Imagine a customer service representative at your organization uploads sensitive customer data into an AI tool to draft emails more quickly. When an employee uses an
The main difference between smishing and vishing is that smishing is a phishing attack that uses SMS text message as the contact method and vishing uses voice calls as the contact method.
Research conducted by the FBI’s Internet Crime Complaint Center (IC3) found that phishing, including vishing and smishing, is the most prevalent cyber threat in the U.S. The report found that in 2022, 300,497 people reported falling victim to phishing, resulting in reported losses totaling up to $52,089,159. Although the number of phishing victims was down compared to 2021, the total losses increased.
Continue reading to learn more about smishing and vishing and how to keep yourself safe from these types of phishing attacks.
The Key Difference Between Smishing and Vishing
Smishing and vishing are both types of phishing attacks where the threat actor attempts to convince their targeted victim into revealing sensitive information through urgent language. The key difference between smishing and vishing is the contact method the threat actor uses.
When conducting a smishing attack, the threat actor’s contact method is SMS text message or other messaging apps like Messenger or WhatsApp. When conducting a vishing attack, the threat actor’s contact method is a voice call, such as a phone call, robocall or voicemail.
What is Phishing?
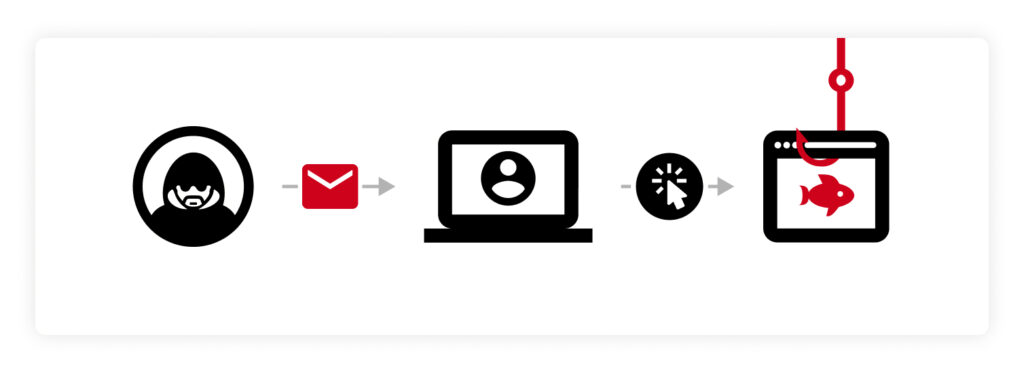
Phishing is a type of social engineering attack that aims to persuade the targeted victim into revealing sensitive information. To convince the victim, the threat actor leverages pretexting techniques to convince the victim they’re someone they’re not, such as a company they have an account with, or a friend, family member or coworker.
Phishing often occurs through emails that contain urgent language such as “take action now or your account will be suspended” so the victim is prompted to act quickly without second-guessing themselves. Phishing scams also contain malicious links or attachments. When clicked, victims are redirected to a spoofed site, or their device is infected with malware. Malware is a type of malicious software that gets unknowingly installed onto a user’s device. When successfully installed, some types of malware are able to track every keystroke the victim makes (keylogger) or spy on them to see all of their sensitive data (spyware).
Example of phishing
How to protect yourself from phishing
You can protect yourself from phishing attacks by taking the following steps:
- Don’t click on unsolicited links or attachments: Clicking on links and attachments you’re not sure about can lead to your device being infected with malware, placing all of your sensitive data at risk of being stolen. Before clicking on unsolicited links, check to see if the link is safe by hovering your mouse over it or using a URL checker.
- Use a password manager: A password manager is a tool that aids you in generating, securely storing and managing your passwords and other sensitive data. Not only will a password manager help you secure your email account from cyber threats, but it also provides a built-in warning about phishing sites. If a site you’re redirected to isn’t showing your saved login information, that’s a telling sign you’re on a phony phishing site and not the legitimate one.
- Enable Multi-Factor Authentication (MFA): MFA is an extra layer of security you can add to your accounts that is strongly encouraged by security professionals. MFA would require the threat actor to verify who they are through an additional method besides a password before they can successfully log in to your account – protecting you in the event that you fall victim to a phishing scam.
- Download antivirus software: Antivirus software is a type of software that can detect, isolate and delete malware and other viruses from your device. Some antivirus software can also scan your emails for malware, which helps you stay protected against email phishing attacks.
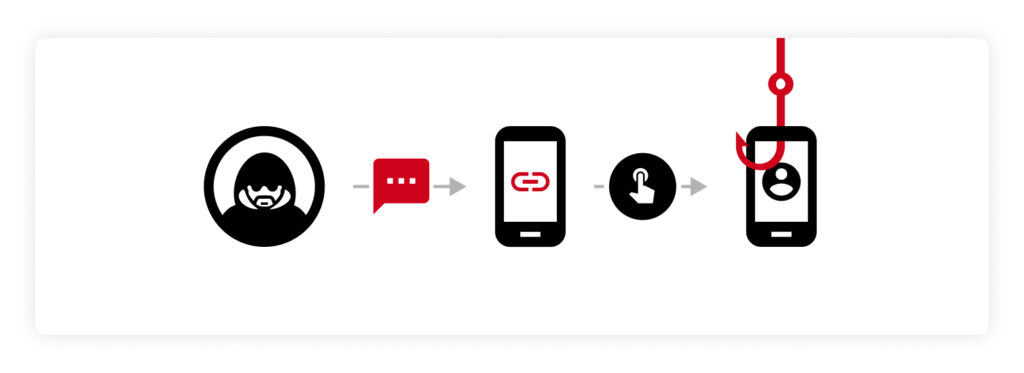
What is Smishing?
