Protect Your Professional Services Firm from Cyber Threats
Keeper secures your passwords, credentials and secrets with zero-trust and zero-knowledge security.
Professional Services Firms are a Major Target for Cyber Attacks
most common target for ransomware attacks1
of law firms have experienced a security breach2
of breaches start with weak or stolen passwords3
In the normal course of business, law firms, accountants and other business consultants handle and store highly confidential personal and business information belonging to clients. This information includes digital intellectual property, patent applications, financial records, tax filings, mergers and acquisitions information and details of lawsuits.
As a result, professional services firms are vulnerable to highly-targeted cyber attacks. If client data is compromised, the firm’s obligation to safeguard this information is thrown into question, and its reputation can suffer significant damage.
Yet many professional services firms are not adequately securing their employee passwords or their client data, even as they implement new digital channels, automation and remote work technologies that expand their potential attack surface.
Top Cyber Threats for Professional Services Firms
While professional services firms are vulnerable to every type of cyber threat, there are 3 that occur most often.
Phishing
Phishing is a sophisticated social engineering attack meant to entice victims into voluntarily revealing sensitive information.
The challenge with phishing is that it can be difficult to spot as methods become more sophisticated.
Ransomware
Ransomware attacks lock users out of their systems until a ransom is paid. This ransom payment is often requested in cryptocurrency to maintain anonymity.
Ransomware is now a multi-billion dollar industry with an attack occurring every 11 seconds.4
Credential Stuffing
A credential stuffing attack is when a cybercriminal uses a set of credentials to attempt to gain access to several accounts at once.
Credential stuffing is so effective because nearly two-thirds of internet users reuse their passwords.
Keeper helps prevent these cyber threats and many more. Schedule a demo to learn how.
How Keeper Helps You Maintain Compliance
Professional services firms must comply with a number of regulatory and industry compliance standards regarding client privacy protections and systemic cyber risk mitigation.
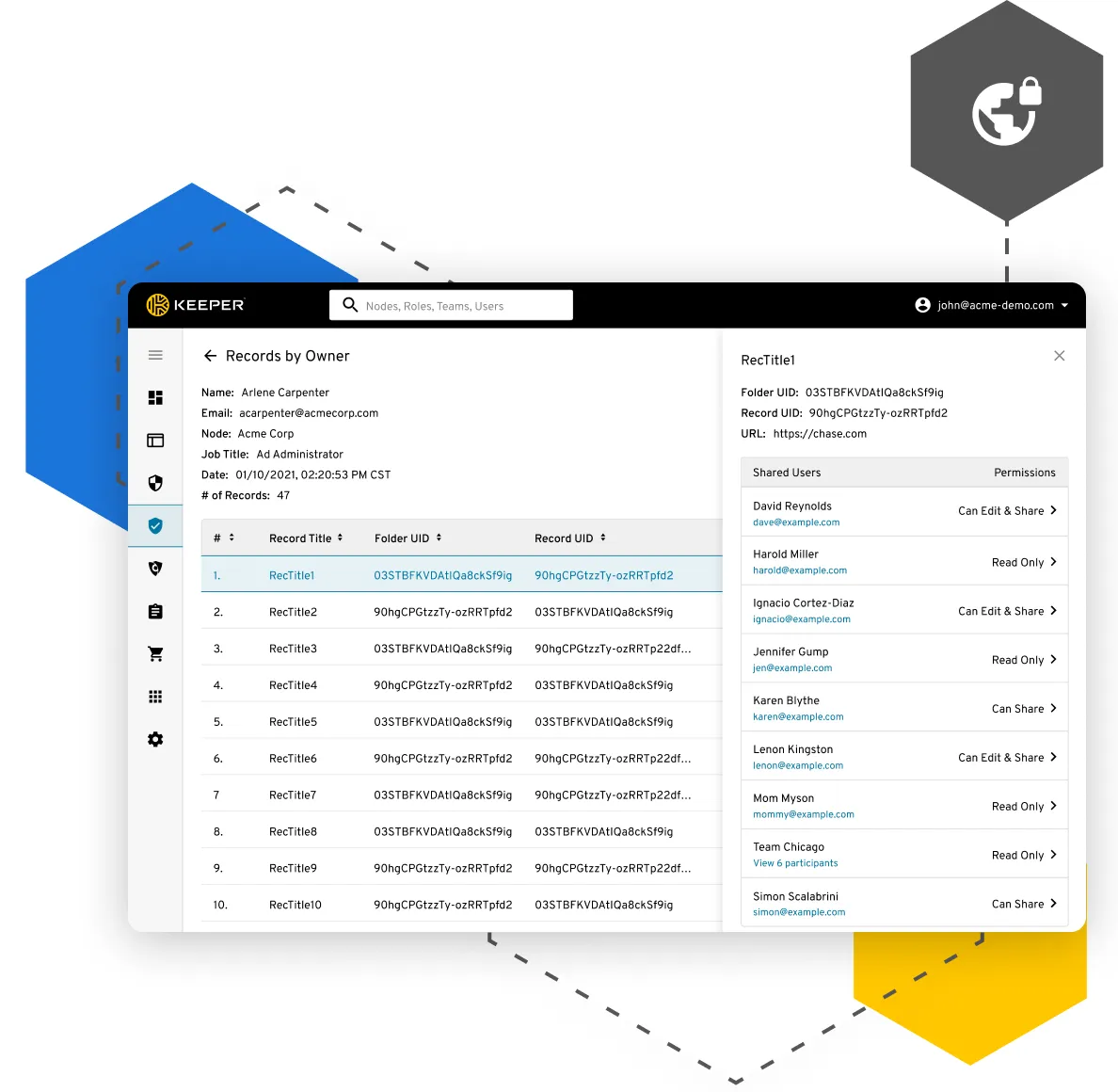
