Keeper is gemaakt met het oog op ontwikkelaars
Krijg controle over uw Keeper-omgeving met speciaal ontworpen ontwikkeltools, SDK's en native integraties.
Krijg controle over uw Keeper-omgeving met speciaal ontworpen ontwikkeltools, SDK's en native integraties.
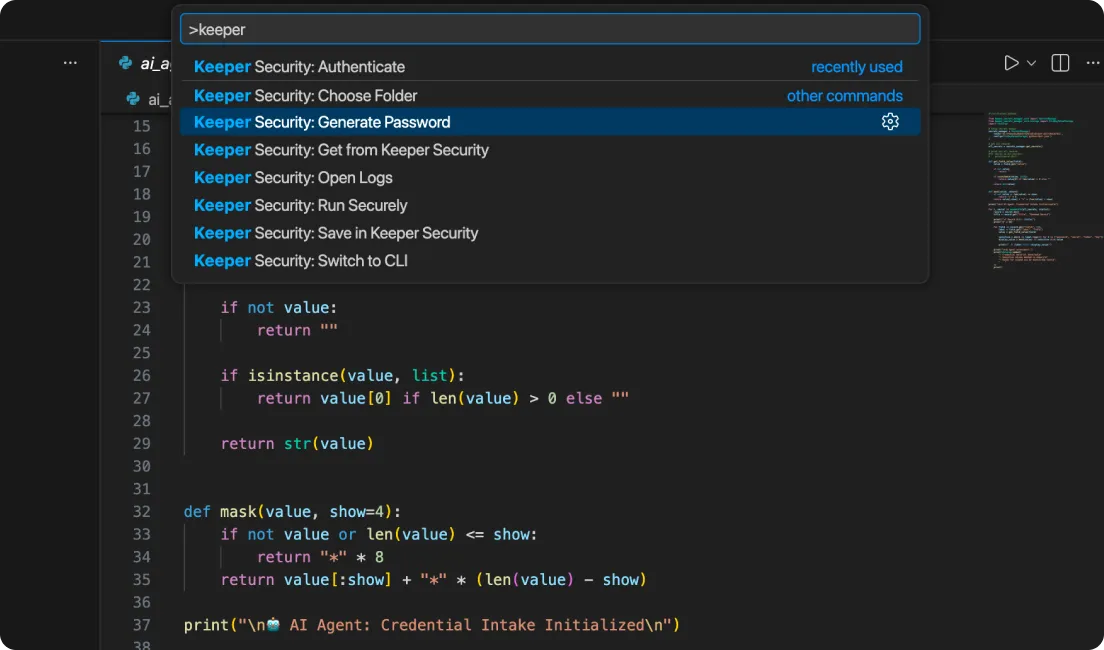
Keeper Secrets Manager for VS Code brings secure vault access directly into the development workflow, allowing developers to save, retrieve and generate secrets without leaving their editor. With support for both Keeper Commander CLI and Secrets Manager, plus secure command execution and built-in secret detection, teams can eliminate hard-coded credentials while maintaining zero-knowledge security.
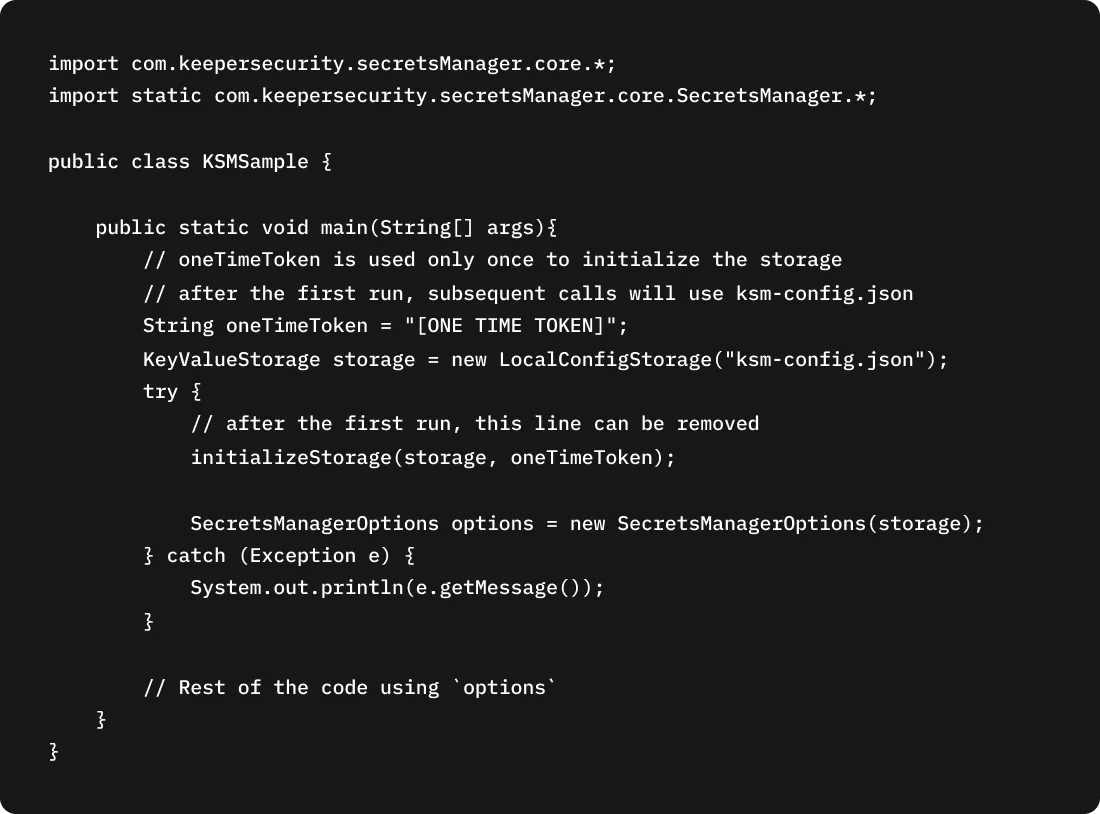
Versnel de ontwikkeling met Keeper Secrets Manager SDK's, ontworpen voor snelle, lichtgewicht en veilig ophalen van geheimen in moderne toepassingsstacks. Integreer geheimen in uw toepassingen met minimale code, terwijl u zero-knowledge versleuteling en hoge prestaties behoudt.
