In modern enterprise environments, identity has become the primary attack vector, but many organizations lack visibility into who has privileged access and whether that access is
User Insights on Cost and Complexity – Research finds traditional PAM solutions are too complex with 68% of organizations paying for wasted features.
Keeper Security and TrendCandy Research surveyed over 400 IT and security professionals to explore the common challenges that organizations face with their current Privileged Access Management (PAM) solutions. The results are conclusive. Not only are major components of traditional PAM solutions not being used, but many respondents admit to never fully deploying the solutions they paid for.
This report was commissioned to gain insights and data on feedback that we’ve heard from countless IT and security professionals – that traditional PAM solutions are overly complex, costly and difficult to maintain. Our research clearly demonstrated that most of these traditional PAM solutions are falling short.
User Feedback – PAM Solutions are Falling Short
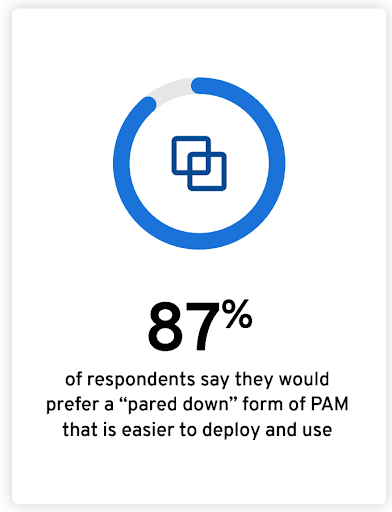
PAM users indicate that the desire and need for a simple solution is pervasive. Some findings include:
- 87% of respondents say they would prefer a “pared down” form of PAM that is easier to deploy and use.
- On average, IT teams only use 62% of their current PAM functionality. 58% of respondents agree there is waste in their PAM solution.
- Roughly two-thirds of survey respondents indicate that pricey and superfluous PAM features create too much complexity for users, reducing user satisfaction.
- More than half of all IT teams – 56% – report they tried to deploy a PAM solution but never implemented it. Of those, 92% said it was because their PAM solution was too complex.
- Most organizations – 85% – say their PAM product requires a dedicated staff to manage and maintain.
- Two-thirds of IT leaders – 66% – say they need a better PAM solution, but 58% say they do not have one because it is too expensive.
Top Five Benefits of a Simplified PAM Solution
With the current, ever-changing security climate, it is essential that all organizations have the right controls in place. This includes privileged password management, secrets management and session management.
Based on the survey results, the top five benefits IT leaders seek in a PAM solution include:
- Managing and monitoring privileged user access
- Protecting against compromise of privileged credentials by external threat actors
- Preventing data breaches
- Protecting against accidental or deliberate misuse of privileged access by company insiders
- Ensuring privileged user access is updated to prevent “privilege creep”
Respondents also shared the top five benefits of a simplified PAM solution:
- Easier to deploy
- Easier to integrate into other systems
- Cost savings
- Consolidated platform
- Requires less staff
Introducing KeeperPAM
Keeper Security’s next-generation solution unifies the most important elements of an effective and simple-to-use PAM platform. The Keeper privileged access manager solution includes Keeper Enterprise Password Manager (EPM), Keeper Secrets Manager (KSM) and Keeper Connection Manager (KCM).
- EPM enables organizations to securely manage, protect, discover, share and rotate passwords with full control and visibility to simplify auditing and compliance.
- KSM delivers a fully-managed, cloud-based solution to secure infrastructure secrets such as API keys, database credentials, access keys and certificates.
- KCM provides an agentless remote desktop gateway for instant privileged session management, remote infrastructure access and secure remote database access to RDP, SSH keys, database and Kubernetes endpoints – no VPN required.
To learn more about KeeperPAM, visit our web page and request a demo today.


