功能: SIEM 集成
无缝集成 SIEM 系统,实现实时可视与威胁响应。
Keeper 的 SIEM 集成功能由高级报告和警报模块 (ARAM) 提供支持,可实现全域可视、实时告警,并生成符合审计要求的报告。
功能: SIEM 集成
Keeper 的 SIEM 集成功能由高级报告和警报模块 (ARAM) 提供支持,可实现全域可视、实时告警,并生成符合审计要求的报告。
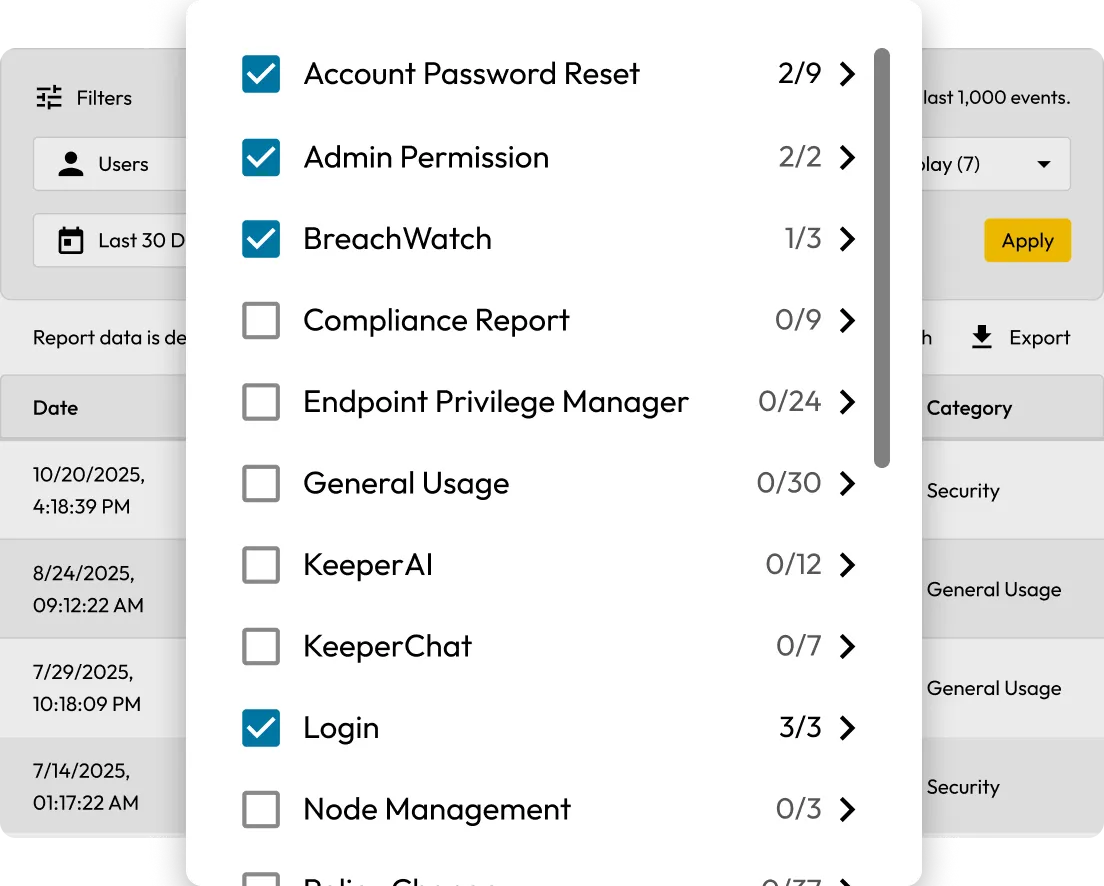
可生成 300+ 种事件类型的自定义报告,涵盖安全事件、管理员操作、特权访问管理 (PAM) 活动等。可按用户、记录 UID、IP 地址、位置及其他属性筛选,精准定位核心信息。
