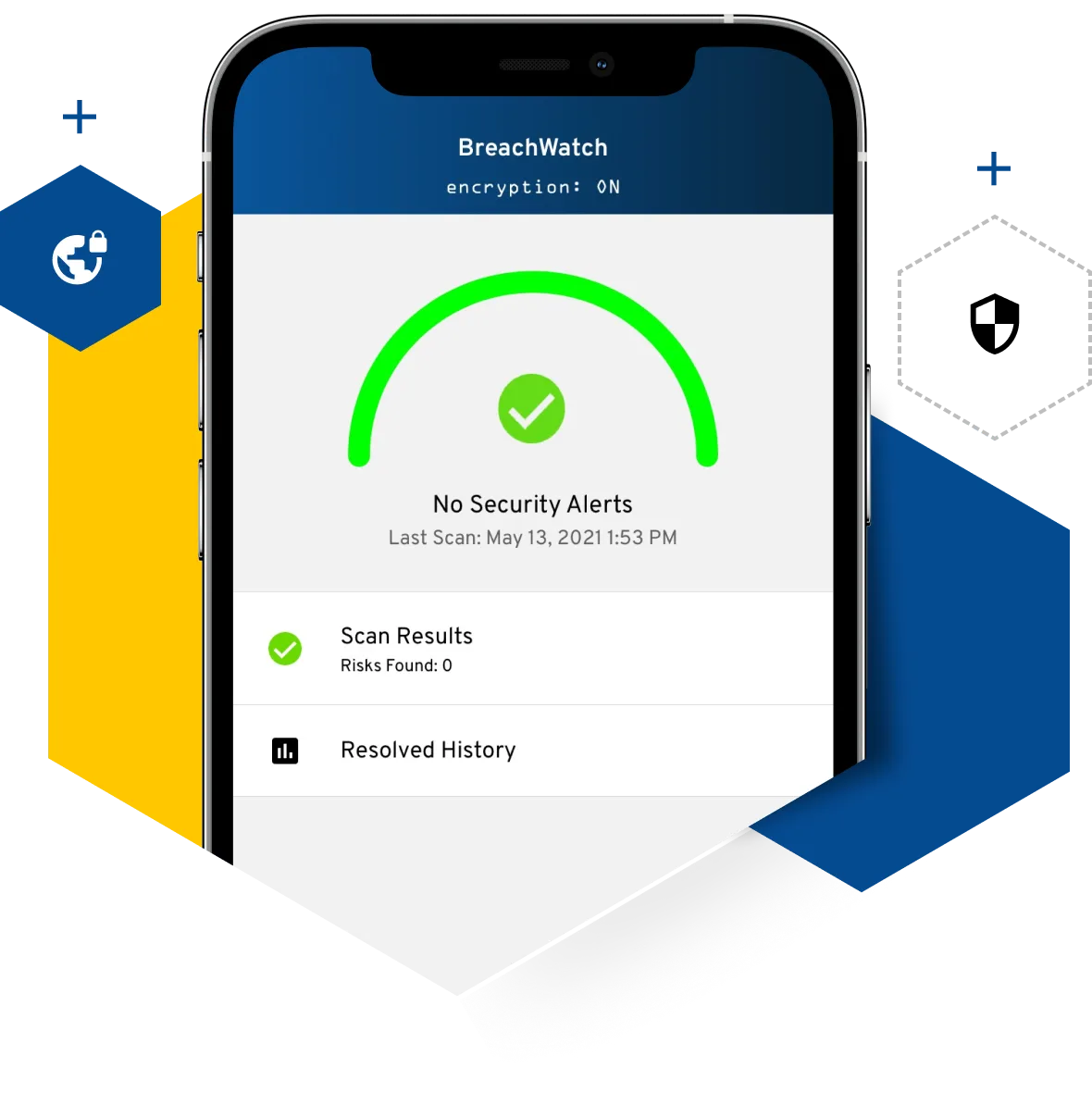
- Keeper BreachWatch®: Use BreachWatch to see if your business (or personal) data has been compromised in an attack. Compromised data is always more vulnerable and can provide an easy entry point for malware.
- Network Detection And Response (NDR) tools: Using NDR tools, you can monitor all of your company’s web traffic for malicious activity. This is especially important if you provide a “guest” WiFi network for vendors entering the building or working with the business.