Funzionalità: autenticazione a due fattori (2FA)
Proteggi la tua Cassaforte Keeper con un secondo livello di autenticazione
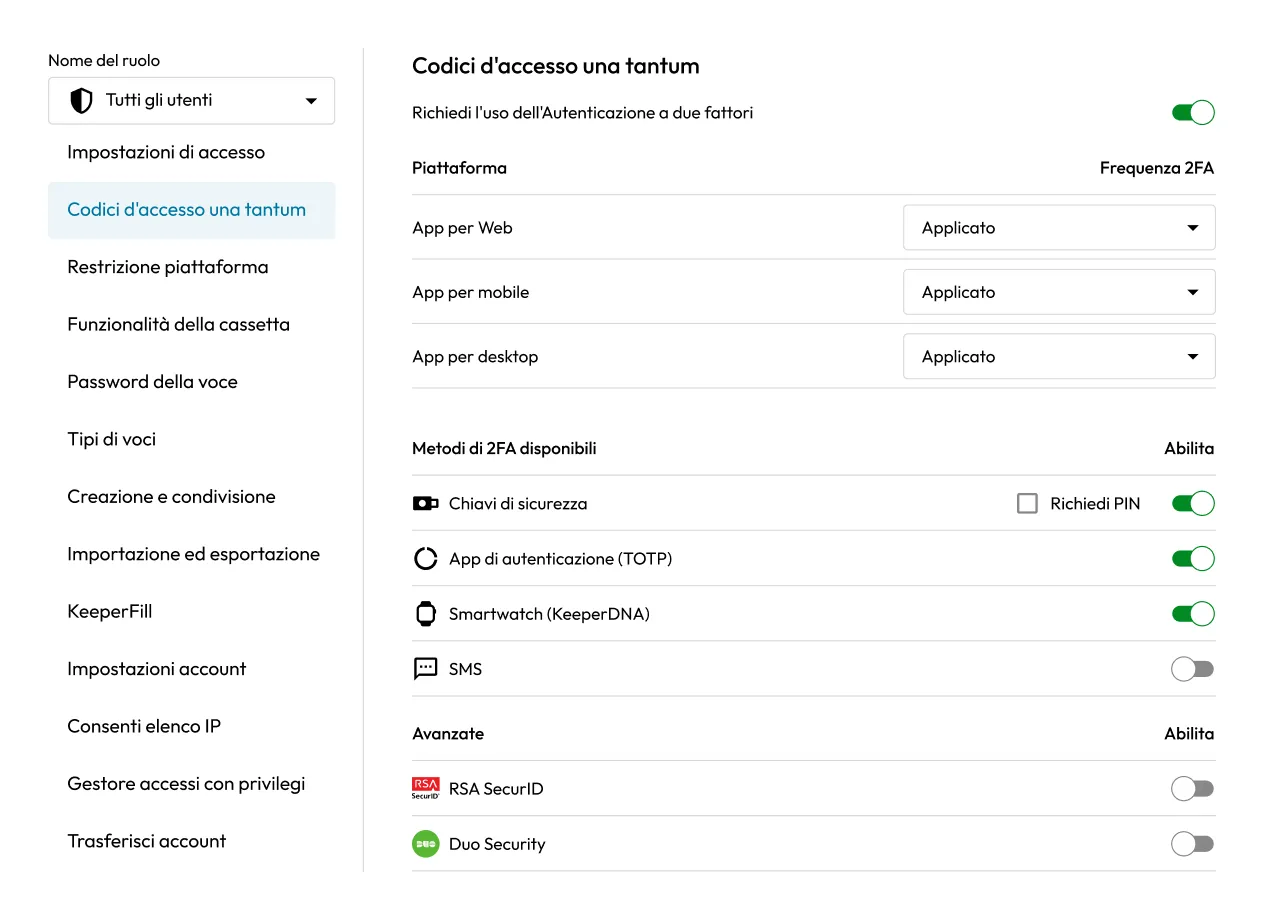
