Employees are adopting AI tools, agents and automations faster than organizations can govern them. The real danger emerges when these tools connect directly to internal systems
A watering hole attack is a type of cyber attack in which a threat actor targets an organization by hacking a website often visited by an employee in order to infect the employee’s device with malware. Once the device of one employee is infected, the threat actor targets other members of the organization and steals their confidential information.
Although watering hole attacks are uncommon, they pose a considerable threat since they are difficult to detect and can put an entire organization at risk of a security breach. These threat actors target employees who are negligent with their cyber hygiene. However, watering hole attacks can be easily avoided by implementing cybersecurity best practices.
Continue reading to learn more about how watering hole attacks work, the signs to look out for and how to prevent them.
How Does a Watering Hole Attack Work?
Watering hole attacks got their name from the hunting technique in which predators would hide around popular watering holes that their prey tend to go to and wait until their prey let their guard down to attack. Threat actors do the same thing with watering hole attacks by targeting niche websites with weak security and waiting until a user visits the hacked website to infect their device with malware.
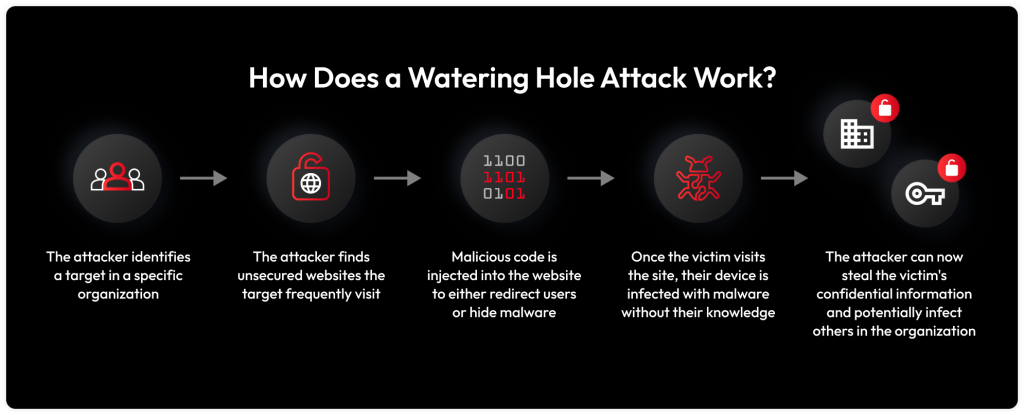
A threat actor starts their watering hole attack by researching and identifying a target. The target is someone who practices poor cyber hygiene and is part of a broader organization or company the attacker ultimately aims to infiltrate. Once the attacker determines their target, they gather intelligence to find any niche and unsecured websites their target often visits, such as discussion boards.
The attacker then looks for security vulnerabilities within the website to inject malicious code such as Javascript or Hypertext Markup Language (HTML). This malicious code either redirects the user to a spoofed website or hides malware in the original website. The attacker then waits for the victim to visit the website to infect their device with malware. Once the victim’s device is infected, the threat actor can steal the victim’s confidential information and infect other members of the victim’s organization as well.
Signs of a Watering Hole Attack
Watering hole attacks can be very difficult to detect until they have taken effect and spread to other devices and employees. However, if you are aware of the signs, then you can detect if a website or your device has been compromised. Here are the signs to look out for:
Increase in emails from niche websites
Sometimes, threat actors try to lure their victims to the compromised site the victim often visits or a spoofed version of that site. If you are noticing an increase in emails sent to you by niche websites you have often visited in the past, that could be a sign that a bad actor is trying to target you with a watering hole attack.
Poor computer performance
If you notice a dip in computer performance such as quick battery drainage, slow loading times, constant crashes or frequent error messages, this may be a sign that you have experienced a watering hole attack and your device has already been infected with malware.
Constant pop-ups
Constant pop-ups of ads or messages pushing you to download files or visit a website are a sign that an attempted watering hole attack is taking place. The goal of these pop-ups is to urge you to visit the compromised website which will install malware on your device.
Changes to security settings in your browser
One way to tell if a cybercriminal is targeting you with a watering hole attack is by checking for changes to the security settings in your browser. Cybercriminals try to change your browser security settings to allow the installation of malware without your knowledge and to keep it undetected once installed.
New downloaded applications
If your device has downloaded new applications that you do not recognize or did not download yourself, then your device may have been infected with malware from a watering hole attack. These newly downloaded applications can be used to steal your data without your knowledge.
Missing files
Missing files can be a sign that your device has been infected with malware from a watering hole attack. Some malware such as ransomware may be stealing, altering or encrypting your files to sell back to you or sell for profit on the dark web.
How To Prevent Watering Hole Attacks
The best way to deal with watering hole attacks is to protect yourself from them. Here are some ways to prevent watering hole attacks.
Use advanced protection solutions
Antivirus software is a tool that monitors, detects and removes malware from your device. You should use advanced protection solutions such as antivirus software to help protect your devices from installing malware from compromised websites. You can also install more advanced threat protection solutions such as anti-malware software, which uses machine learning to detect and remove new malware.
Monitor internet traffic
You should monitor your internet traffic for any suspicious activity to prevent watering hole attacks. Using antivirus software ensures your traffic is being monitored and will notify you of any potentially harmful websites. You should only visit secure websites with HTTPS in the URL and avoid third-party websites to prevent watering hole attacks.
Use a VPN
A Virtual Private Network (VPN) is a service that protects your internet connection and online activity by masking your Internet Protocol (IP) address and encrypting your data. A VPN can hide your online activity from threat actors, preventing them from targeting you and learning about your online behavior.
Keep your software up to date
Keeping your software up to date can help prevent watering hole attacks by patching known security vulnerabilities. Updating your software will offer another layer of protection against the installation of malware from hacked websites.
Don’t overshare online
Threat actors that execute watering hole attacks are looking for information about you to learn about your interests and online behavior so they can find websites you often visit. You should avoid oversharing online to prevent threat actors from learning about you and to protect yourself from watering hole attacks.
Stay educated about cyber threats
One of the best things you can do to prevent watering hole attacks is to educate yourself about cyber threats and learn how to recognize them. Always be on the lookout for cyber threats and implement cybersecurity best practices to protect yourself and your organization.
Stay Safe From Watering Hole Attacks
Watering hole attacks are scary to deal with since they are difficult to detect until they have already taken effect and your device is already infected. If you feel like your device has been infected with malware from a watering hole attack, then you should get rid of the malware infection right away to protect yourself and your organization.