機能: SIEM統合
SIEMとのシームレスな統合で、リアルタイムの可視化と脅威対応を実現
KeeperのSIEM統合は、レポート・アラートモジュール (ARAM) を基盤に、完全な可視化、リアルタイムのアラート通知、監査対応のレポート機能を実現します。
機能: SIEM統合
KeeperのSIEM統合は、レポート・アラートモジュール (ARAM) を基盤に、完全な可視化、リアルタイムのアラート通知、監査対応のレポート機能を実現します。
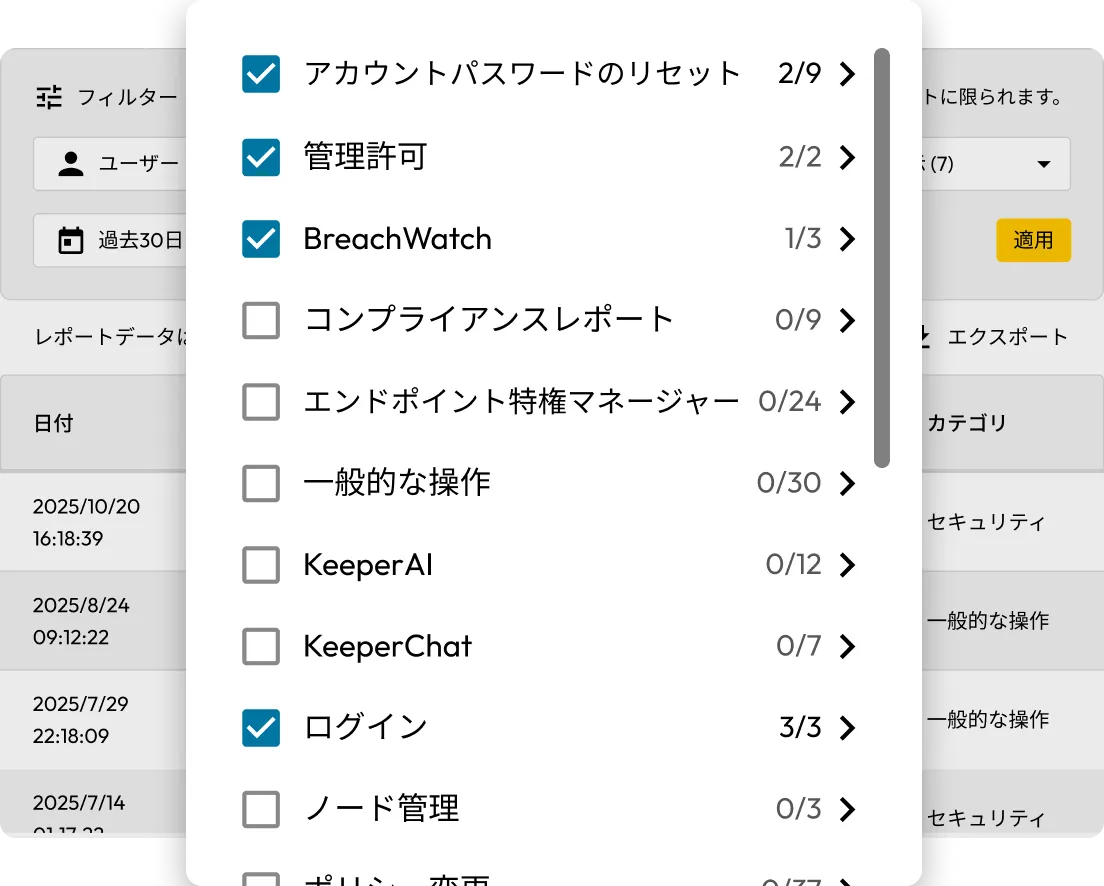
セキュリティイベント、管理用操作、特権アクセス管理 (PAM) のアクティビティなど、300種類以上のイベントを対象にカスタムレポートを作成。ユーザー、レコードUID、IPアドレス、所在地などの属性で絞り込み、重要な情報を的確に把握できます。