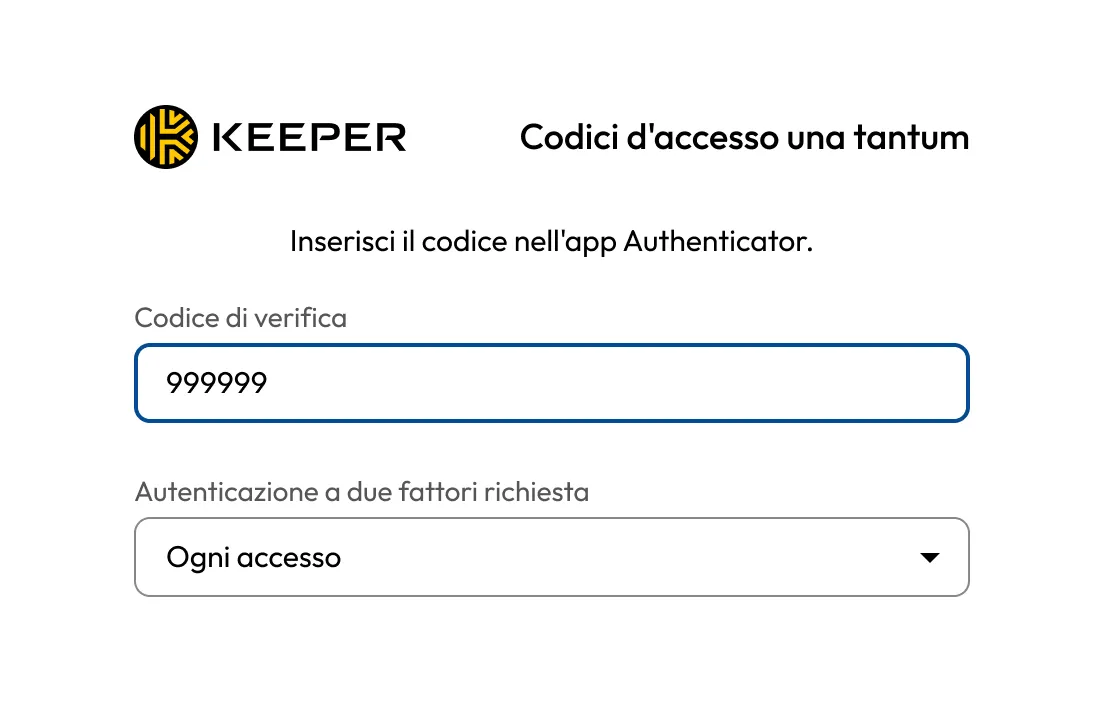
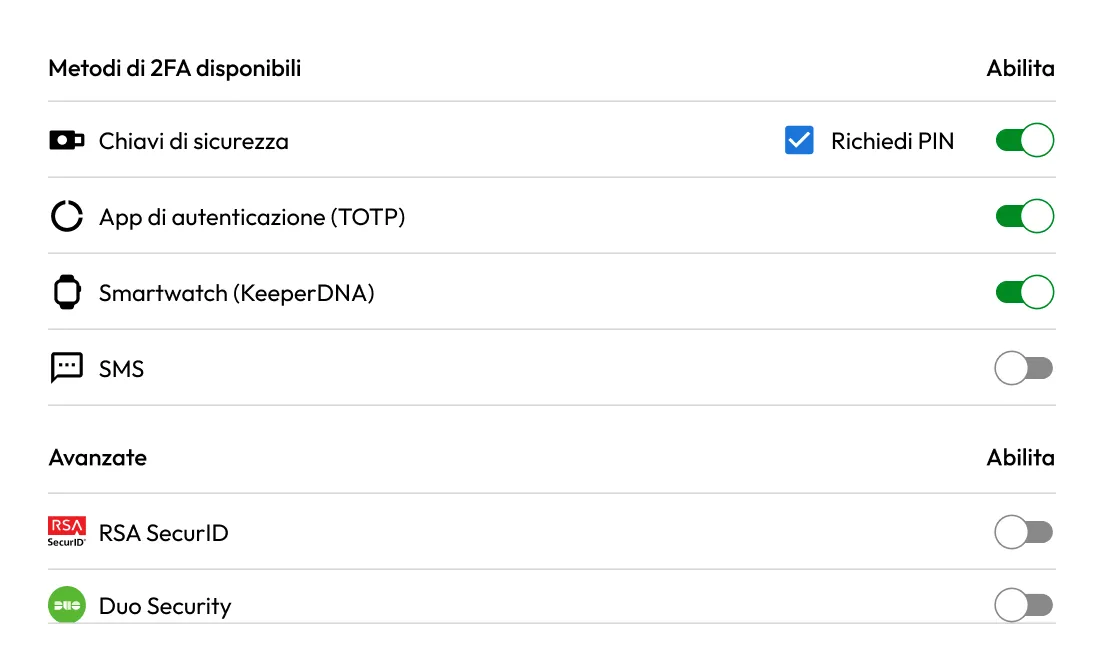
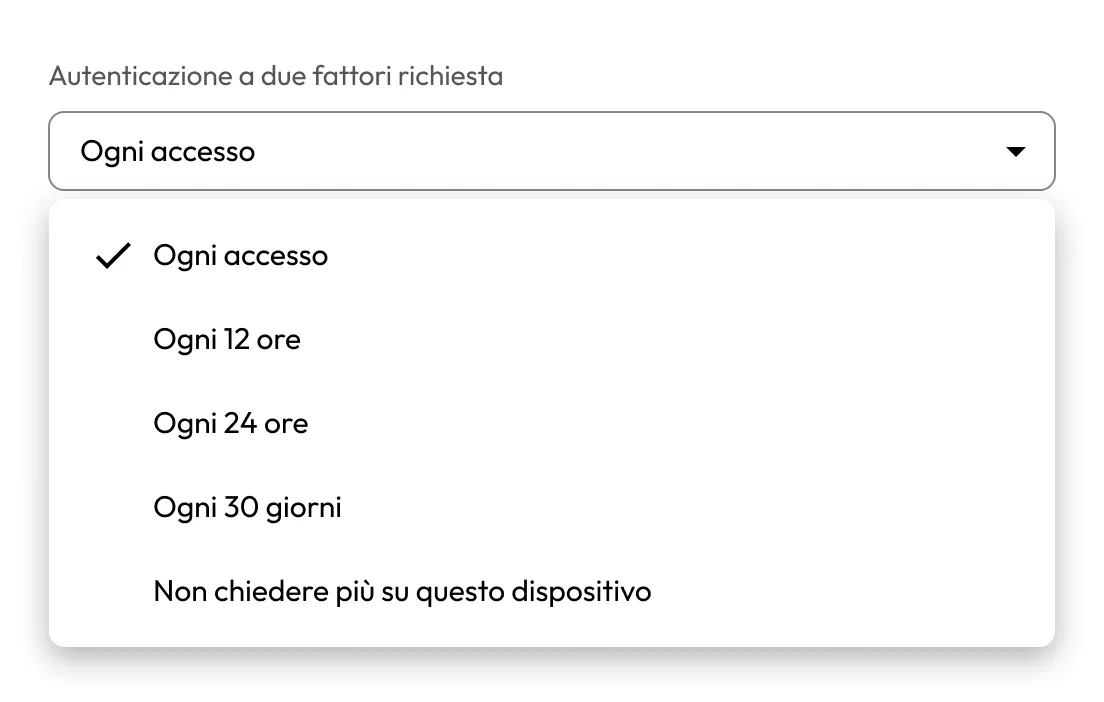
Keeper supporta diversi metodi di autenticazione a più fattori (MFA) per proteggere l'accesso alla tua Cassaforte Keeper e garantire accessi sicuri in ambienti personali e aziendali.