[Ondersteunde SDK's: Java/Kotlin, JavaScript, Python, .NET, Go, Ruby, Rust]
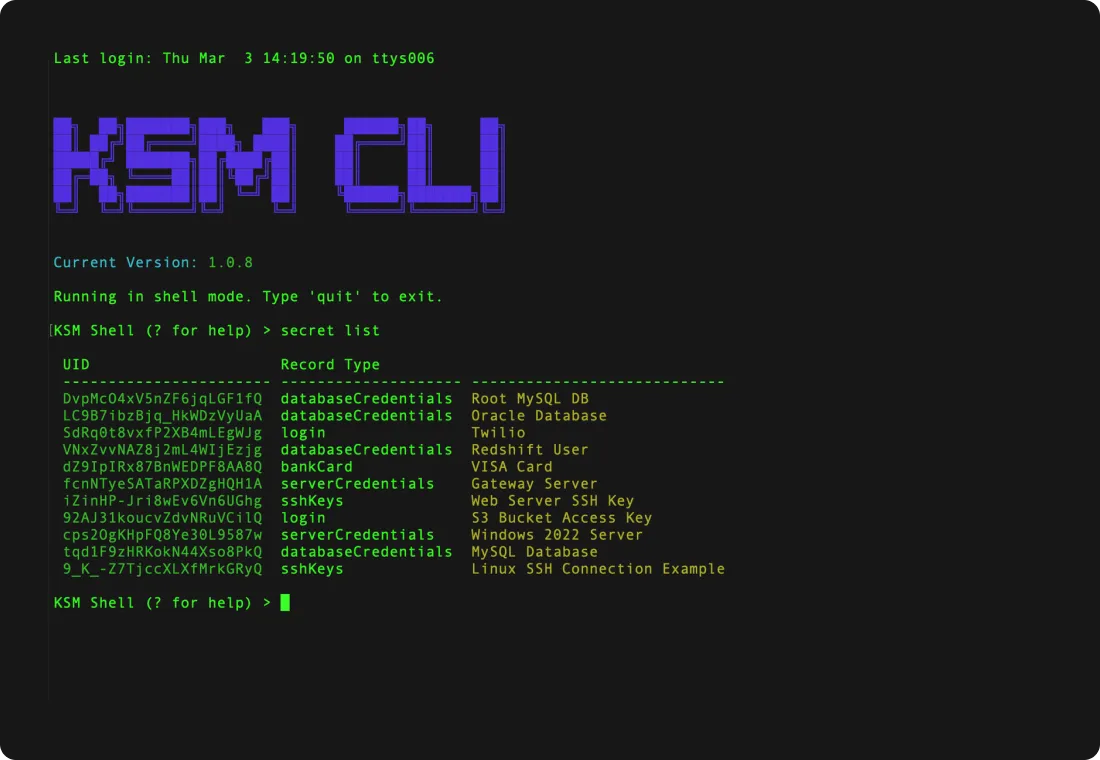
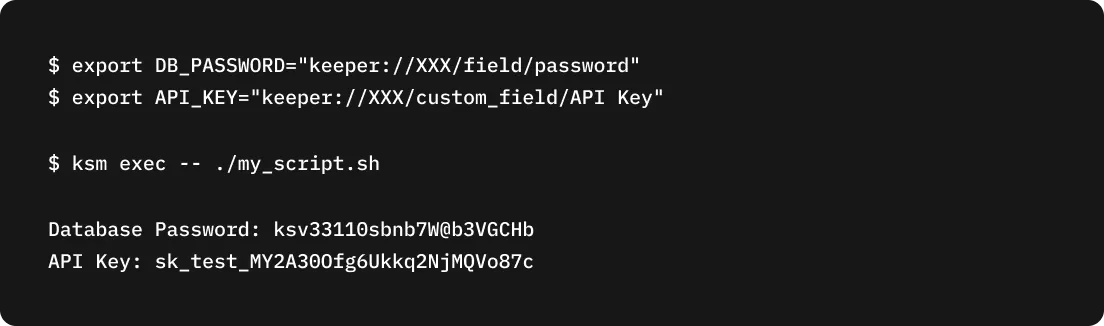
De Keeper Secrets Manager CLI maakt veilige, machinegebaseerde toegang tot geheimen mogelijk, rechtstreeks vanuit terminals, scripts en automatiseringspijplijnen. De mogelijkheden omvatten het ophalen van geheimen, het injecteren van omgevingsvariabelen, het initialiseren van configuraties en ondersteuning voor shelluitvoering.
The Keeper Commander SDKs for .NET and Python provide programmatic access to the Keeper Vault, Enterprise Admin Console and Secrets Manager. They enable secure credential management, enterprise policy control and automation at scale, allowing organizations to embed Keeper’s zero-trust security into custom applications and DevOps workflows.

Keeper Secrets Manager integreert naadloos met populaire CI/CD-platforms, containeromgevingen en orkestratietools, waaronder Kubernetes, waardoor geheimen veilig kunnen worden geïnjecteerd tijdens de uitvoering zonder hardgecodeerde aanmeldingsgegevens of verstoring van workflows.
