Imagine a customer service representative at your organization uploads sensitive customer data into an AI tool to draft emails more quickly. When an employee uses an
The main difference between the deep web and the dark web is that the deep web is bigger and used every day by most people without even realizing it, whereas the dark web can only be accessed with the Tor browser and is riskier to access than the deep web.
Continue reading to learn more about the differences between the deep and dark web, and how you can keep your information protected from both.
What is the deep web?
The deep web, also known as the hidden web, is the part of the internet where almost all online activity happens. The deep web consists of sites and databases that are not fully accessible to standard search engines such as Google, Bing and Yahoo. This could be because the pages are not indexed, meaning they can’t be found by searching for them on search engines, they are paywalled websites or private databases. To access deep web content, you’ll need the direct link or sign-in credentials that grant you access to it.
What is the deep web used for?
- Paid Subscriptions: The deep web is used to access all types of paid subscriptions such as streaming services like Netflix and Hulu.
- Accessing Accounts: One of the main uses of the deep web is to log in to accounts such as social media or bank accounts.
- Online Payments: Whenever you pay for something online, you enter your payment information through the deep web.
What is the dark web?
The dark web is a part of the internet that provides anonymous and secure communication channels that can only be accessed with a special browser called Tor. Average users of the internet will not stumble upon the dark web. Going on the dark web has to be intentional since it requires a user to have specific tools to access it, such as the Tor browser and a Virtual Private Network (VPN).
What is the dark web used for?
- Anonymity: Many people use the dark web because they want to remain anonymous. For example, citizens who are a part of oppressive regimes use the dark web to speak freely.
- Selling Personal Data: Cybercriminals often use the dark web to sell stolen information leaked in data breaches. For example, they may sell account login information, credit card numbers and Social Security numbers, to name a few.
- Illegal Purchasing: People use the dark web as a way to purchase things that they can’t get anywhere else because they’re illegal. This includes drugs, weapons and stolen data.
The key differences between the deep web and dark web
Here are some of the key differences between the deep and dark web.
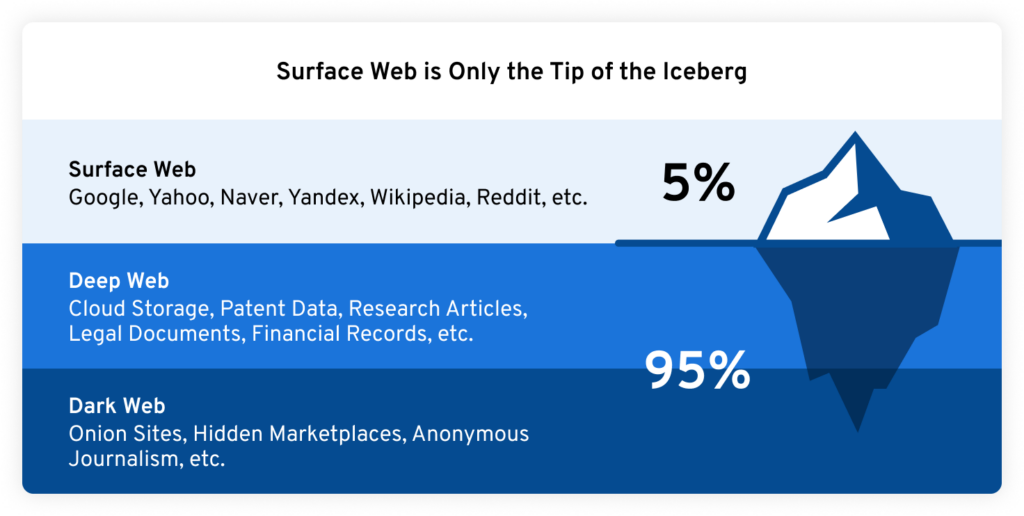
1. The deep web is bigger than the dark web
The deep web is the largest part of the internet. According to Dataprot, a rough estimate is that the surface web makes up only 5% of the internet and the rest is made up of the deep web. The surface web is anything on the internet that you’re able to search for on standard search engines like Google.
