With the release of Desktop and Web Vault Update 17.4, Keeper Security’s desktop app is now available on the Linux Snap Store, bringing zero-trust, zero-knowledge password
Cyber attacks on small and medium-sized businesses (SMBs) are rising globally, and attacks are becoming more complex and targeted. To bypass intrusion detection systems and other technical security defenses, cybercriminals are using social engineering schemes to steal employee login credentials.
In addition to stealing sensitive employee and customer data, installing ransomware and other malware, and destroying files, cybercriminals can use stolen email and password combos to take over enterprise email accounts and launch a highly sophisticated form of phishing scheme known as Business Email Compromise (BEC). Also known as email account compromise (EAC), BEC scams have grown by over 100% since 2016, with aggregate global losses exceeding $26 billion and rising.
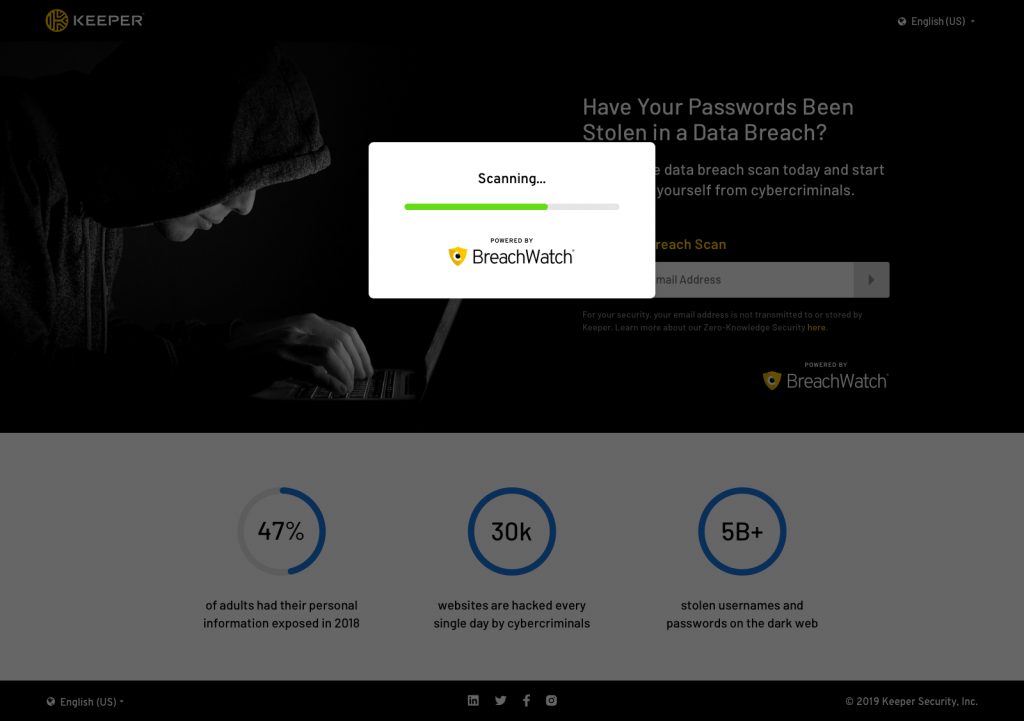
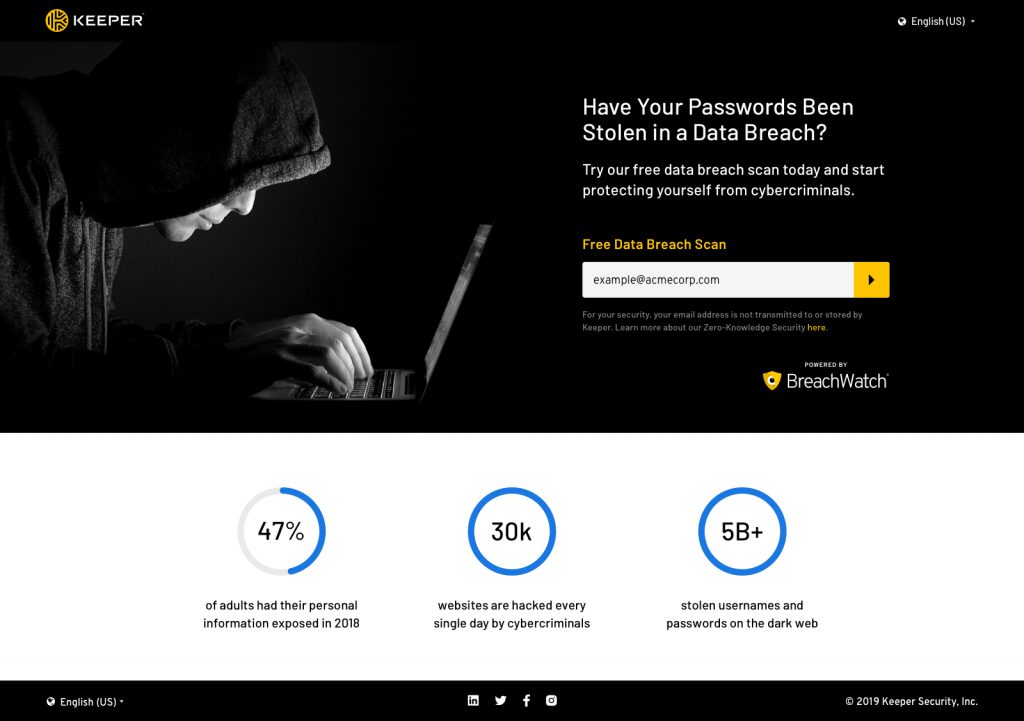
Have your business email addresses or domain-level password records been exposed in a public data breach? Find out for FREE right now.
Over 5 billion stolen usernames and passwords are up for sale on the Dark Web. Do any of them belong to your business? How can you be sure? On average, it takes organizations 101 days to discover their systems have been compromised; cybercriminals were inside Marriott Starwood’s reservations system for nearly four years before detection.
The risks are simply too great to play a wait-and-see game, especially since you can find out right now using Keeper’s FREE data breach scan tool for businesses. Powered by Keeper’s BreachWatch®, this tool is truly free, with no account sign-up required. Simply provide your business email, and we’ll tell you if that email has been exposed in a breach. Additionally, you’ll receive domain-level breach details, including the most recent date that a record from your business domain was breached.