KeeperはServiceNow、Jira、Salesforceなどのプラットフォームと連携し、リアルタイムイベントからチケットを自動生成。ワークフローの効率化、セキュリティチームとITチーム間の連携の強化を実現します。
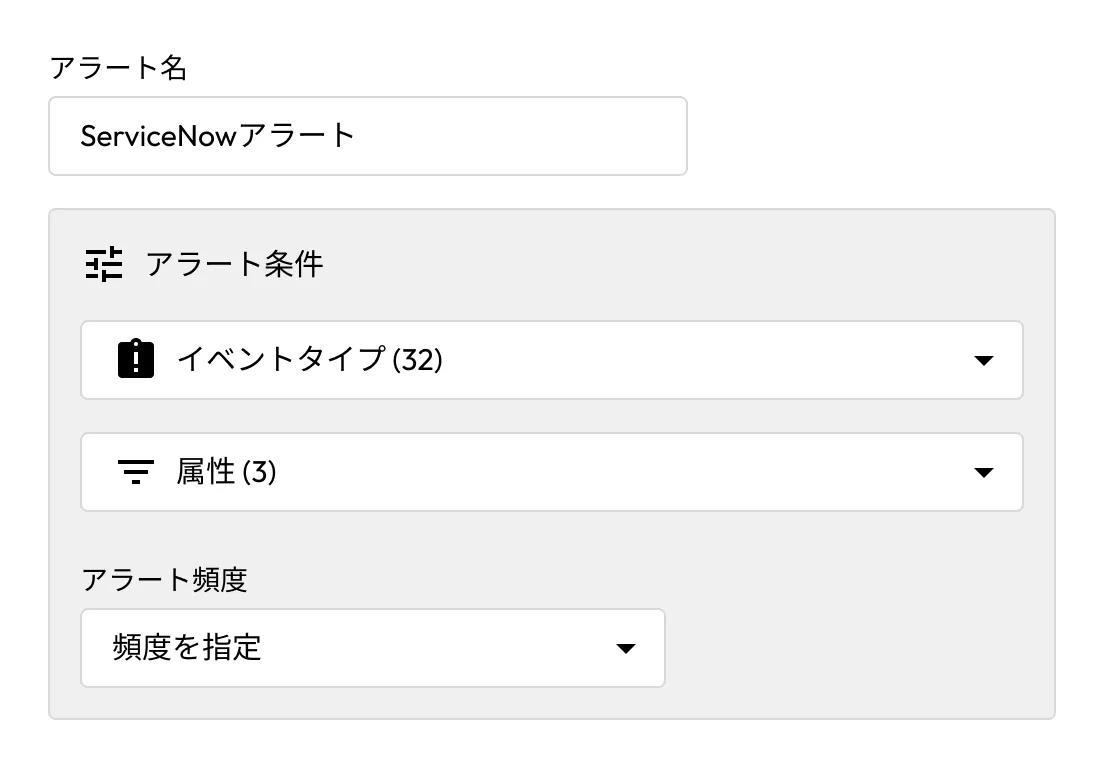
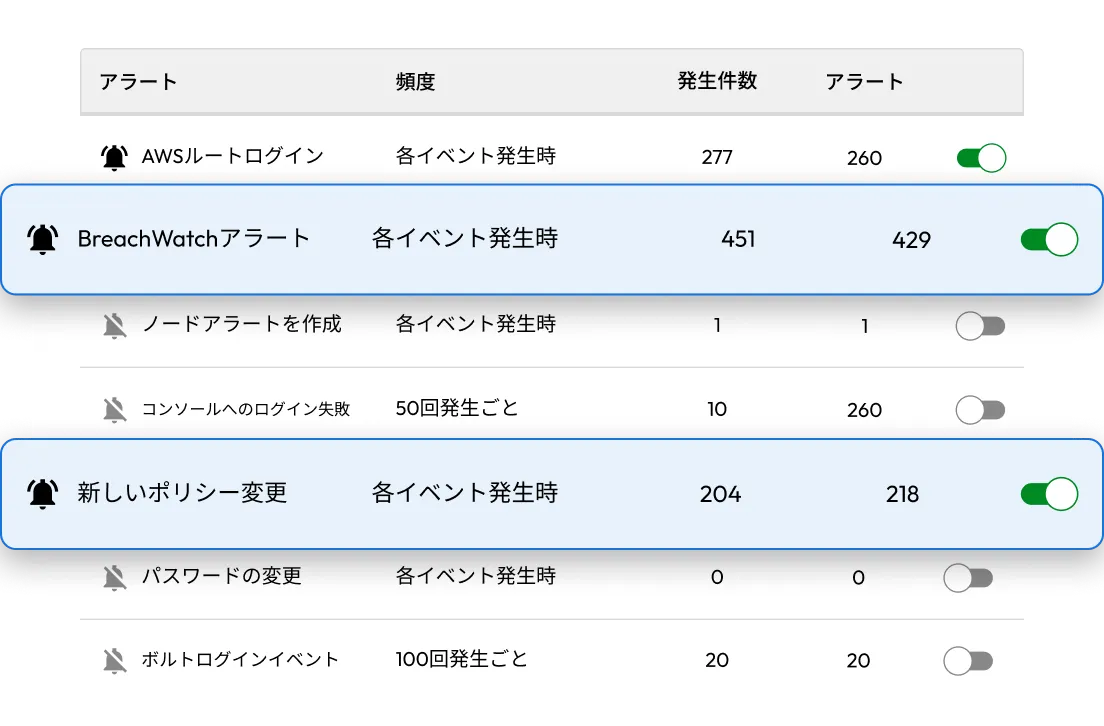
あらゆるイベントタイプに対するアラート設定と、メール、SMS、Webhookによる通知。一般的なトリガーには、ロールポリシーの変更、2要素認証の無効化、デバイス承認、BreachWatchによる検知などがあります。
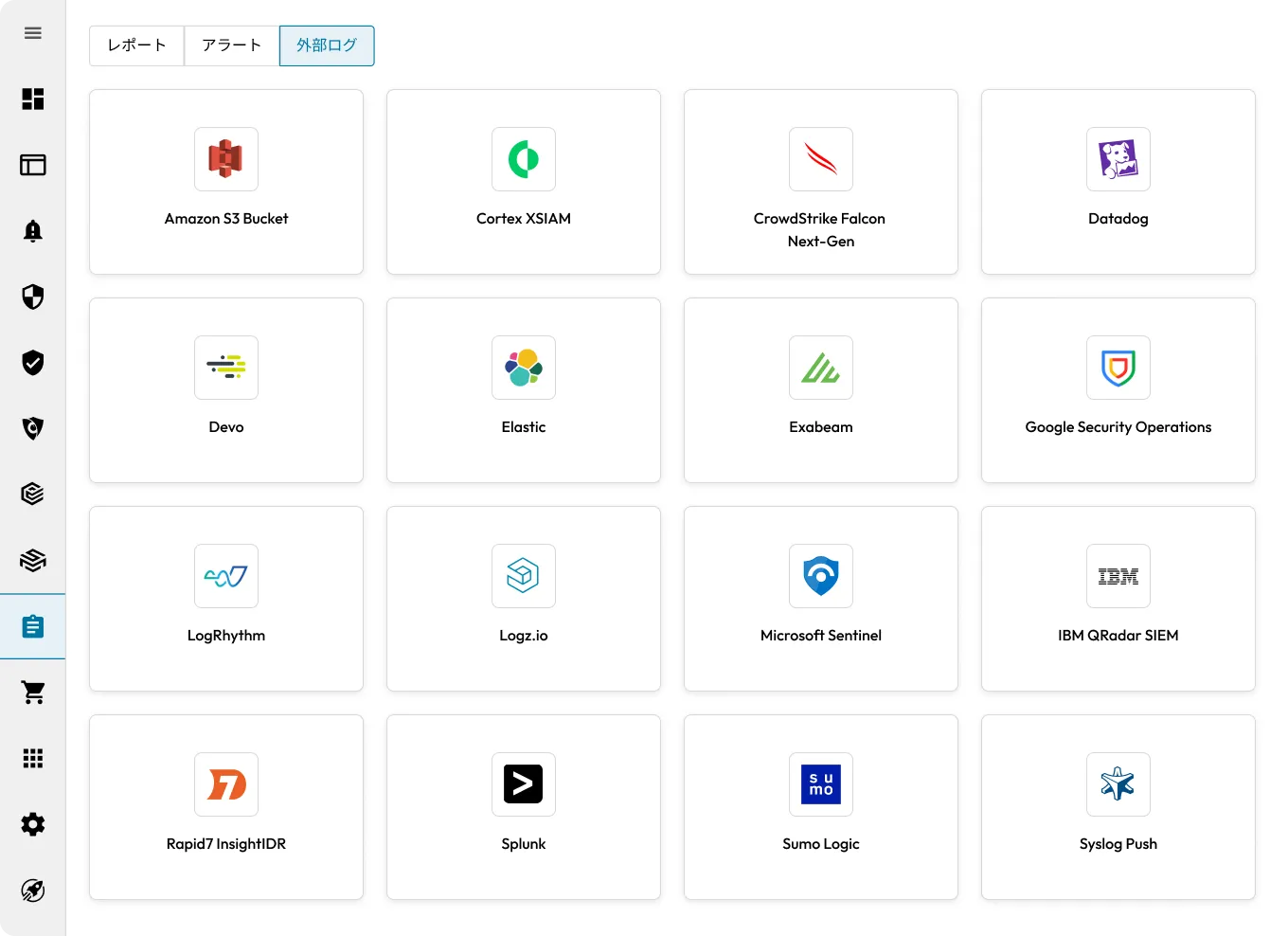
事前構築済みの統合、syslog、Webhookを利用してSIEMプラットフォームに接続。