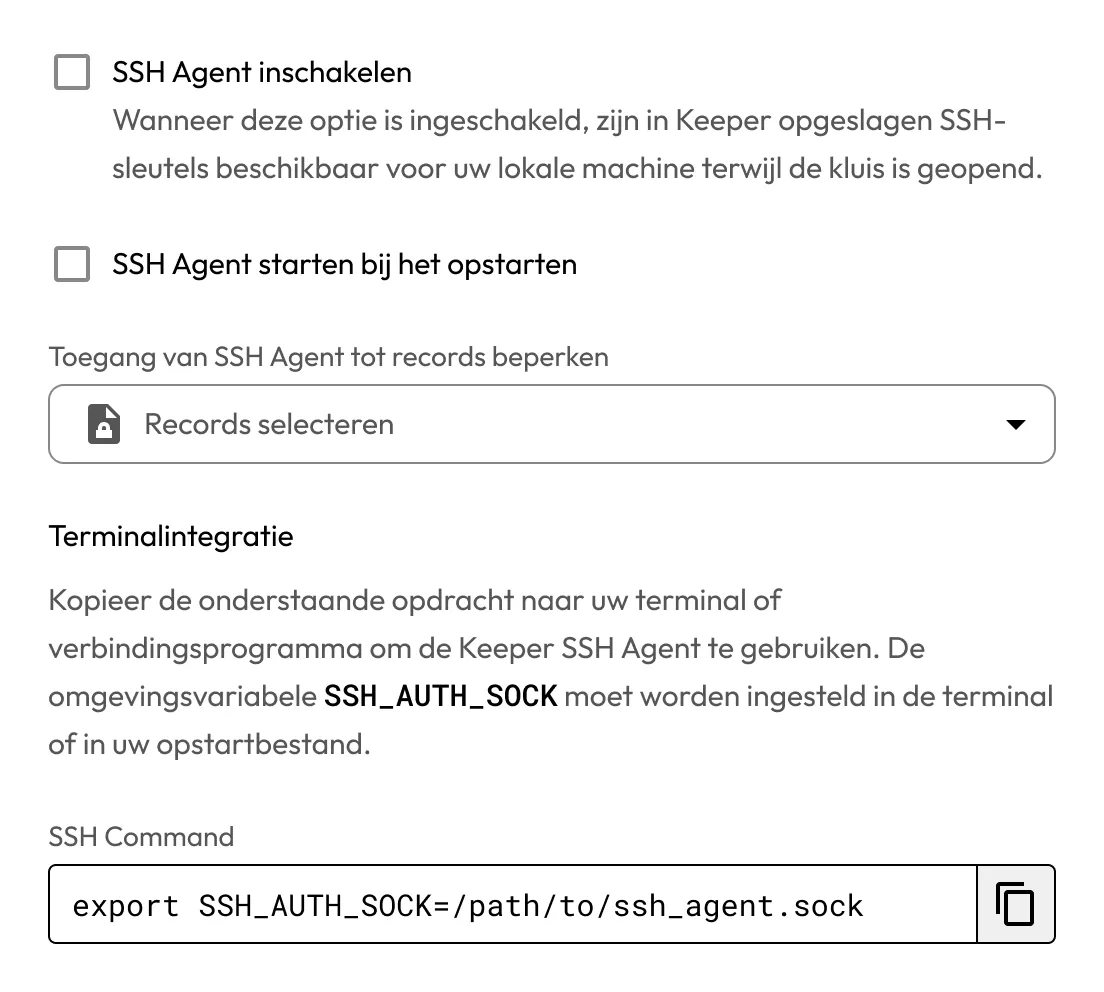
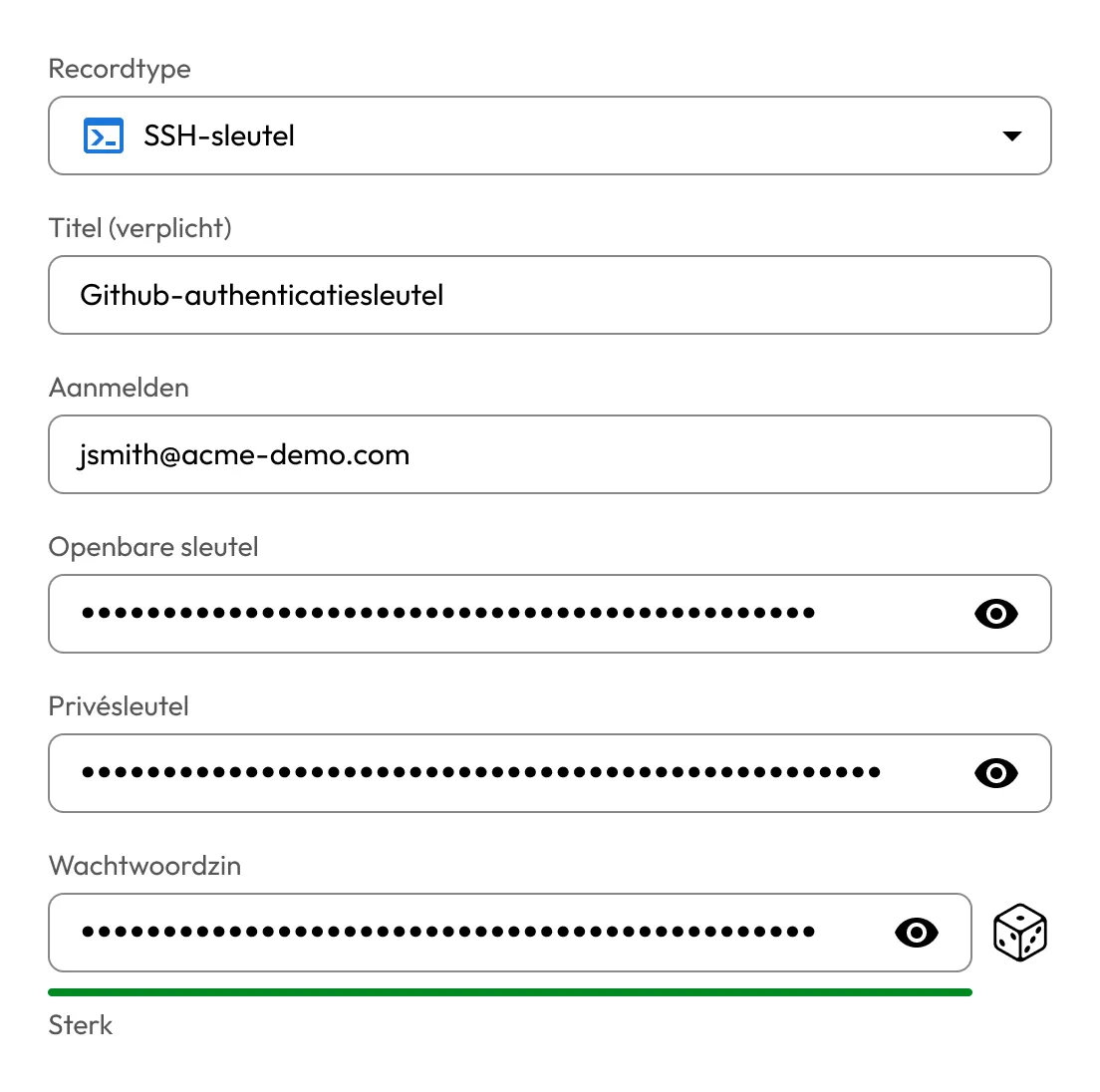
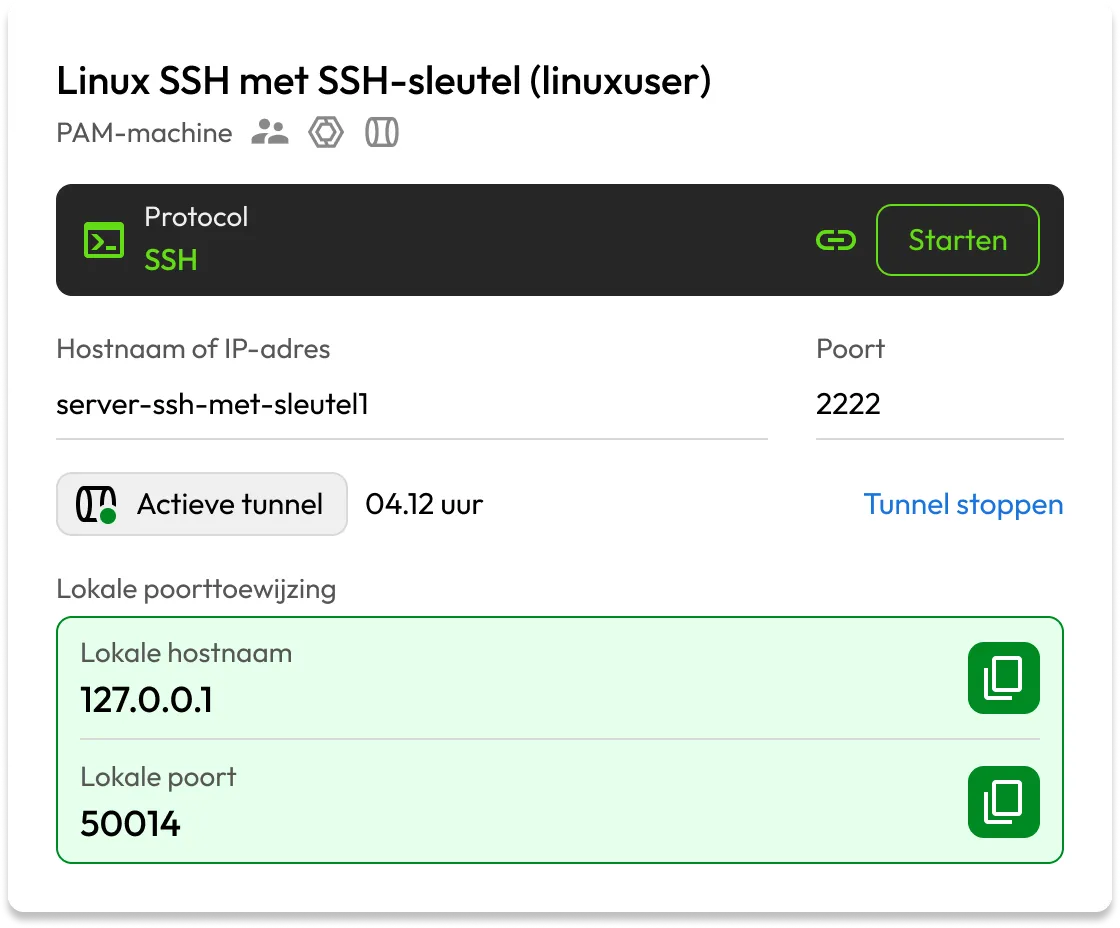
Keeper SSH-sleutelbeheer centraliseert opslag, toegangsbeheer en levenscyclusbeheer van SSH-sleutels. Het omvat geautomatiseerde rotatie, op rollen gebaseerde toegangscontrole (RBAC), auditregistratie en veilige browsergebaseerde