Keeper Security has once again been recognized by the German technology publication connect professional. In its latest independent test, Keeper Endpoint Privilege Manager (EPM) received a
KuppingerCole Analysts AG, a global information-security analyst firm, named Keeper Security a leader in its 2023 Leadership Compass – Secrets Management report based on product strength, market presence and innovation.
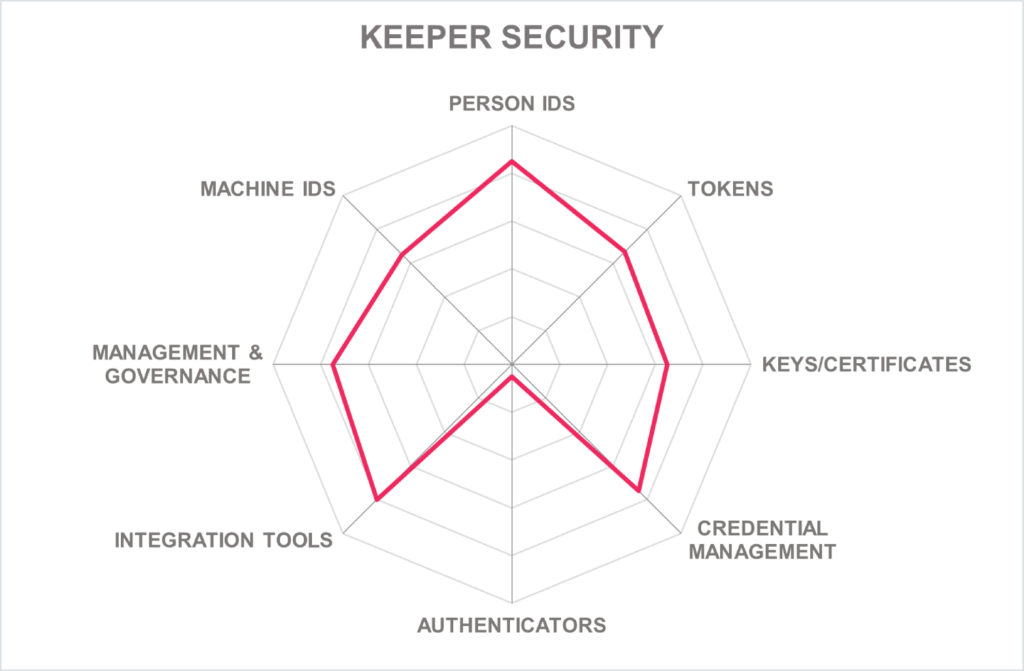
Specifically designed to fully manage and protect an organization’s cloud infrastructure with zero-trust and zero-knowledge security, Keeper Secrets Manager (KSM) was rated as a top performer in the following categories:
- Security
- Functionality
- Deployment
- Interoperability
- Usability
KSM is a cloud-based platform for securing infrastructure secrets such as API keys, database passwords, access keys, certificates and more in a zero-knowledge environment. KSM is also fully-managed, so end-users don’t have to deal with any hosted software, VPC peering requirements or additional infrastructure configurations.
Available as part of KeeperPAM™, KSM is integrated within Keeper Enterprise Password Manager’s web vault, admin console and desktop app to eliminate hard-coded secrets or secrets saved in config files.
KuppingerCole’s 2023 Secrets Management Report nomination further establishes Keeper’s position as an industry leader and innovator in cybersecurity and privileged access management.
The Importance of Secrets Management in Today’s Cybersecurity Landscape
For Development Operations (DevOps) teams, secrets refer to sensitive information that is required to be securely stored and transmitted between different stages of the software development and delivery pipeline.
Secrets include passwords, API keys, database credentials, SSH keys and other confidential information necessary for the proper functioning of the application or infrastructure. These secrets are often used to access external services or systems that are needed to build, test and deploy software.
Proper handling of secrets is critical because if these machine-to-machine credentials fall into the wrong hands, they can be used to compromise the security of an entire system. To ensure the confidentiality, integrity and availability of secrets, DevOps teams use various tools and techniques such as encryption, access controls and secret management systems.
Secrets need to be protected by strong security policies, regularly rotated and never stored in clear text. Access to secrets should be limited to only those who need them and regularly audited to ensure compliance with security best practices.
Secrets can be used in a variety of ways by cybercriminals, including:
- Credential-stuffing attacks: The use of secrets, such as passwords and API keys, to automate login attempts on multiple accounts. This is often successful because users tend to reuse the same password across different services.
- Man-in-the-middle attacks: An attempt to intercept and eavesdrop on communications between DevOps tools and systems, allowing cybercriminals to steal secrets in transit.
- Phishing attacks: The use of social engineering techniques to trick DevOps team members into revealing secrets, such as passwords or API keys, through fake login pages or other deceptive means.
- Malware attacks: The use of malware to steal secrets from DevOps tools or systems through vulnerabilities in the code or by tricking team members into installing malicious software.
- Insider threats: Attacks by individuals who have legitimate access to DevOps secrets. This can include bad actors who steal secrets for personal gain or accidental leaks by team members who are not following security best practices.
Who Is KuppingerCole and How Do They Evaluate Vendors?
KuppingerCole is an independent analyst firm specialized in providing research, advisory and consulting services in the areas of Identity and Access Management (IAM), cybersecurity, as well as Governance, Risk Management and Compliance (GRC).
KuppingerCole offers a wide range of services to clients worldwide, including market research, vendor evaluations, strategy consulting, implementation support and training. The firm leverages its expertise in the field of IAM to publish reports and market studies.
Its most recent 2023 Leadership Compass – Secrets Management report conducted a detailed report that compared leading solutions for secrets management, recognizing Keeper as an Overall Leader in secrets management.
The solutions named Overall Leaders are identified based on a combined rating that looks at the strength of product, market presence and innovation of the vendor.
KuppingerCole rates the vendors themselves on innovativeness, market position, financial strength and ecosystem. The report listed the following strengths for Keeper Security:
- Fusion of password management and privileged access management
- High assurance solution with full encryption of communication
- Strong DevOps support
- Comprehensive go-to-market strategy
- Partner network for market coverage
What Separates KSM From Other Secret Management Solutions?
KSM operates as a cloud-based platform, securing infrastructure secrets such as API keys, database passwords, access keys, certificates and any type of confidential data.
The platform is fully managed, easy to deploy, has no hosted software, no complex VPC peering requirements and requires no new infrastructure to configure.
Keeper is the only password manager that uses Elliptic Curve Cryptography in its encryption with zero-trust and zero-knowledge security so that only end-users can access their vault. Secrets can only be decrypted at the device level. The front-end systems’ source code is open-source and publicly viewable.
KSM’s other key features include:
- Simple vault interface in a GUI and CLI
- Access to secrets from the source code
- Centralized admin console with RBAC
- Logs, reports, alerts, SIEM integration and compliance reporting
Request a demo of Keeper Secrets Manager today to see how to secure your environment and eliminate secrets sprawl.