Keeper 可与 ServiceNow、Jira、Salesforce 等平台集成,基于实时事件自动生成工单,简化工作流程,提升安全团队与 IT 团队的协作效率。
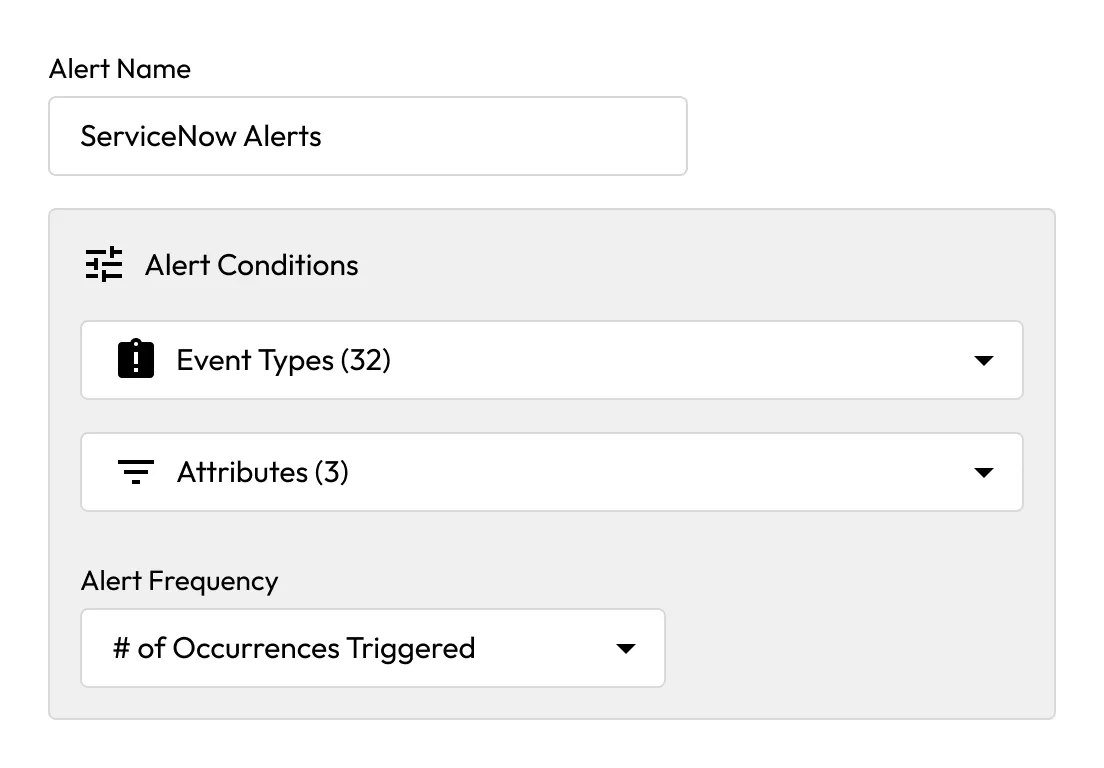
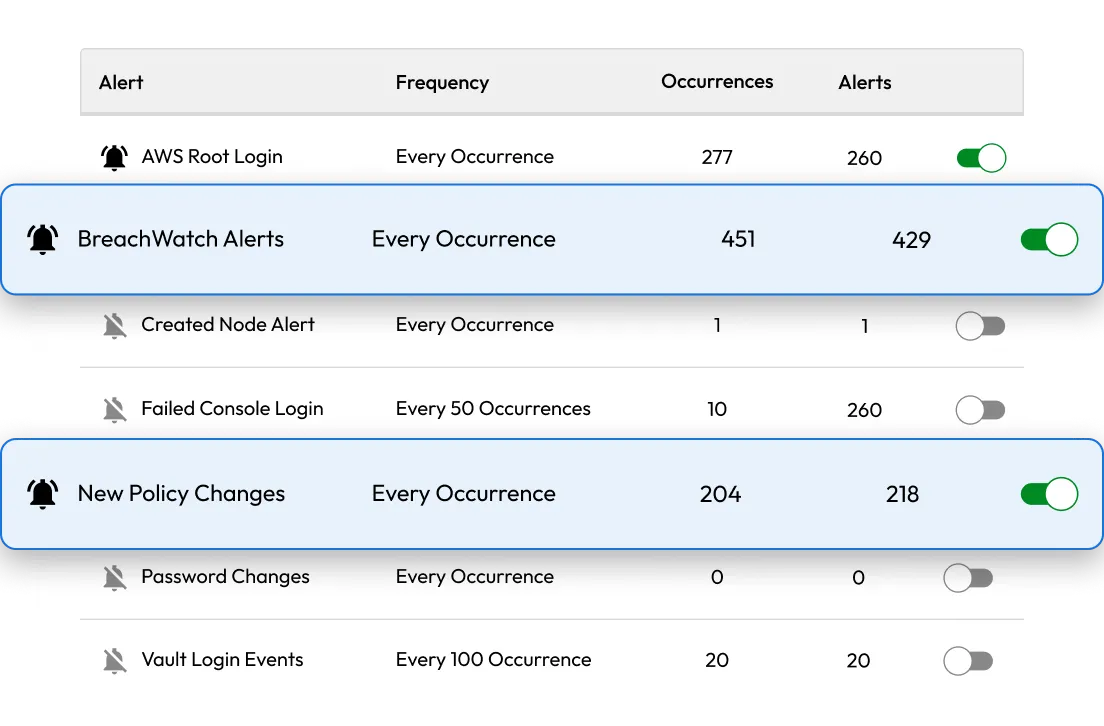
可为任意事件类型设置警报,通过电子邮件、短信或 Webhook 接收通知。常见触发场景包括角色策略变更、2FA 关闭、设备审批、BreachWatch 检测警报。
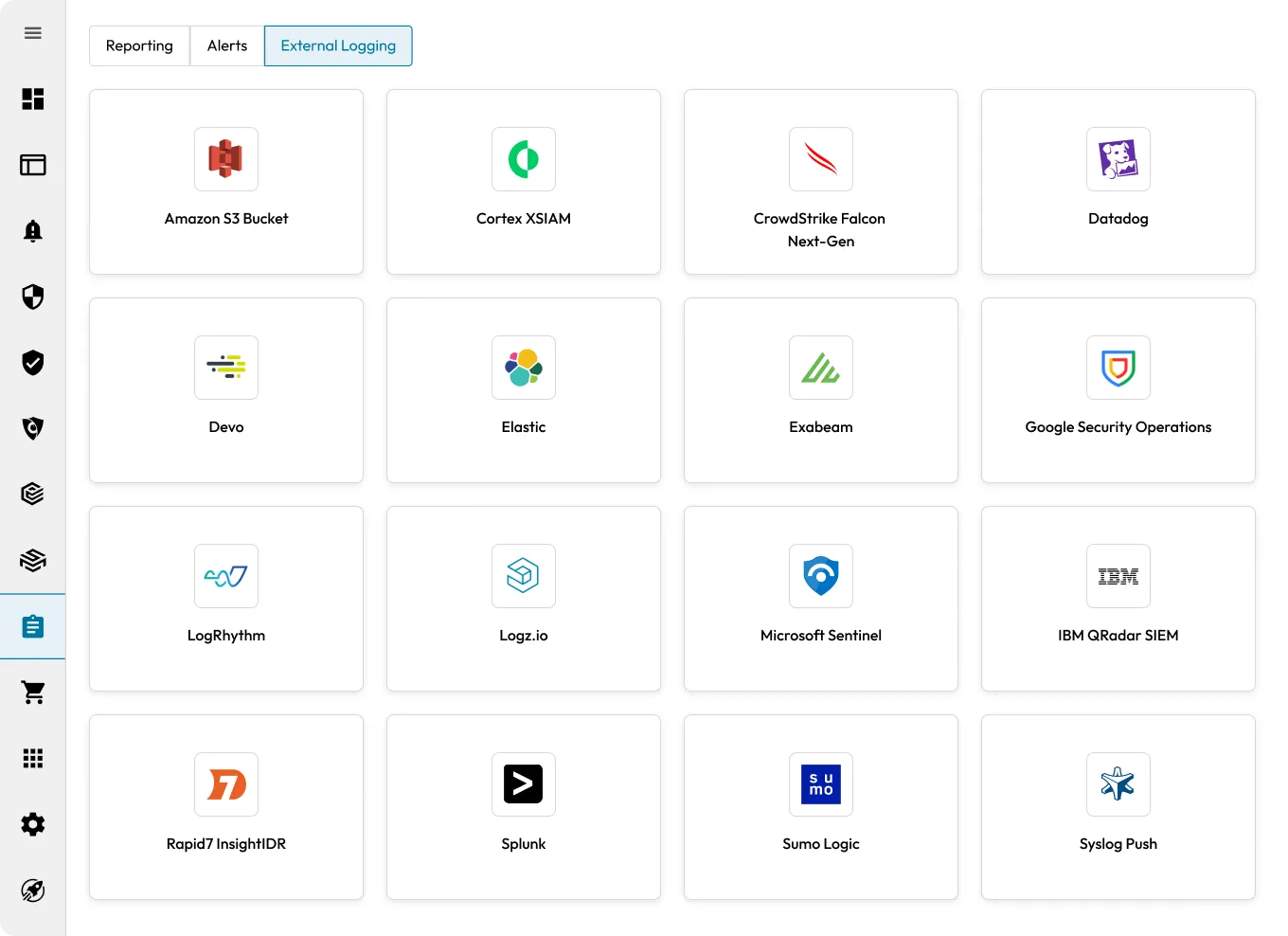
可通过预集成组件、系统日志或 Webhook 连接您的 SIEM 平台。