toegang. Er worden geen privésleutels blootgesteld. Geen VPN nodig.
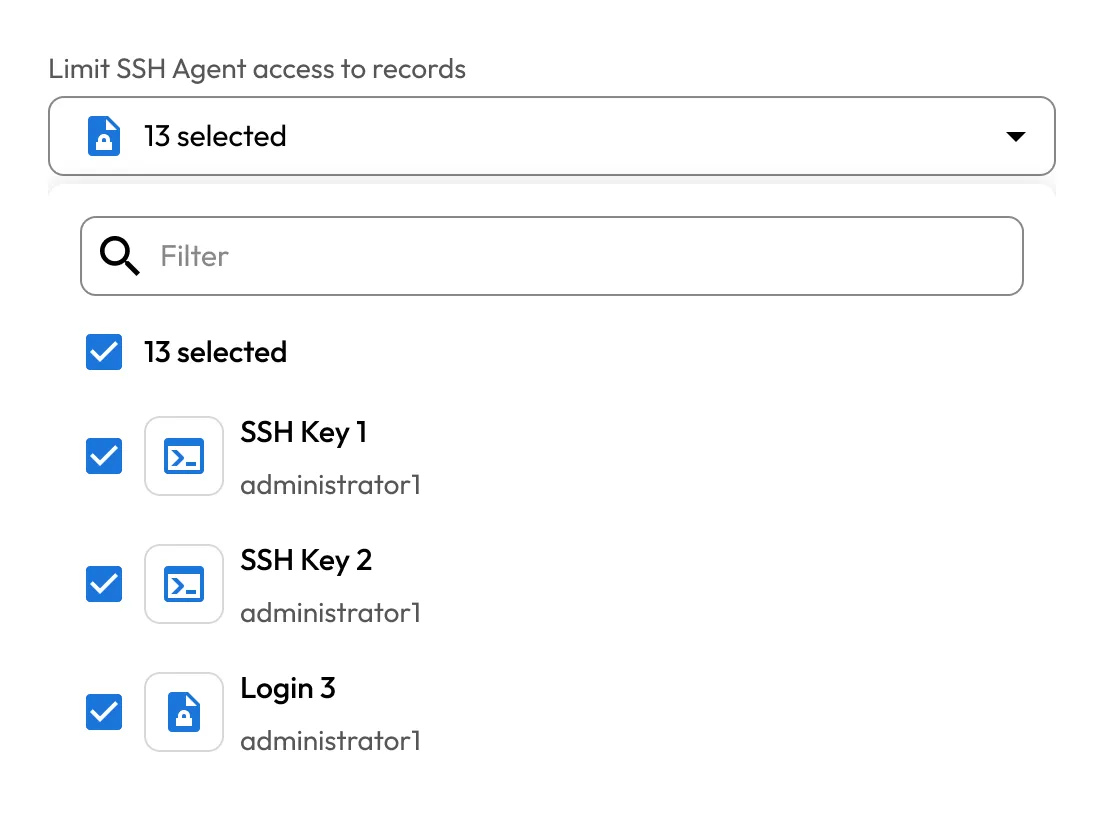
Keepers SSH-agent laadt SSH-sleutels dynamisch uit de versleutelde kluis in sessies die zich uitsluitend in het geheugen bevinden, waardoor permanente lokale opslag van sleutels wordt geëlimineerd en naadloze terminalgebaseerde toegang mogelijk wordt.