According to SpiceWorks, the deep web hosts around 7,500 terabytes of data, whereas the surface web hosts 19 terabytes. It’s also estimated that there are 550 billion individual documents that are hosted on the deep web and only one billion are hosted on the surface web. The dark web is considered to be a smaller subset of the deep web. According to Britannica, the dark web makes up only 0.01% of the deep web.
2. Most people access the deep web everyday, but not the dark web
As mentioned above, some common use cases for the deep web include accessing paid subscriptions and online accounts. These are things that most people access everyday. However, since the dark web has to be accessed intentionally using the Tor browser and a VPN, most people won’t access the dark web in their day-to-day lives.
3. Unlike the deep web, the dark web is often used for criminal activity
Since the dark web provides its users with anonymity, cybercriminals use this to their advantage to carry out various criminal activities such as buying and selling illegal weapons, drugs, and personal data that they gathered from public data breaches. This kind of criminal activity does not take place on the deep web because it’s illegal.
4. The dark web is riskier to access than the deep web
Both the deep web and dark web come with their risks, however, the dark web presents a greater one. Because the dark web is home to all kinds of illegal activity, clicking on the wrong thing can place your device at risk of becoming infected with malware or other viruses. Malware is a type of malicious software that can spy on you, log your keystrokes and steal your personal information.
How to keep your information safe on the deep web and dark web
Here’s how you can keep your information safe on both the deep and dark web.
Use strong, unique passwords
One of the best ways you can keep yourself and your information protected is by using strong, unique passwords for each of your accounts. Strong passwords are at least 16 characters long and contain uppercase and lowercase letters, numbers and symbols. To make your accounts as secure as they can be, make sure you’re not reusing or using variations of the same password across multiple accounts.
Coming up with strong passwords and memorizing them all is next to impossible to do on your own. We recommend using a password manager to aid you in generating, managing and securely storing all your passwords, passkeys and data. With a password manager, the only password you’ll have to remember is your master password.
Enable MFA on your accounts
Multi-Factor Authentication (MFA) is an extra layer of security you can enable on your accounts. MFA protects you in the event that someone gains access to your login credentials since it requires a one or more methods of authentication before they’re able to successfully log in.
Subscribe to a dark web monitoring service
Dark web monitoring is when a tool is used to scan the dark web for your personal information such as your email address or credentials. This can be done manually with a free service that doesn’t notify you, or it can be done automatically with a tool that detects and notifies you when your credentials are being sold on the dark web. A dark web monitoring tool that constantly scans the dark web for your personal information is the best option for keeping you and your data safe because you’ll receive dark web alerts and can take action immediately if your credentials or information are compromised.
One dark web monitoring tool that works alongside Keeper Password Manager is BreachWatch®. BreachWatch monitors for suspicious activity on the dark web and alerts you as soon as any dark web activity matches the credentials stored in your Keeper Vault. When one of your records shows as “high-risk,” you’ll receive a notification and Keeper will help you change your password to one that is strong and unique.
Maintain good cyber hygiene
Cyber hygiene refers to cybersecurity best practices that everyone who actively uses the internet should be implementing to keep themselves and their data protected from common cyber threats.
Some cybersecurity best practices you should follow include:
- Using a personal firewall
- Using a VPN
- Having antivirus software installed on your computer
- Regularly updating your software, apps and devices
- Regularly backing up your data
- Checking if links are safe before clicking on them
- Being cautious of unsolicited attachments
- Not responding to requests for personal information
Stay up to date with the latest cybersecurity news
To know about the latest cyber threats people fall victim to online, you should keep up with the latest cybersecurity news. This will help you understand what type of attacks to be on the lookout for when you’re browsing online.
Stay safe on the deep web and dark web
Being an active internet user means there’s always a possibility that your information is vulnerable to being stolen, which is why it’s important you take the necessary precautions to keep yourself and your data protected. While we don’t recommend you access the dark web, if you do decide to, make sure you take all the steps above to keep your data safe from cybercriminals. The same steps apply when using the deep web.
Start a free 30-day trial of Keeper Password Manager today to begin securing your accounts from common cyber threats on all parts of the internet.