Keeper 支持 Microsoft Sentinel、Splunk、CrowdStrike Falcon Next-Gen SIEM、Datadog、Google Security Operations、Elastic、AWS S3 等多种平台。

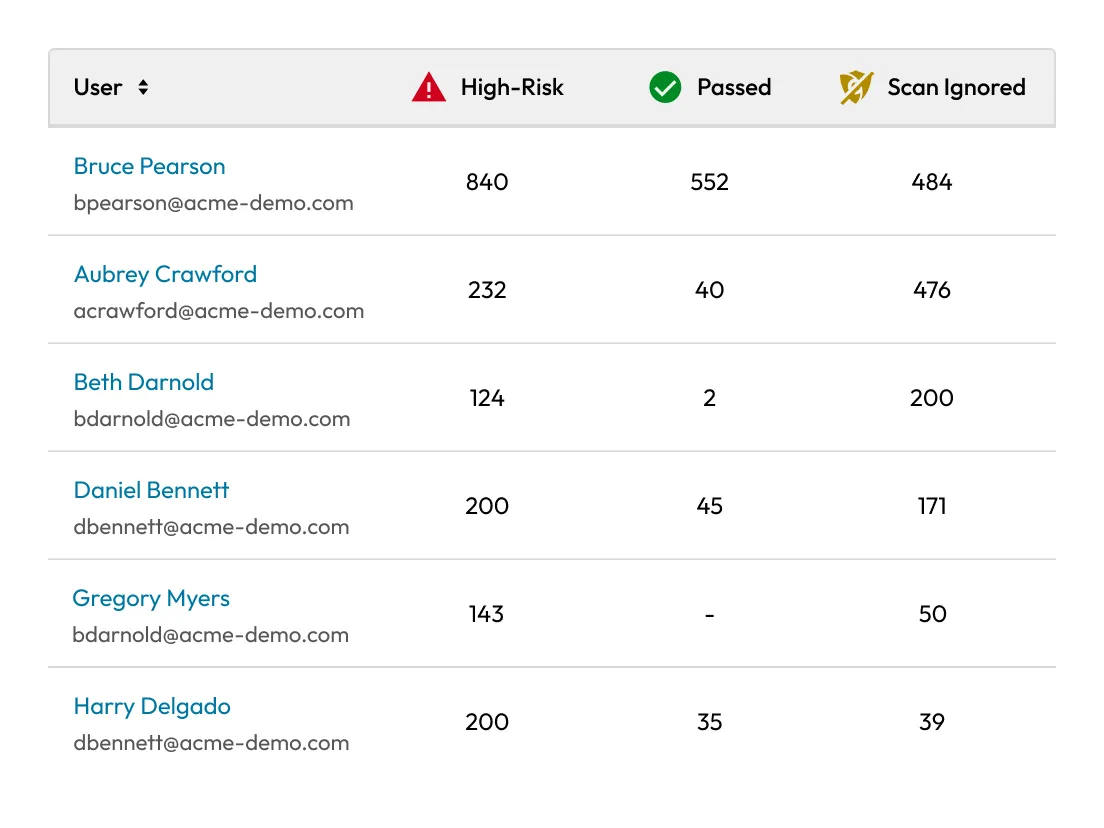
跟踪 BreachWatch® 警报与处理事件,监控组织内的高风险密码。可基于该数据规范凭据使用管理,降低安全风险。
可通过 Keeper Commander 调取、筛选 SIEM 事件数据,生成自定义报告,并与日志传输通道或外部系统集成。


生成详细的操作报告,以满足 SOX、ISO、SOC 2、HIPAA 等合规要求。Keeper 可帮助您在审计过程中便捷地展示管控措施与责任追溯依据。
并非如此,Keeper 的 SIEM 集成功能需额外搭载高级报告和警报模块 (ARAM)。如果您使用的是 KeeperPAM®,则已包含 ARAM 模块。
Keeper 可记录 200 余种事件类型,包括登录、密码修改、记录创建、共享操作、PAM 会话启动、设备审批、保管库转移等。
可以,您可通过 Keeper 的 ARAM 模块配置筛选规则与阈值逻辑。
可以,所有事件仅记录元数据。保管库内容全程加密,Keeper 及您的 SIEM 服务提供商均无法访问。
Keeper 支持所有主流 SIEM 系统,包括 Splunk、IBM QRadar、LogRhythm、Sumo Logic、Azure Sentinel 等。
您必须启用 Cookie 才能使用在线聊天。