De exec-opdracht van Keeper Secrets Manager injecteert geheimen in omgevingsvariabelen tijdens de uitvoering, waardoor elk script, binair bestand of systeemaanroep veilig geheimen kan implementeren zonder wijzigingen in de toepassingscode.
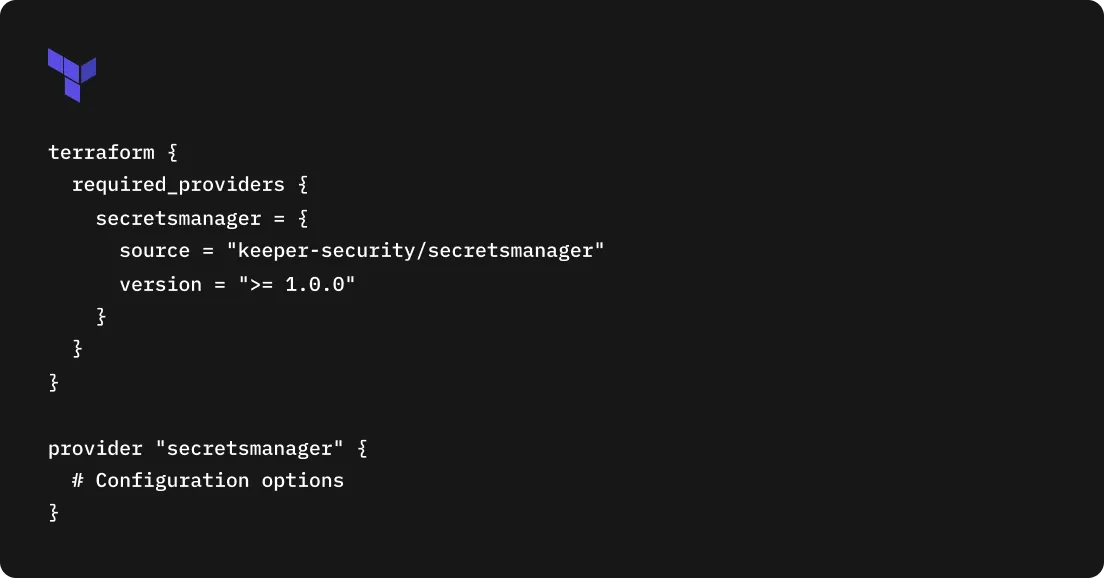
De Keeper Secrets Manager Terraform Provider stelt Terraform-configuraties in staat om veilig te verwijzen naar geheimen die zijn opgeslagen in de Keeper-kluis, waardoor geheimen in leesbare tekst in state-bestanden of bronbeheer worden voorkomen.
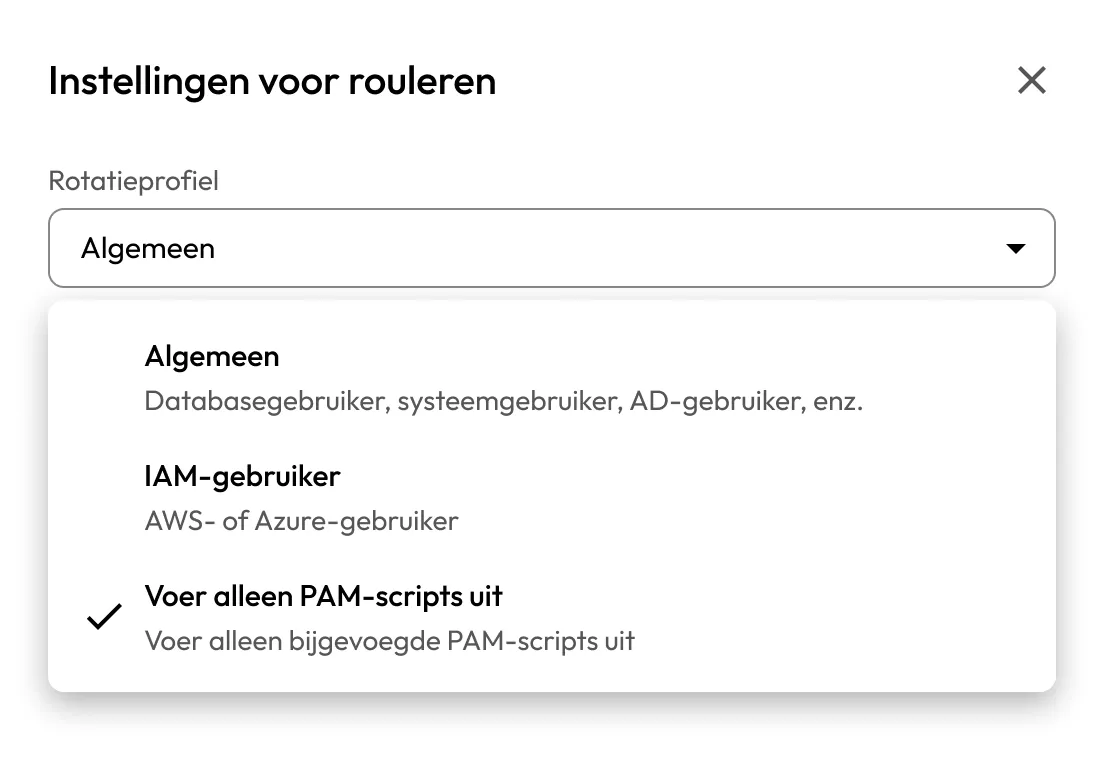