Keeper simplifies compliance monitoring and reporting by giving IT administrators full visibility and control over employee password usage and role-based systems access throughout their data environments, with customizable audit logs and event reporting.
Keeper Third-Party Attestations and Certifications

Protect Your Firm with These Advanced Capabilities
Even if your password security is solid, your firm could be compromised through one of your vendors. Keeper allows you to protect your firm from both internal and external cyber threats.
Some of the world-class features that protect your firm are:
Secrets Management
Remove hard-coded credentials from your source code, automate management of credentials, API keys, database passwords and other secrets - integrates with your CI/CD pipelines and DevOps environment. Learn More
Secure File Storage
Tap into Keeper’s zero-knowledge encryption to put secure file storage, retrieval and decryption privileges only in the hands of approved users. Learn More
Encrypted Messaging
Secure messaging across employee devices with KeeperChat® the world’s most secure messaging solution, to protect communications with end-to-end encryption. Learn More
Dark Web Monitoring
Continuously scan for and receive alerts on compromised passwords to take immediate action against account takeover attacks with BreachWatch®. Learn More
Robust Compliance and Reporting
Supports audits for Sarbanes Oxley (SOX) and other regulations that require access-control monitoring and event auditing. Learn More
Managed End-User Deployment
Count on responsive customer support, detailed deployment and training from our dedicated support specialists. Learn More
Ready to get started? Learn more about our two Keeper plans below!
Keeper Business
(AAA billed annually)
*zzgl MwSt
*Includes GST
- Encrypted vault for every user
- Includes Family Plan for every user
- Folders and subfolders
- Shared team folders
- Access from unlimited devices
- Policy engine and enforcements
- Security Audit
- Activity reporting
- Team management
- Basic Two-Factor Authentication (SMS, TOTP, smartwatch and FIDO WebAuthn)
Keeper Enterprise
Contact sales for Keeper Enterprise pricing
- Everything in Keeper Business, plus:
- Single Sign-On (SAML 2.0) authentication
- Automated Team Management
- Advanced Two-Factor Authentication (DUO & RSA)
- Active Directory and LDAP sync
- SCIM and Microsoft Entra ID (Azure AD) provisioning
- Email auto-provisioning
- Command line provisioning
- Developer APIs for password rotation and backend integration