KeeperはMicrosoft Sentinel、Splunk、CrowdStrike Falcon Next-Gen SIEM、Datadog、Google Security Operations、Elastic、AWS S3などに対応しています。

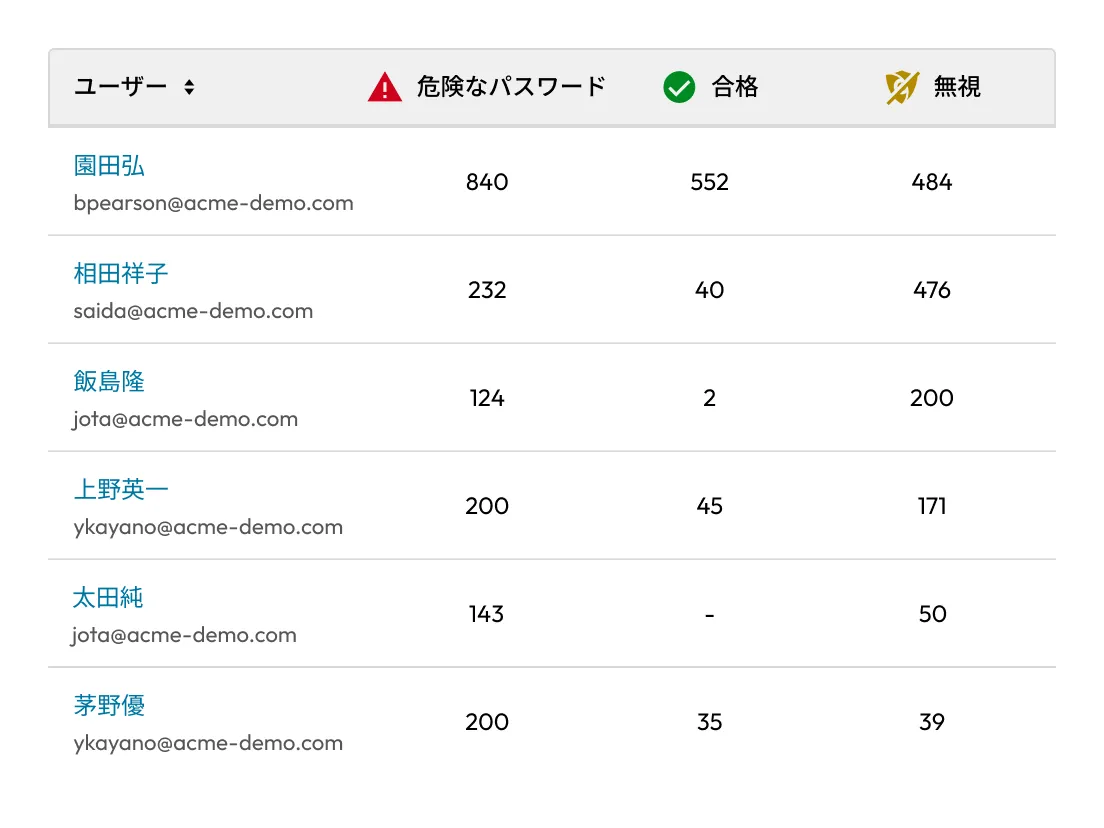
BreachWatch®アラートと対応状況を追跡し、組織全体の高リスクなパスワードを監視。このデータを活用して認証情報の管理を強化し、リスクを低減します。
Keeperコマンダーを使用してSIEMイベントデータにアクセスし、フィルタリングやカスタムレポートの作成が可能。ログパイプラインや外部システムとの連携にも対応しています。


SOX、ISO、SOC 2、HIPAAなどの各種コンプライアンス要件に対応するための詳細なアクティビティレポートを生成。監査時に必要な統制と説明責任を容易に証明できます。
いいえ。SIEM統合にはレポート・アラートモジュール (ARAM) のアドオンが必要です。KeeperPAM®をご利用の場合は、ARAMはすでに含まれています。
ログイン、パスワード変更、レコード作成、共有操作、PAMセッション開始、デバイス承認、ボルト移転など、300種類以上のイベントを記録、送信できます。
はい。KeeperのARAMを使用して、フィルタリングやしきい値の設定が可能です。
はい。すべてのイベントはメタデータのみで構成されています。ボルトの内容は暗号化されたままで、KeeperやSIEMプロバイダーからアクセスされることはありません。
Splunk、IBM QRadar、LogRhythm、Sumo Logic、Azure Sentinelなど、主要なSIEMシステムに対応しています。
チャットサポートを利用する場合、Cookie を有効にしてください。