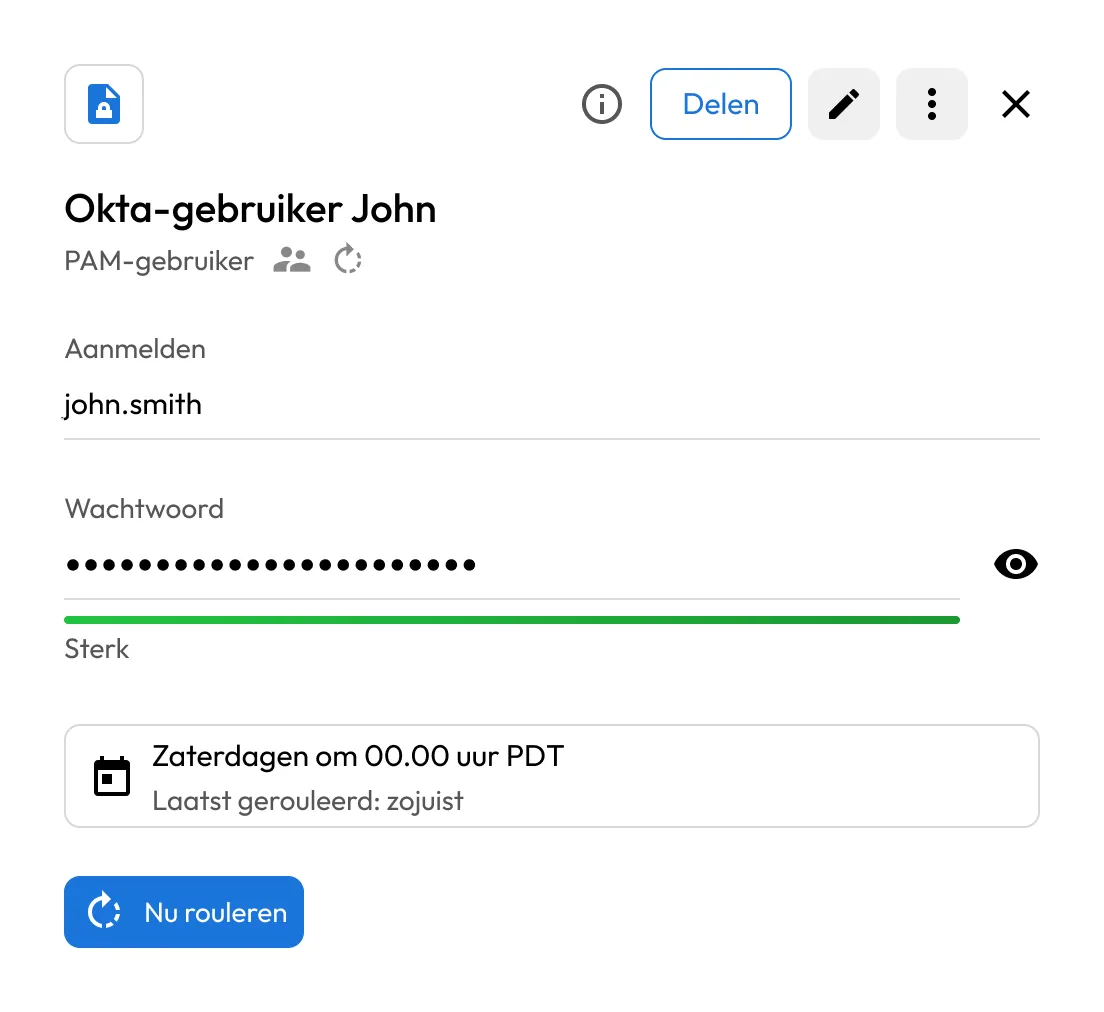
Keeper ondersteunt geautomatiseerde rotatie van aanmeldingsgegevens via configureerbare rotatieworkflows en uitbreidbare PAM-scripts. Organisaties kunnen ingebouwde scripts gebruiken, aangepaste logica ontwikkelen of door de community ondersteunde integraties gebruiken.
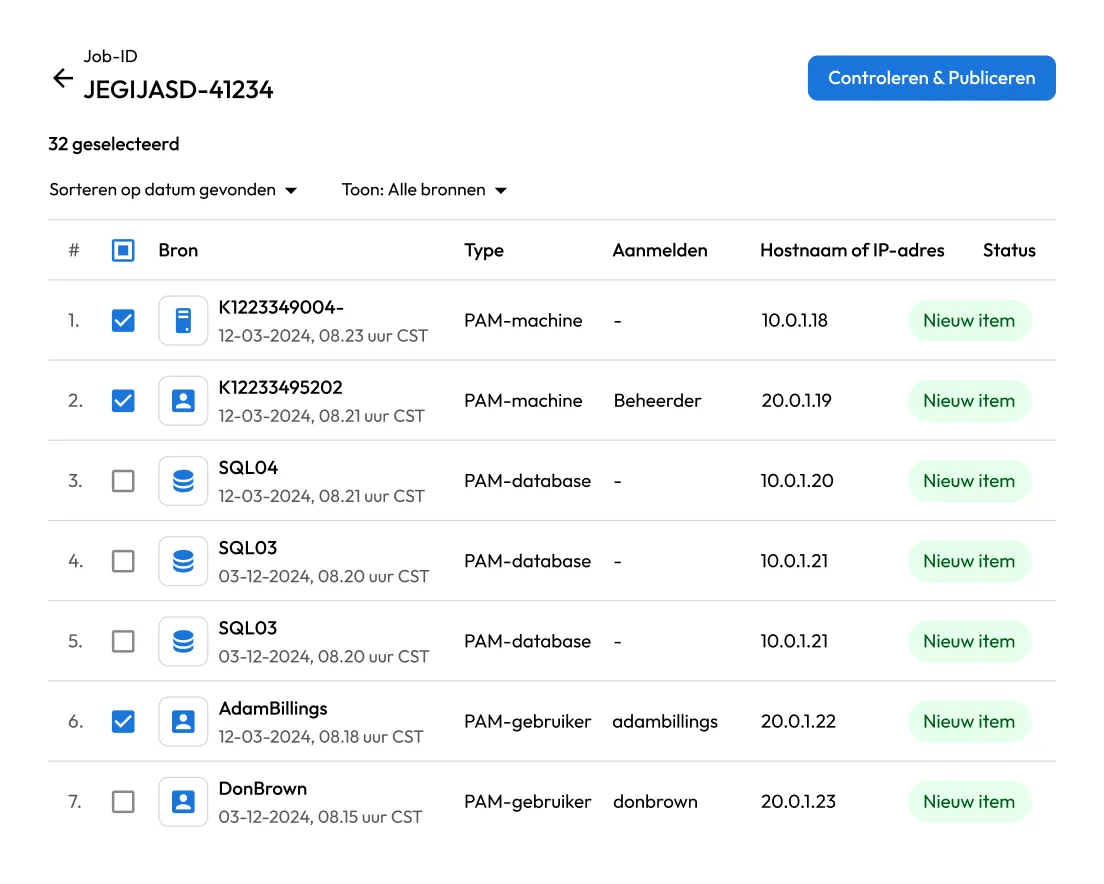
Keeper Discovery identificeert gepriviligeerde accounts, serviceaccounts en afhankelijkheden van aanmeldingsgegevens binnen de infrastructuur, waardoor beveiligings- en DevOps-teams blinde vlekken kunnen elimineren en risico's kunnen verminderen.