How does it work?
The Data Breach Scan is powered by Keeper’s BreachWatch® for Business service, a self-contained managed service operated by Keeper on Amazon AWS, which is physically separate from the Keeper Backend API and stored user data. Breach Watch for Business constantly scans business user emails and alerts companies if any of their employees’ passwords have been stolen in a data breach.
On the BreachWatch® servers, a physical hardware security module (HSM) is used to process, hash, and store billions of unique passwords from dark web data breaches. Each of these billions of passwords is processed on Keeper’s servers using the HMAC_SHA512 hashing method, hashed with an HSM using a non-exportable key.
The BreachWatch® backend architecture was built to prevent the correlation of a breached password to an actual password in a user’s vault, no matter the size of the data breach. The hashing used in the breached password detection utilizes a physical HSM to ensure that hashing can only be performed online – to prevent any threat of brute force attack on the BreachWatch® data. For additional security and encryption details, visit our documentation portal.
Keeper Security is a SOC 2 and ISO27001 certified company.
Privacy
Other “dark web scan” products may use untrusted data sources. Keeper does not and will not share or leak any user information or vault data with any 3rd party.
Ease of use
Only an email address is required to perform the scan and receive the summary results. You may use the tool to scan an unlimited number of business email addresses.
If you choose to sign up for a BreachWatch for Business paid subscription, you will be able to see the actual breached websites and the dates they were breached. Additionally, you will be able to correlate the Free Breach Scan results directly to your stored Keeper vault passwords.