Smishing, also known as SMS phishing, is a type of phishing attack that occurs through text message. With smishing, the message the victim receives will contain the same urgent language as phishing emails, so they’re pushed to take action immediately. This type of phishing attack typically uses malicious links so the victim is redirected to a spoofed site that looks like a site they have an account with. If the victim believes the site is legitimate and log in like they normally would, the threat actor will have the victim’s credentials, which they can use to compromise their actual account.
Example of smishing
How to protect yourself from smishing
Keeping yourself protected from smishing is similar to keeping yourself protected from other types of phishing attacks. However, there are a few additional precautions you can take to protect yourself from smishing.
- Don’t respond to requests for personal information: Smishing and other phishing attacks don’t always send malicious links and attachments to scam you. Another common thing you should be on the lookout for is a request for your personal information. A threat actor pretending to be from a company you have an account with may ask you to confirm a few details. If you respond to this request, your accounts are at risk of becoming compromised and your identity is at risk of being stolen.
- Go to the company’s website yourself: If you receive a text message claiming to be your bank or another company you have an account with, go to their legitimate website yourself. This prevents you from clicking on suspicious links and ensures you’re using the actual company’s website, rather than a spoofed one. If you wish to contact the company to ask them about the text message you were sent, it’s best to call the phone number listed on the legitimate company website.
- Block the number: If you’ve determined that the text message you received was a phishing attempt, it’s best to block the number. Doing this will prevent that number from attempting to send you a phishing message again.
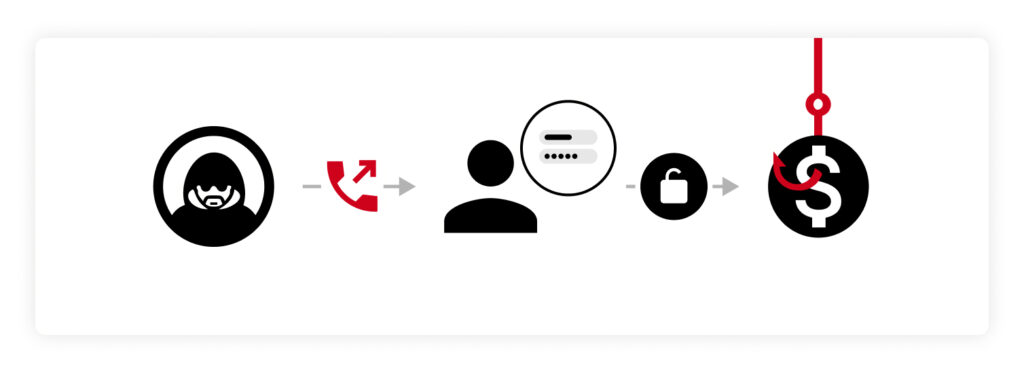
What is Vishing?
Vishing is another type of phishing attack, but it occurs through a voice call rather than email or text. Many people tend to fall for this type of phishing attack because hearing a voice on the other end makes the threat actor sound more convincing. Through this type of phishing attack, the main objective of the threat actor is to have the victim disclose sensitive information such as their credit card number, social security number and so on. The information the threat actor is able to collect can help them carry out targeted cyber attacks, steal money or steal the victim’s identity.
Example of vishing
How to protect yourself from vishing
To protect yourself from vishing, you should follow the steps mentioned in the phishing and smishing sections above. You should also take the following additional steps to protect yourself from vishing attacks:
- Don’t answer unknown callers: One of the best ways to protect yourself from vishing attacks is by not answering phone calls from unknown callers. Only answer calls from people you have saved in your contact list, if possible.
- Get a call blocker: A call-blocking service prevents scammers from being able to call you. Some phone service providers, like AT&T and T-Mobile, offer call-blocking services that you can add to your phone plan. While call-blocking services won’t prevent scam calls altogether, they will prevent the majority of them, which helps protect you from vishing attacks.
- Be wary of AI impersonation: Vishing attacks have gotten more sophisticated and realistic lately because of the rise of Artificial Intelligence (AI). AI can imitate real voices based on audio clips and threat actors can use this technique to impersonate someone the targeted victim knows. For example, a threat actor can use vishing and AI to pretend to be the victim’s family member and say they forgot the login to a sensitive account. Falling for this scam can place that account and other accounts at risk of being compromised.
Keep Safe From Phishing, Smishing and Vishing
Phishing, smishing and vishing continue to be one of the most prevalent threats and are getting more sophisticated each year. Knowing what they are and how to keep safe from them can make all the difference in keeping yourself and your data protected.
While it’s crucial you learn how to spot phishing attacks, it’s likely you may fall for a phishing scam by accident. If this happens, you’ll want to ensure your accounts are already protected with strong and unique passwords to minimize the impact of the attack. A password manager is a huge help in creating strong passwords for all of your accounts and remembering them for you. An added benefit to having a password manager is it can detect spoofed sites, since it won’t autofill on sites it doesn’t recognize.
Get started with a free 30-day trial of Keeper Password Manager to begin securing your accounts from common phishing threats.