Keeper maakt veilige opslag en gebruik van GPG- en SSH-ondertekeningssleutels mogelijk om geverifieerde Git-commits te ondersteunen, waarmee repository's worden beschermd tegen imitatie en ongeautoriseerde codewijzigingen.
Keeper Connections biedt veilige toegang tot servers, databases en webtoepassingen zonder aanmeldingsgegevens, rechtstreeks vanuit de Keeper-kluis. Aanmeldingsgegevens worden tijdens de uitvoering geïnjecteerd en nooit blootgesteld aan eindgebruikers.
Breid Keeper uit met plug-ins die geautomatiseerde rotatie van aanmeldingsgegevens voor SaaS-applicaties en diensten van derden mogelijk maken. Integreer rotatieworkflows in bedrijfseigen systemen, interne tools en niet-ondersteunde platforms om voor continue hygiëne van aanmeldingsgegevens te zorgen zonder handmatige tussenkomst.
Keepers externe browserisolatie voert websessies uit in een externe omgeving om gebruikers te beschermen tegen bedreigingen op het web. Aanmeldingsgegevens kunnen veilig worden geïnjecteerd zonder dat ze naar endpointapparaten worden verzonden of daarop worden opgeslagen.
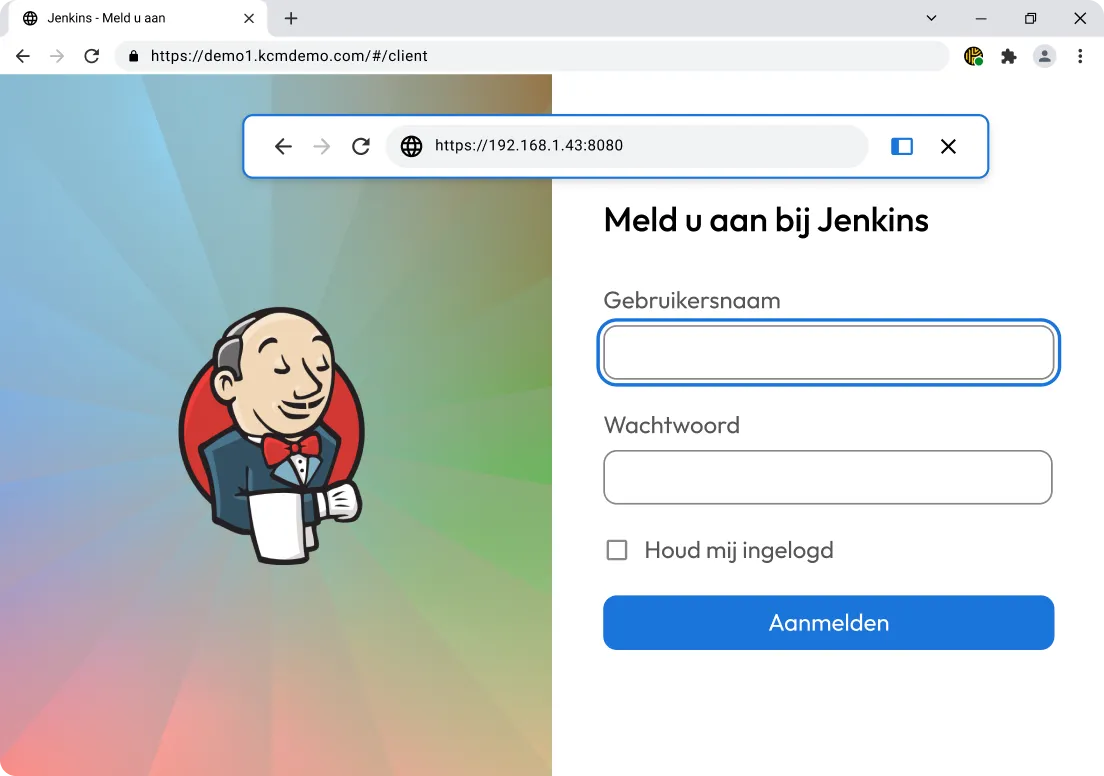
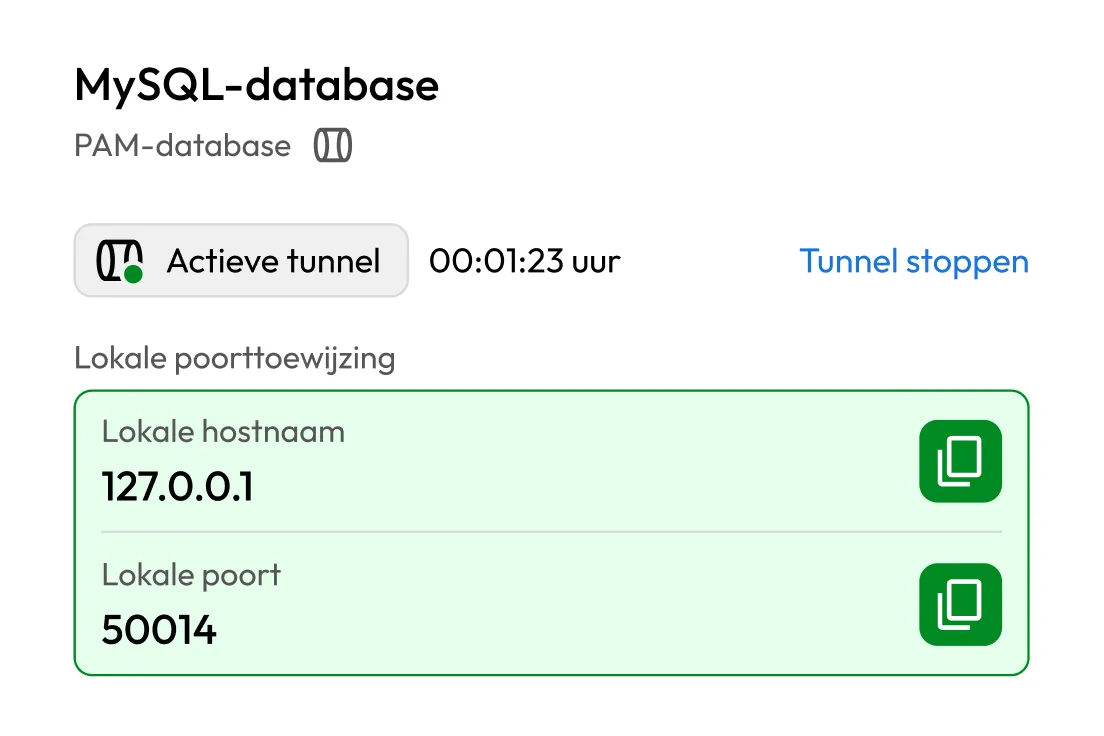
Keeper Tunneling maakt veilige toegang tot interne services en databases mogelijk via versleutelde tunnels, terwijl u de native clienttools blijft gebruiken en netwerkbronnen niet openbaar blootstelt.
Keeper Secrets Manager ondersteunt veilige toegang tot geheimen voor AI-agents via het Model Context Protocol (MCP), dat geautomatiseerde workflows mogelijk maakt terwijl zero-trust en zero-knowledge beveiliging behouden blijven.

Keeper Commander is een volledig uitgeruste opdrachtregelinterface met een interactieve supershell die veilige, scriptbare en herhaalbare workflows mogelijk maakt voor kluis- en administratieve operaties, inclusief gebruikersbeheer, rapportage, rotatie van aanmeldingsgegevens, verbindingen en tunneling.
Implementeer Keeper Commander als een zelfgehoste REST API-service om de Keeper-kluis en beheermogelijkheden te integreren met systemen van derden, met behoud van zero-knowledge encryptie.
De Keeper Admin-API biedt toegang tot gebeurtenissenlogs, compliancegegevens, rapportagestatistieken en administratieve inzichten via een flexibele REST API-interface.
MSP's kunnen de accountbeheer-API gebruiken om tenants, abonnementen, proefperiodes en gebruiksstatistieken te beheren in klantomgevingen.
MSP-partners kunnen via een speciaal API-eindpunt gratis Keeper Family Plans inrichten voor in aanmerking komende eindgebruikers.
Onderwijsinstellingen kunnen op grote schaal Keeper Student-accounts inrichten met behulp van de Student Provisioning API.
Keeper ondersteunt SCIM 2.0 voor geautomatiseerde gebruikersinrichting, intrekking, groepsbeheer, toegang tot gedeelde mappen en beleidshandhaving.

Killercoda is een interactief leerplatform dat praktische leerervaringen biedt voor veel van Keepers ontwikkeltools.
SDK's en tools voor het Keeper Security-platform: Commander CLI, Secrets Manager en integraties van derden.
De oplossingen voor verbindingsbeheer van Keeper zijn commercieel ondersteunde mogelijkheden die worden aangedreven door Apache Guacamole, ontwikkeld door de oorspronkelijke makers.
Deel uw kennis, ontdek goede gewoontes en blijf op de hoogte met exclusieve updates en inzichten rechtstreeks van het Keeper-team.
Keeper Secrets Manager levert geheimen tijdens de uitvoering met behulp van SDK's, de CLI of shelluitvoering. Geheimen worden just-in-time opgehaald uit de versleutelde kluis en in toepassingen of processen geïnjecteerd zonder dat ze hard gecodeerd worden in broncode, configuratiebestanden of images.
Nee, geheimen worden standaard nooit naar de schijf geschreven. Ze worden tijdens de uitvoering veilig opgehaald en alleen gedurende de duur van het proces in het geheugen bewaard, waarmee zero-trust en zero-knowledge beveiligingsmodellen worden ondersteund.
SDK's zijn ontworpen voor toepassingen die programmatische toegang tot geheimen binnen code nodig hebben. De CLI is ideaal voor scripts, automatisering, CI/CD-pijplijnen en operationele workflows waarbij geheimen nodig zijn zonder de toepassingscode te wijzigen.
Ja, Keeper integreert naadloos met populaire CI/CD-platforms en ondersteunt ook het gebruik van pijplijnen via de CLI en shelluitvoering. Geheimen kunnen veilig worden geïnjecteerd tijdens de uitvoering zonder ze bloot te stellen in pijplijnconfiguratiebestanden of logs.
Keeper Secrets Manager ondersteunt Java/Kotlin, JavaScript, Python, .NET, Go, Ruby en Rust. Aanvullende toegangsmethoden zijn beschikbaar via de CLI en shellintegraties.
SSH-sleutels worden versleuteld opgeslagen in de Keeper-kluis en dynamisch in geheugensessies geladen met behulp van de Keeper SSH Agent. Privésleutels worden nooit naar schijf geschreven of aan eindgebruikers blootgesteld.
Keeper ondersteunt veilige toegang tot geheimen voor AI-agents met behulp van het Model Context Protocol (MCP), waardoor agents dynamisch geheimen kunnen ophalen met behoud van zero-trust en zero-knowledge beveiligingscontroles.
U moet cookies inschakelen om Live Chat te kunnen gebruiken.